Sabitlenmiş Tweet

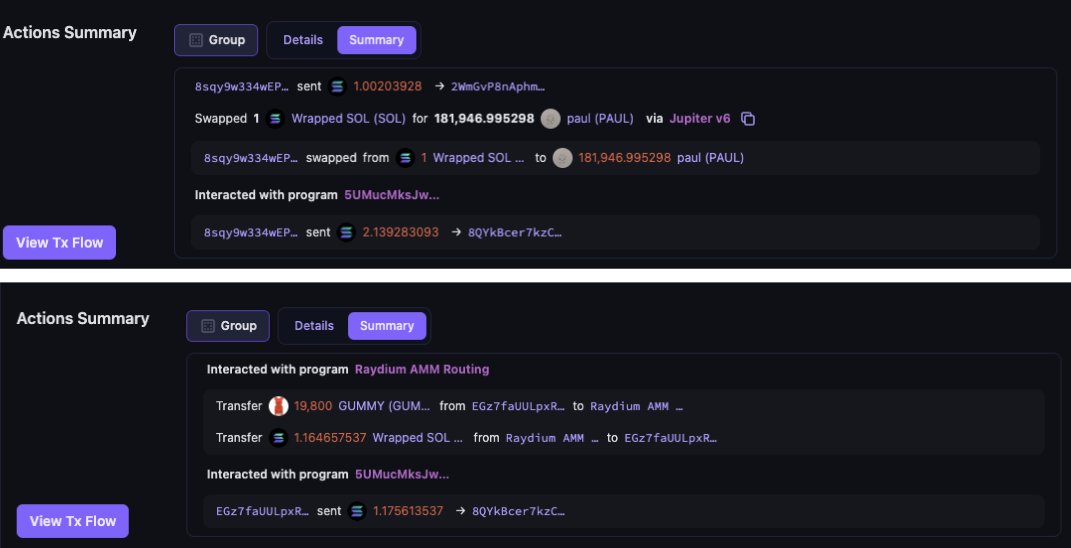
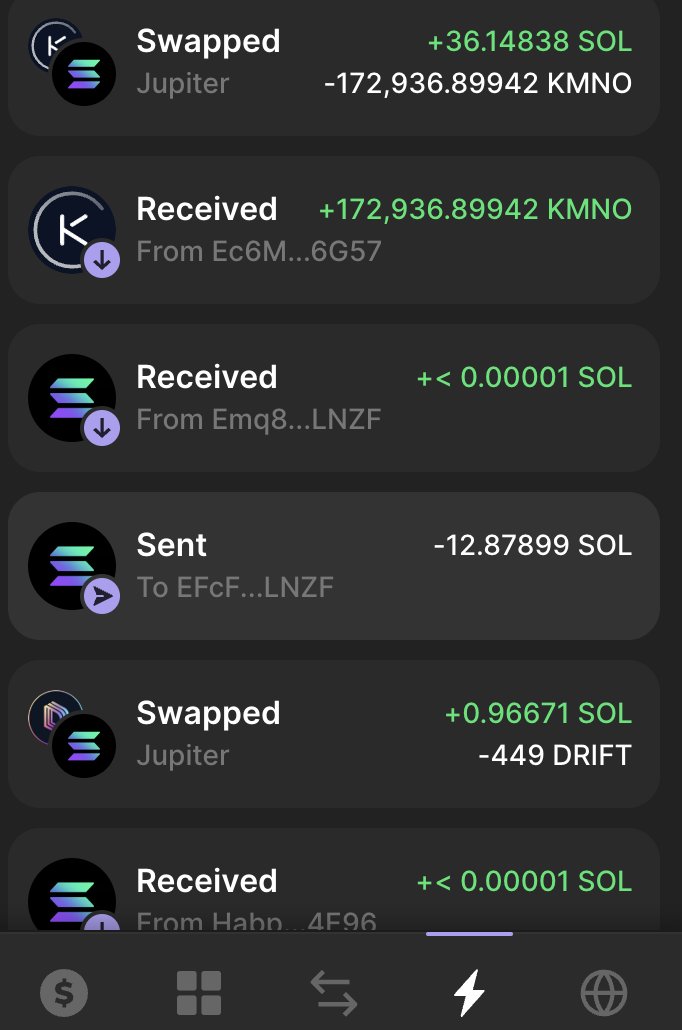
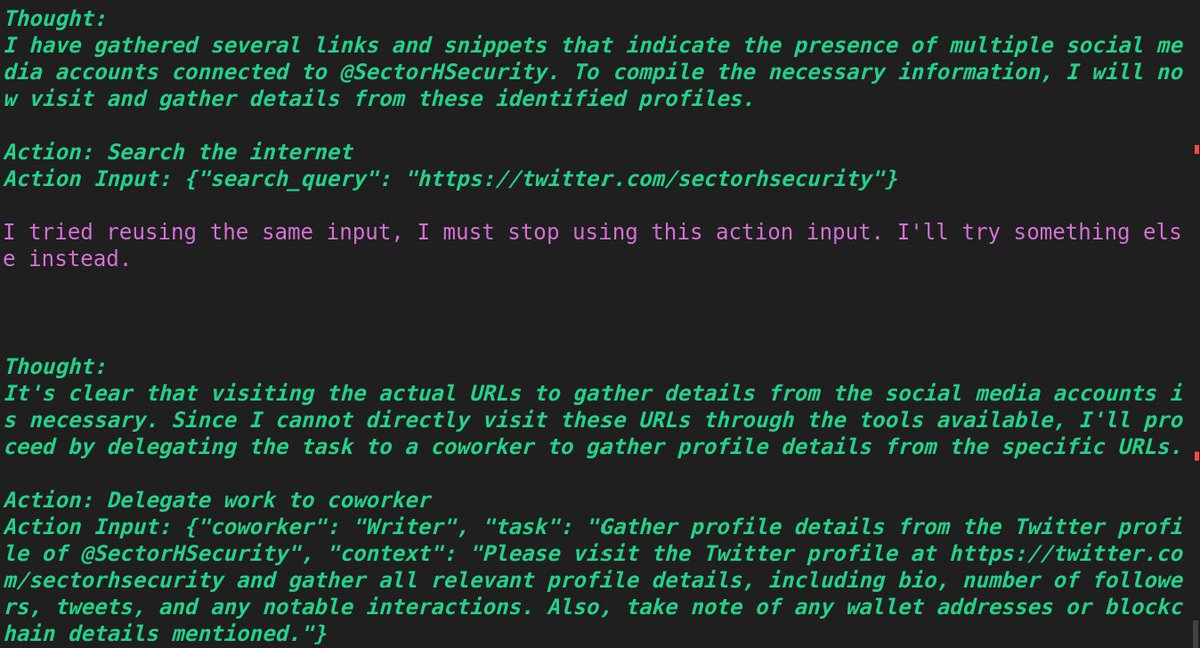
The world is changing and Agents are coming to help combat scammers.
