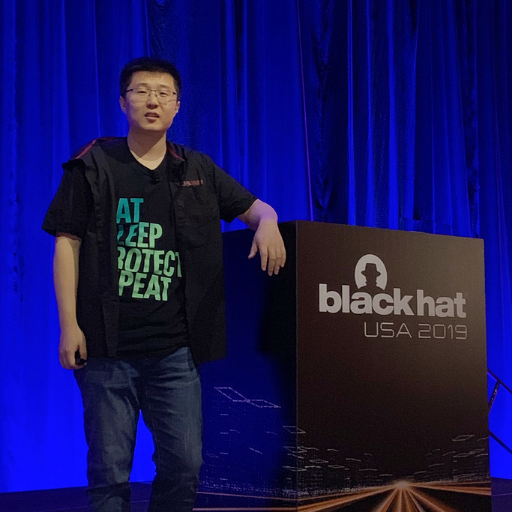
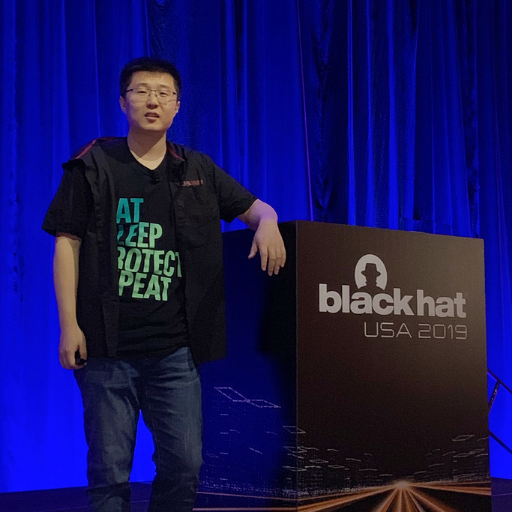
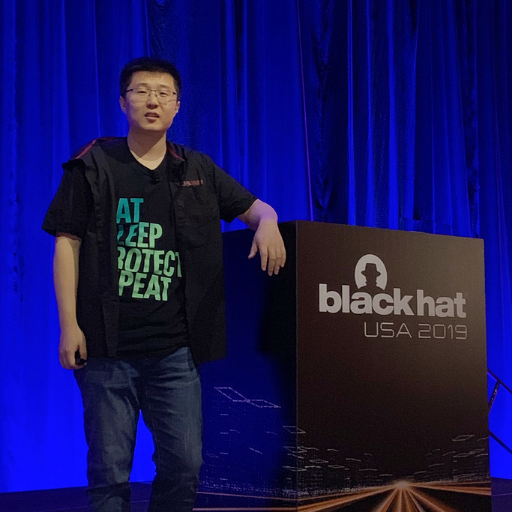
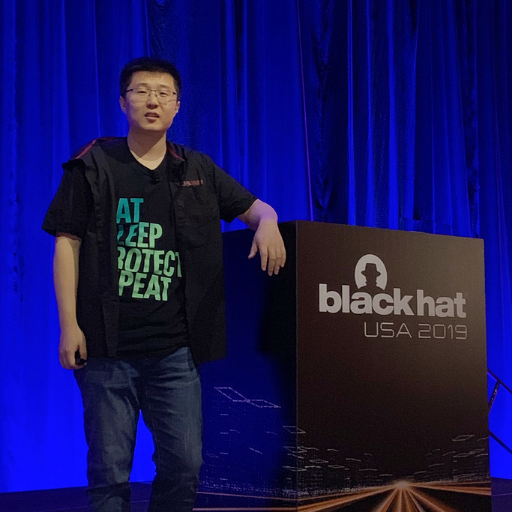
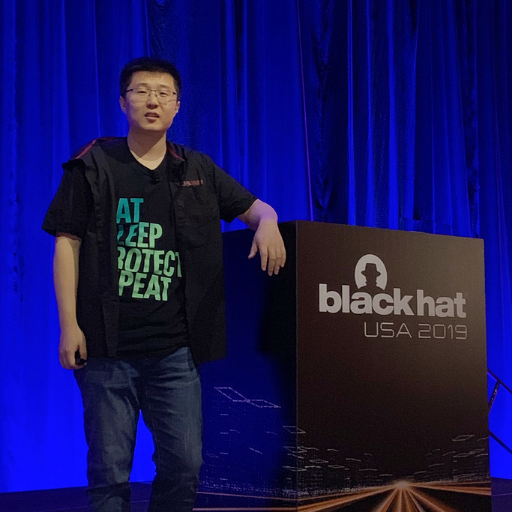
Min(Spark) Zheng
277 posts
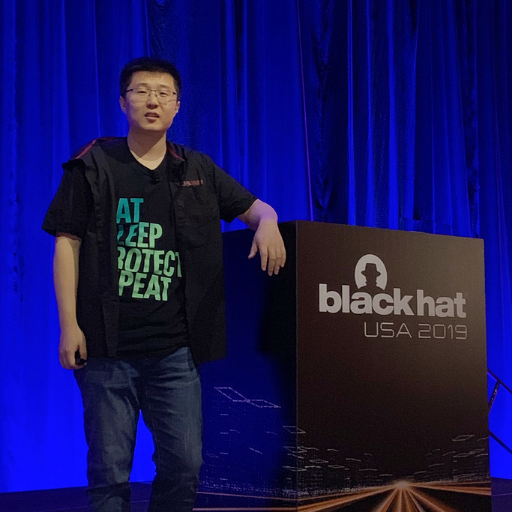
Min(Spark) Zheng
@SparkZheng
