We reported a total of 51 bugs (low to critical impact) for IoT devices used by Singapore Smart City and Smart Building.
event.ntu.edu.sg/SPIRITCYBER-24

English
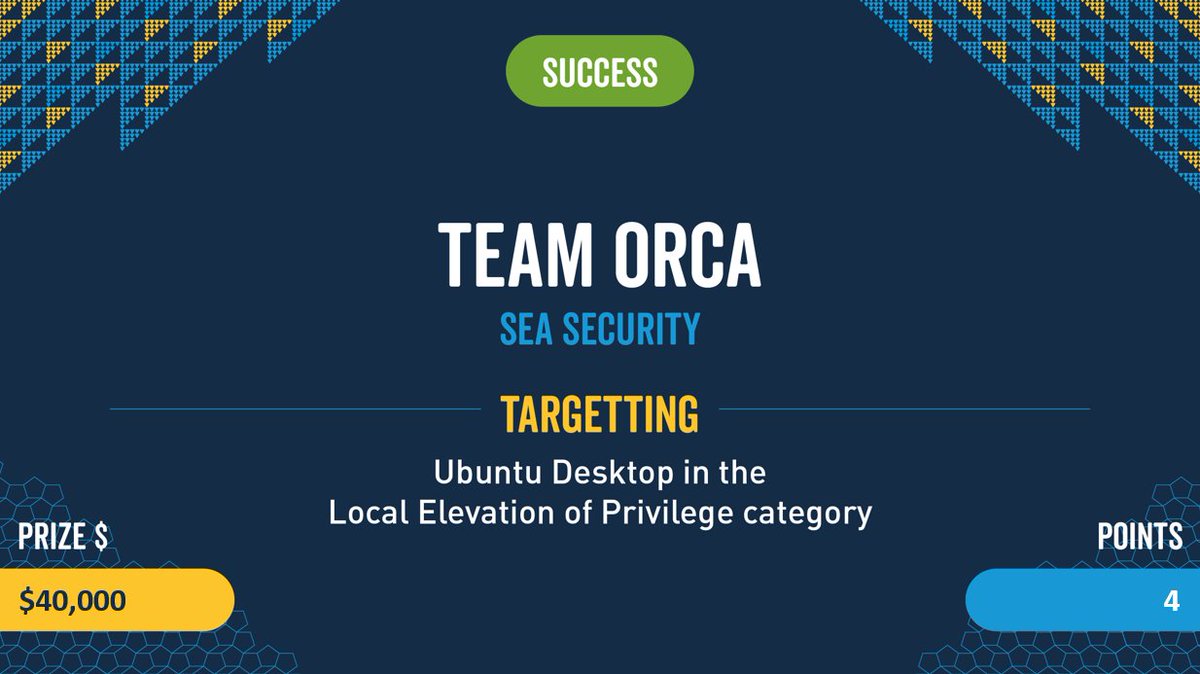
Sea Security Response
25 posts

@Seasecresponse
We are the Sea Security Response Center. To know more about us, visit https://t.co/fuq7Alrq40.