The threat didn't break in. It simply applied. 💼
Background check: passed.
Interviews: nailed.
Intent: not so great...
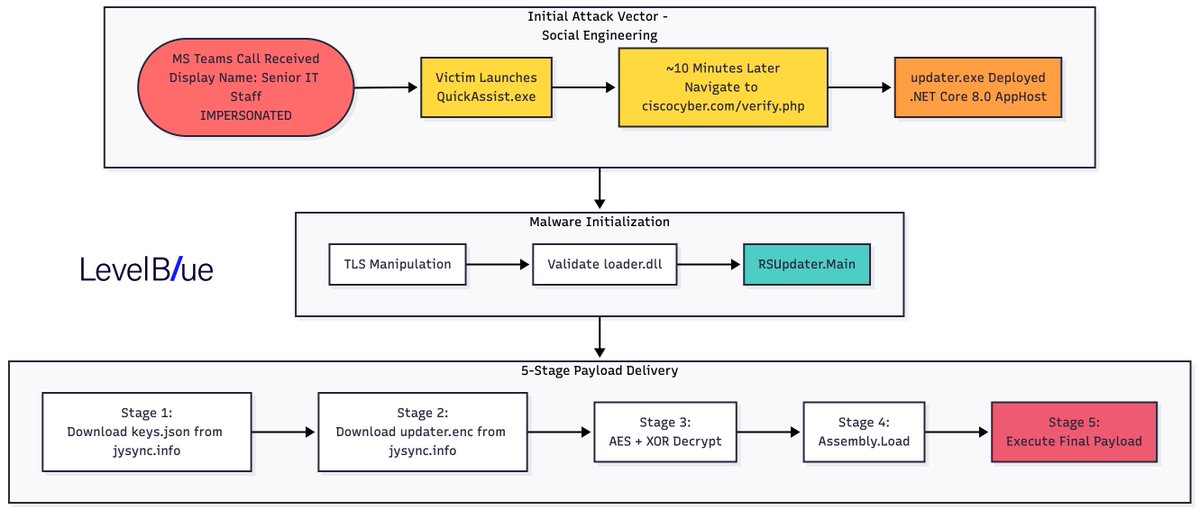
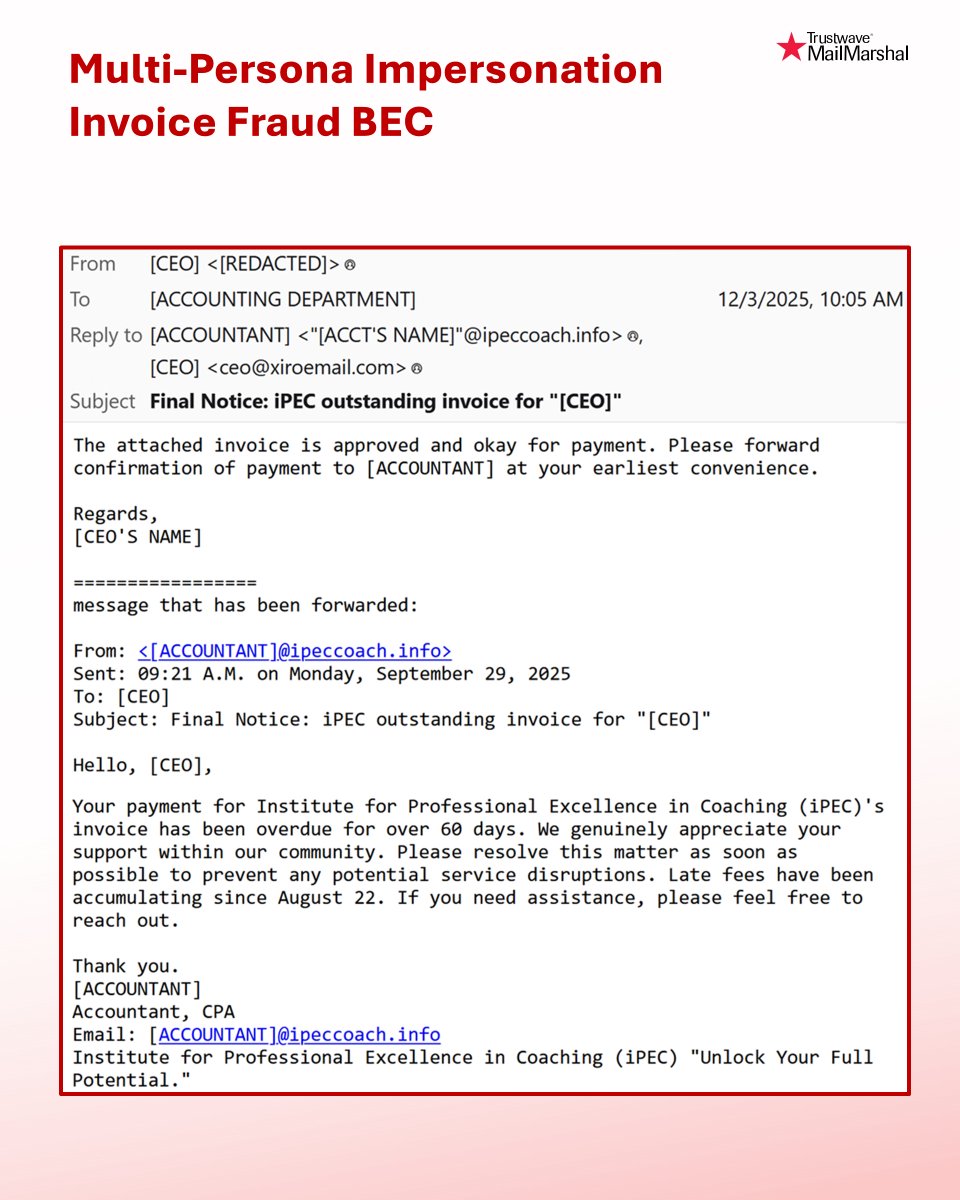
This case shows how a North Korea-linked IT worker blended into a legitimate hiring funnel and how combining OTX intelligence with XDR surfaced what individual tools would miss.
hubs.ly/Q0476_Xz0
English