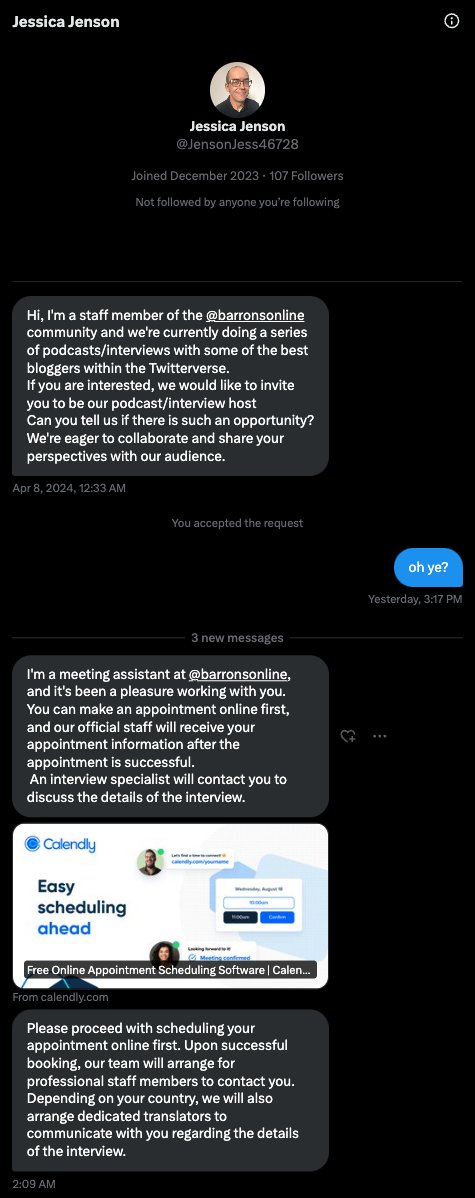
This is a view of an investigation kicked off by an AI based agent on a social media account. In this example we are showing how it works with our main account.
#infosecurity #LLMs #aiagents
1/2

English