Sabitlenmiş Tweet

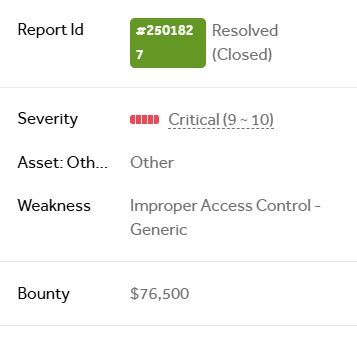
In May this year , I, along with @M_Zeeshan899, found our biggest bug with our biggest bounty on @Hacker0x01. The bug was quickly fixed and awarded with a bounty of 76500$ .
The bug was similar to what nahamsec has explained in his video youtu.be/KfoOl8RhlhQ

YouTube
English
















