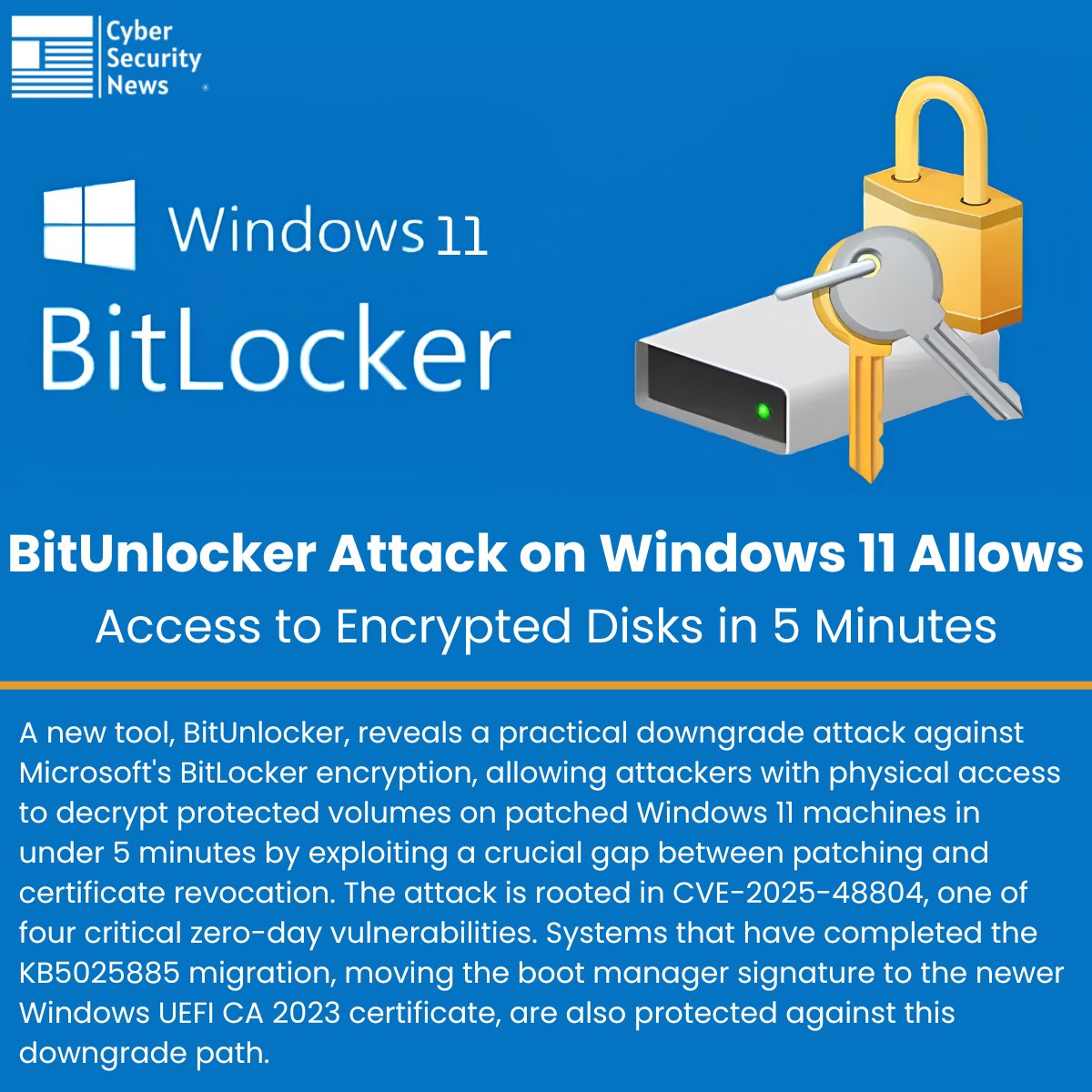
@The_Cyber_News Impressive work. This looks less like a “BitLocker break” and more like a deep understanding of Windows trust transitions, WinRE, recovery states, and compatibility layers.
Very valuable research. Respect to the researchers involved.
English