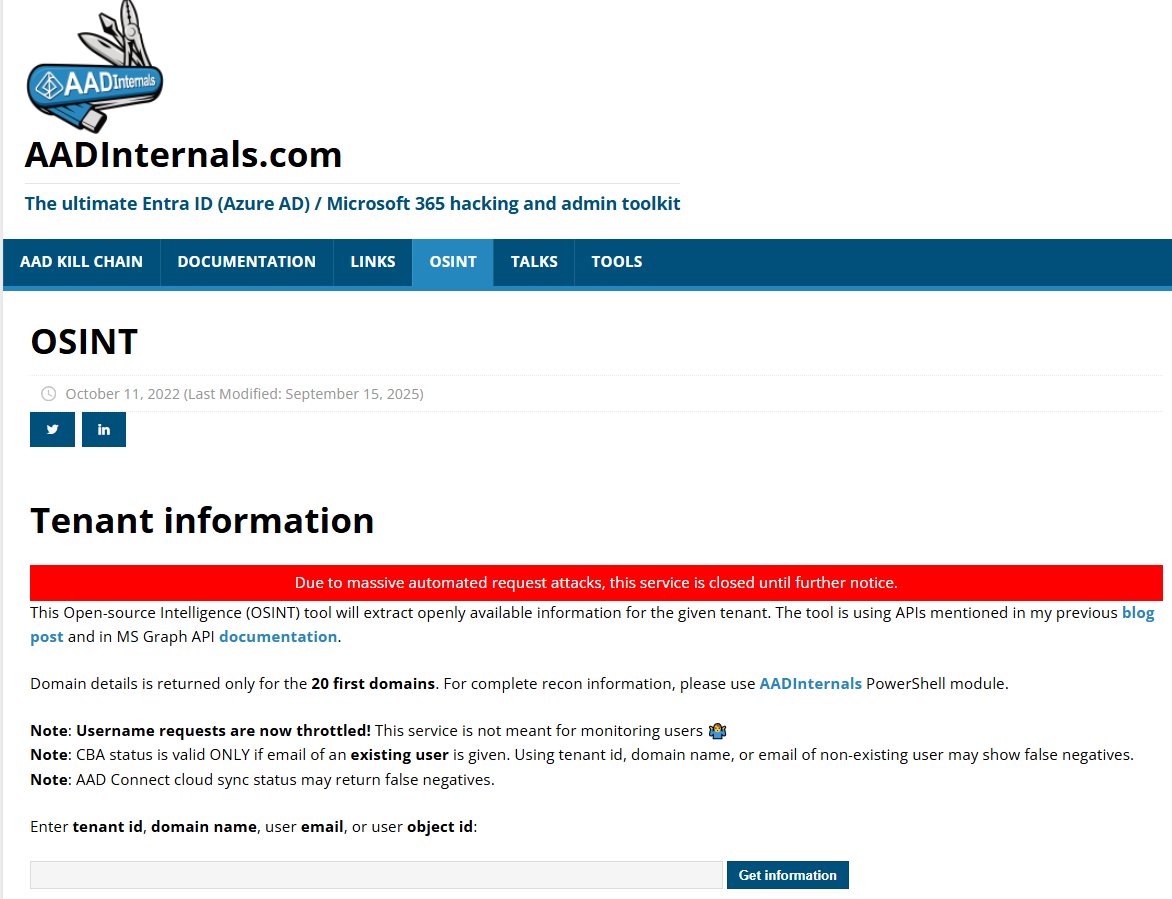
@IAMERICAbooted @_dirkjan even 1m$ is complete peanuts compared to what he could of got
English
repo flex
364 posts










SK Telecom stated that the allegedly leaked data being sold by a hacking group is "fake," following reports of a massive data breach. #SKTelecom #DataBreach en.yna.co.kr/view/AEN202509…





I’m going to have nightmares tonight about LockBit 5.0 if I ever manage to fall asleep 💀