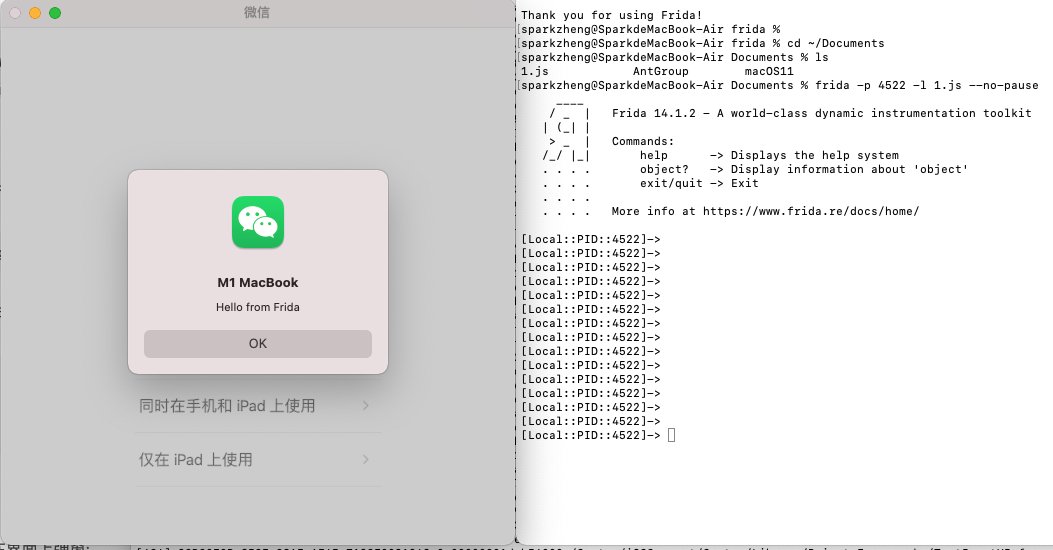
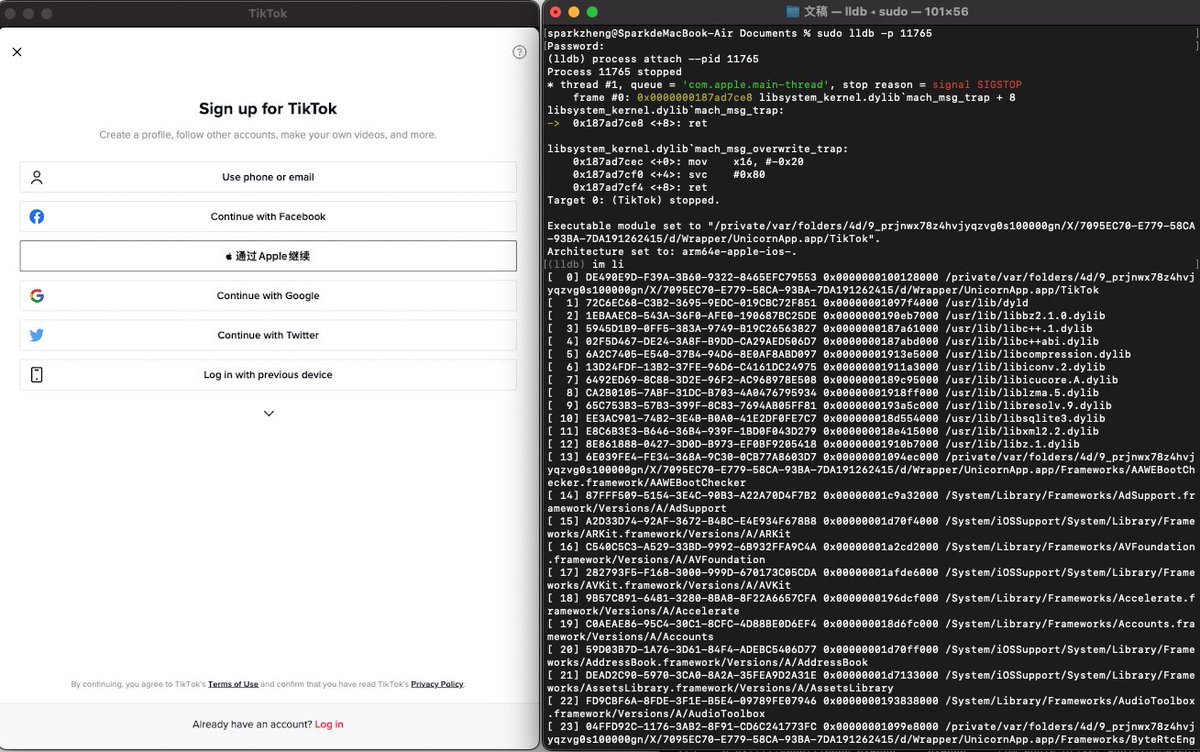
Android/iOS Senior Security Engineer @ Alibaba, CUHK PhD, a member of Blue-lotus and Insight-labs, worked in FireEye , Baidu and Tencent.




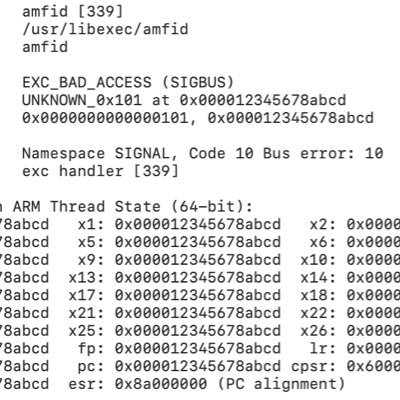
Our good friend @_bazad has a few things left over in