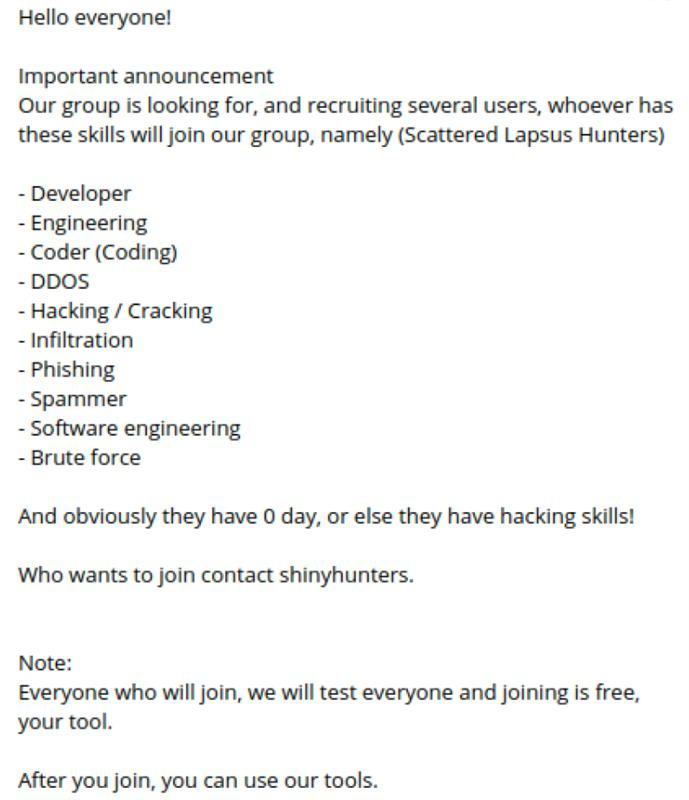
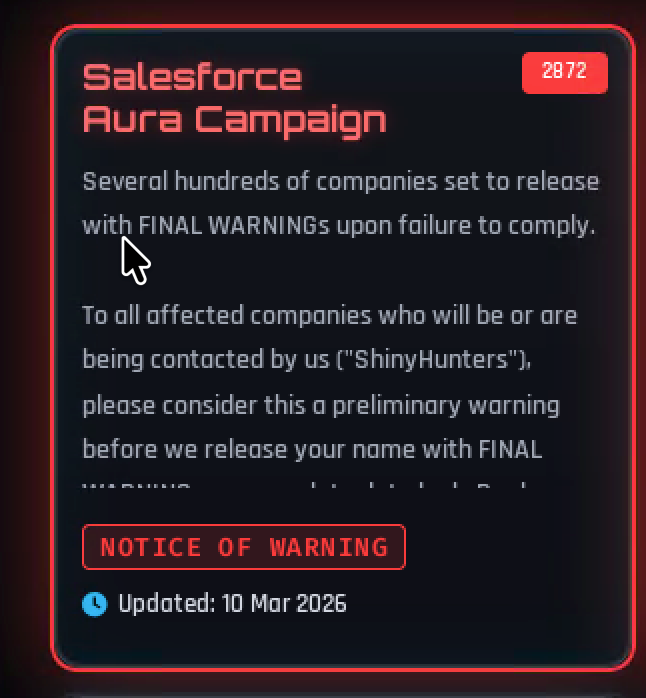
ShinyHunters is likely firing up another Zendesk campaign 🎯
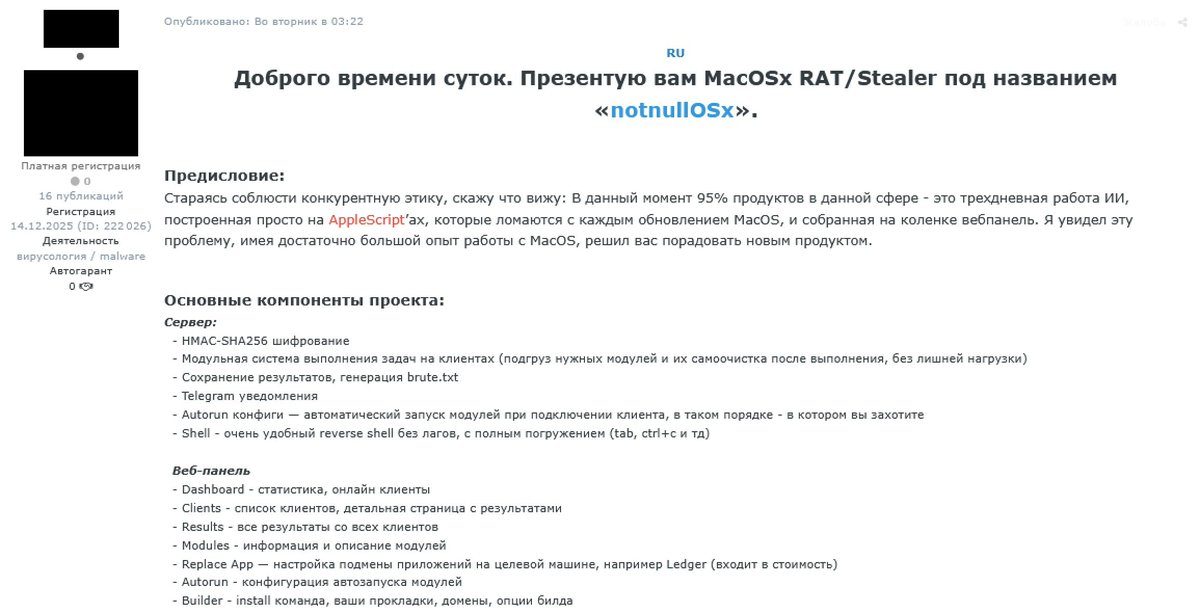
Over the past two months, ReliaQuest has identified 60+ newly registered domains impersonating #Zendesk support portals. These domains follow the pattern [brandname]zendesk[.]com and target organizations across financial services, SaaS vendors, and other high-value sectors.
#ShinyHunters is building at scale by embedding trusted brand names directly into malicious domains to increase their legitimacy. Combined with valid TLS certificates, these sites appear authentic in browsers and email clients, making credential harvesting significantly more effective.
For security teams: monitor email gateways for these domain patterns, watch for Zendesk subdomain abuse in authentication logs, and educate users that legitimate Zendesk support portals will never use third-party domains containing "zendesk" in the URL structure. Authentication attempts from domains matching [anything]zendesk[.]com should be treated as high-priority alerts.
English