Sabitlenmiş Tweet
Ronin
1.4K posts

Ronin retweetledi

[BLOG]
This post summarises how to tie Cobalt Strike's UDRL, SleepMask, and BeaconGate together for your syscall and call stack spoofing needs.
rastamouse.me/udrl-sleepmask…
English
Ronin retweetledi

Goad v3 merged into the main branch 🥳
Github : github.com/Orange-Cyberde…
Doc : orange-cyberdefense.github.io/GOAD/

English
Ronin retweetledi

In a somewhat recent project we used a vulnerable driver, which worked fine...
Except: The customer had a custom rule that caused an alert when a service is created!
Decided to write a tool that creates the registry keys and calls into NtLoadDriver: github.com/ioncodes/Silen…
English
Ronin retweetledi

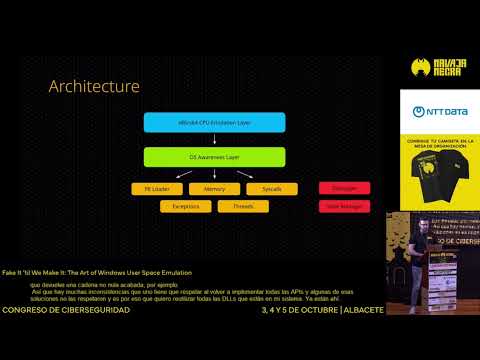
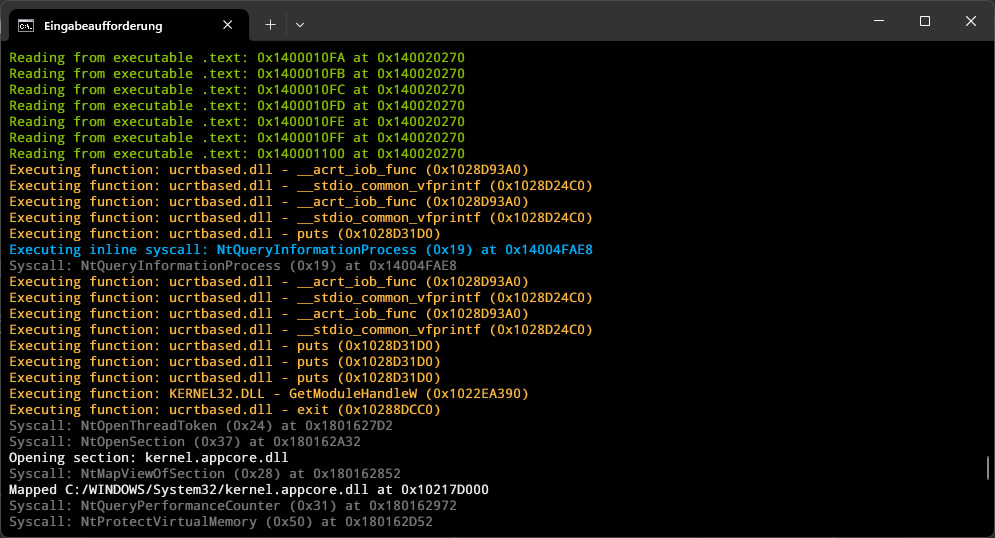
Windows User Space Emulator : A high-performance Windows process emulator that operates at the syscall level, providing full control over process execution through comprehensive hooking capabilities :
Fake It 'til We Make It : The Art of Windows User Space Emulation : youtube.com/watch?v=Y6NXwI…
Slides : #slide=id.p1" target="_blank" rel="nofollow noopener">docs.google.com/presentation/d… credits @momo5502
YouTube
English
Ronin retweetledi
@hardwaterhacker Been waiting a while to get my own invite. Looks like those were used. Suppose I can wait moar. 🤣
English
@HackingLZ I think it’s fair game if the device is used in the organization in some way.
English