the Project Zero publishing pipeline -- "it's really easy to miss bugs, even ones that you feel should have been obvious".
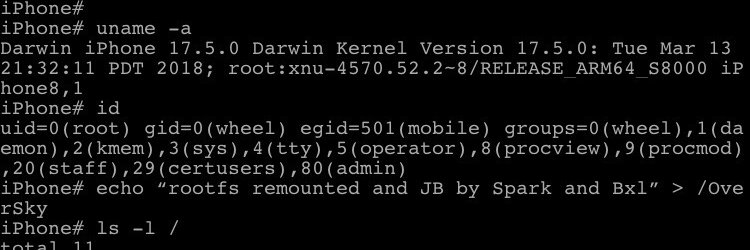
Who needs a write-up when you can see the source code? tardy0n for iOS 13.0 - 13.5, co-developed by @tihmstar and me: github.com/TheOdysseyJB/O…

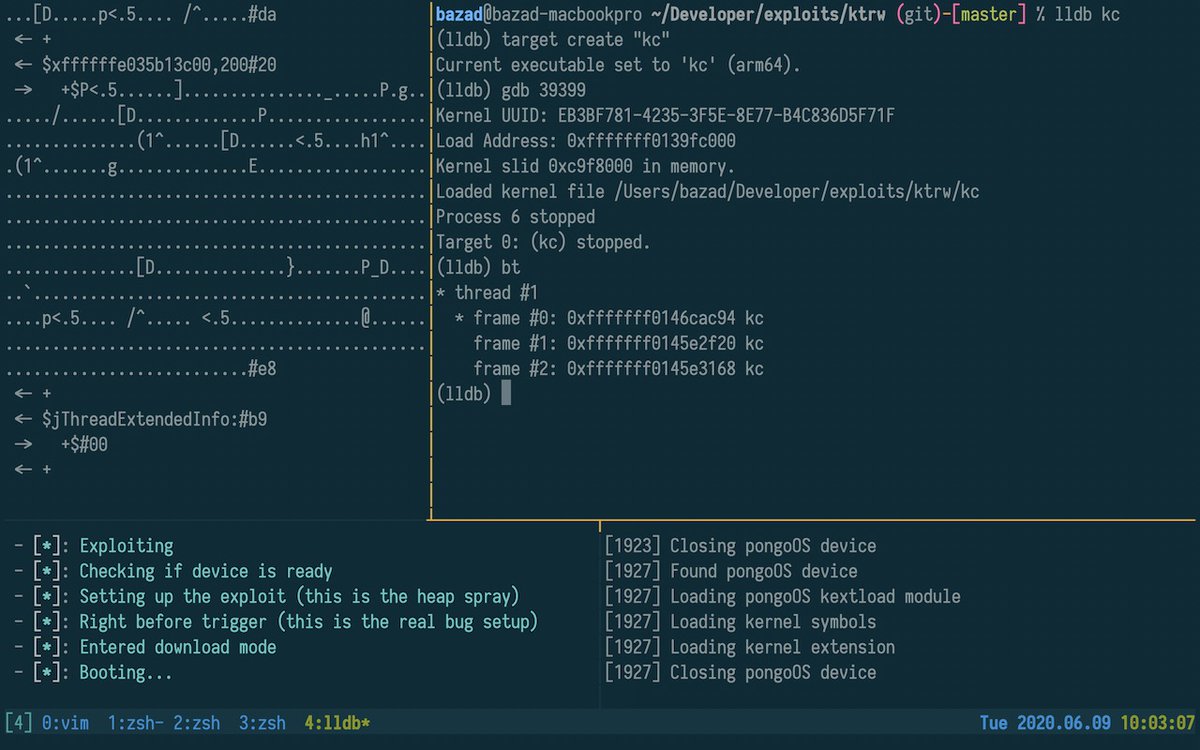
I've compiled a summary of every original public iOS kernel exploit from app context since iOS 10, describing the high-level exploit flow to get stable kernel read/write. The trends of how these exploits have evolved over time are quite interesting: googleprojectzero.blogspot.com/2020/06/a-surv…
