Sabitlenmiş Tweet
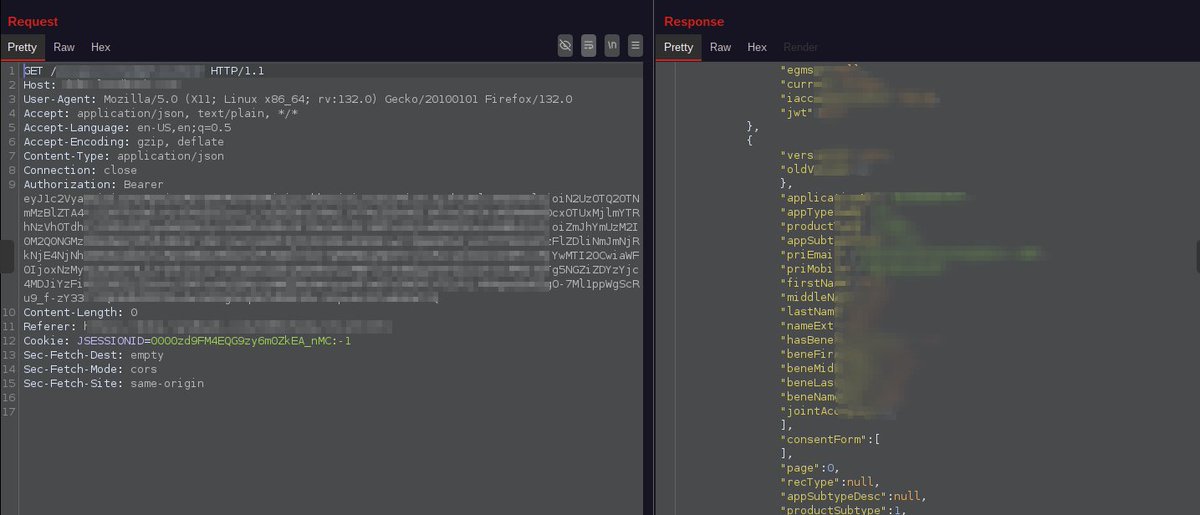
New Write-up!
Achieving Remote code execution by exploiting variable check feature!
shawarkhan.com/2021/01/achiev…

English
Shawar Khan
1.1K posts

@ShawarkOFFICIAL
Security Engineer at https://t.co/Ij35PKq2yZ | OSCP+ | CCEP | CAIPJ | CSCRB | CVE-2019-8389 | Synack Acropolis | Acknowledged by Top Tech Giants.