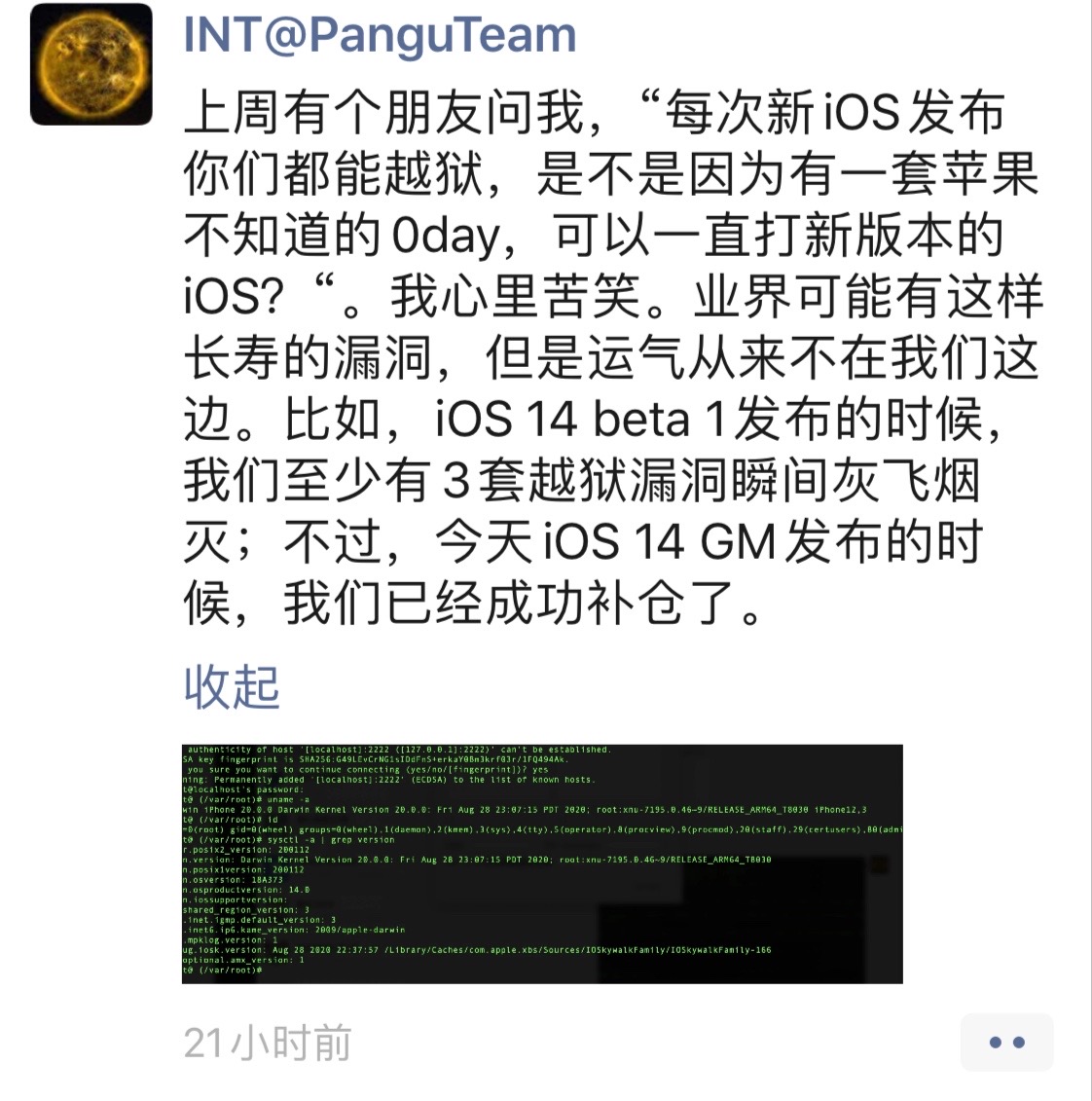
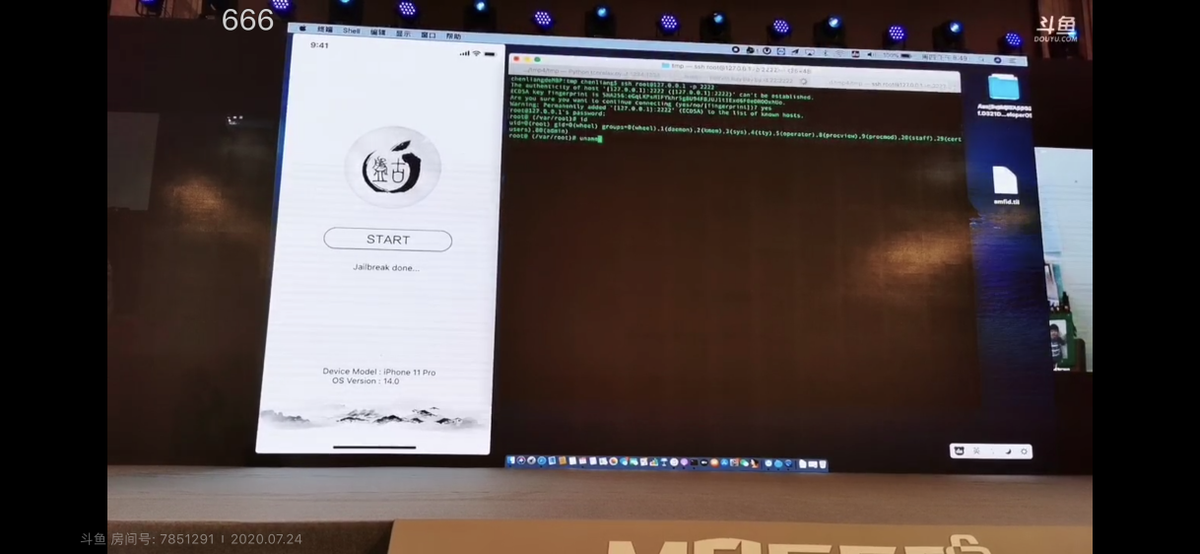
Cool and good job! I am more interested in what 0day vulnerabilities are used, but the entire payload has been obfuscated and it will take some time to analyze. 😅
#unc0ver v5.0.1 is now out - unc0ver.dev.