Subash S
10.2K posts

Subash S
@SubashSRover
Virgil says ' Timeo Danaos et dona ferentes ', I say I'm a Phlegmatic Perquisite Perjurer following ' La Forza del Destino ' of Verdi !
India Katılım Temmuz 2015
5.7K Takip Edilen492 Takipçiler
Subash S retweetledi
Subash S retweetledi
Subash S retweetledi
Subash S retweetledi
Subash S retweetledi
Subash S retweetledi
Subash S retweetledi
Subash S retweetledi
Subash S retweetledi
Subash S retweetledi

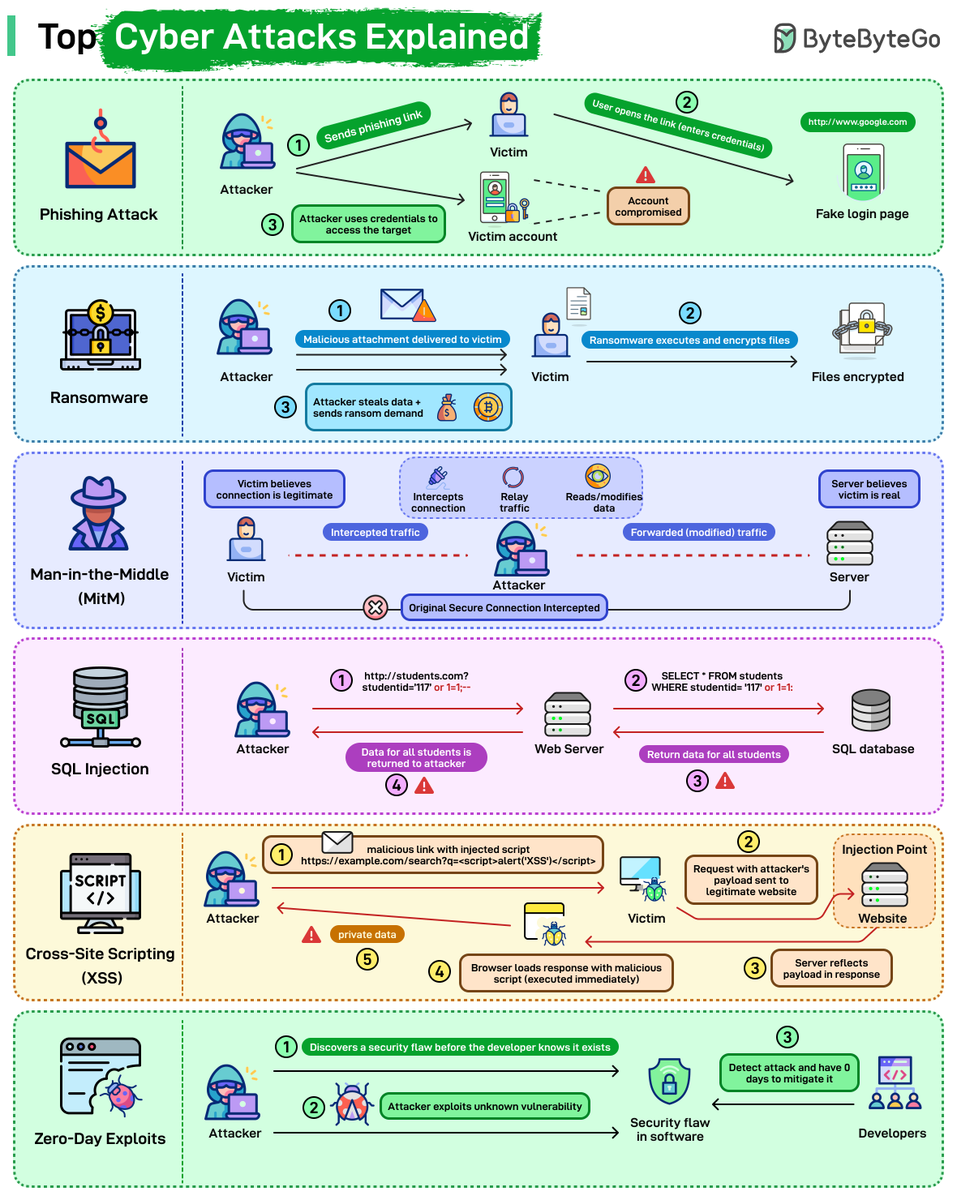
Top Cyber Attacks Explained
Here’s a quick look at how some of the most common attacks work:
Phishing: The attacker sends a fake link pointing to a spoofed login page. The victim enters credentials, the attacker captures them, and uses them to access the real system.
Ransomware: The victim opens a malicious attachment or file. The ransomware encrypts local data and demands payment to restore access. Files stay locked until the ransom is paid or a backup is restored.
Man-in-the-Middle (MitM): The attacker positions themselves between the victim and the server, intercepting traffic in both directions. Neither side detects the interception. The attacker can read or modify data as it passes through.
SQL Injection: Malicious SQL gets inserted into an input field, for example, studentId=117 OR 1=1. The database executes it as a valid query and returns data it shouldn't. A single vulnerable input field can expose an entire table.
Cross-Site Scripting (XSS): A malicious script gets injected into a legitimate page. When another user loads that page, their browser executes the script. Session tokens, cookies, and private data can be stolen this way.
Zero-Day Exploits: The attacker finds a vulnerability the vendor hasn't discovered yet. No patch exists. The attack runs until the vendor identifies the issue and ships a fix, which can take days or weeks.
Over to you: Which of these attacks have you seen most often in real environments, and which one do you think is the hardest to defend against today?
English
Subash S retweetledi
Subash S retweetledi
Subash S retweetledi
Subash S retweetledi
Subash S retweetledi
Subash S retweetledi

gstack is available now at github.com/garrytan/gstack
Open source, MIT license, let me know if it works for you. It's just one paste to install it on your local Claude Code, and it's a 2nd one to install it in your repo for your teammates.
English
Subash S retweetledi
Subash S retweetledi

First 500 people who take action can get totally free
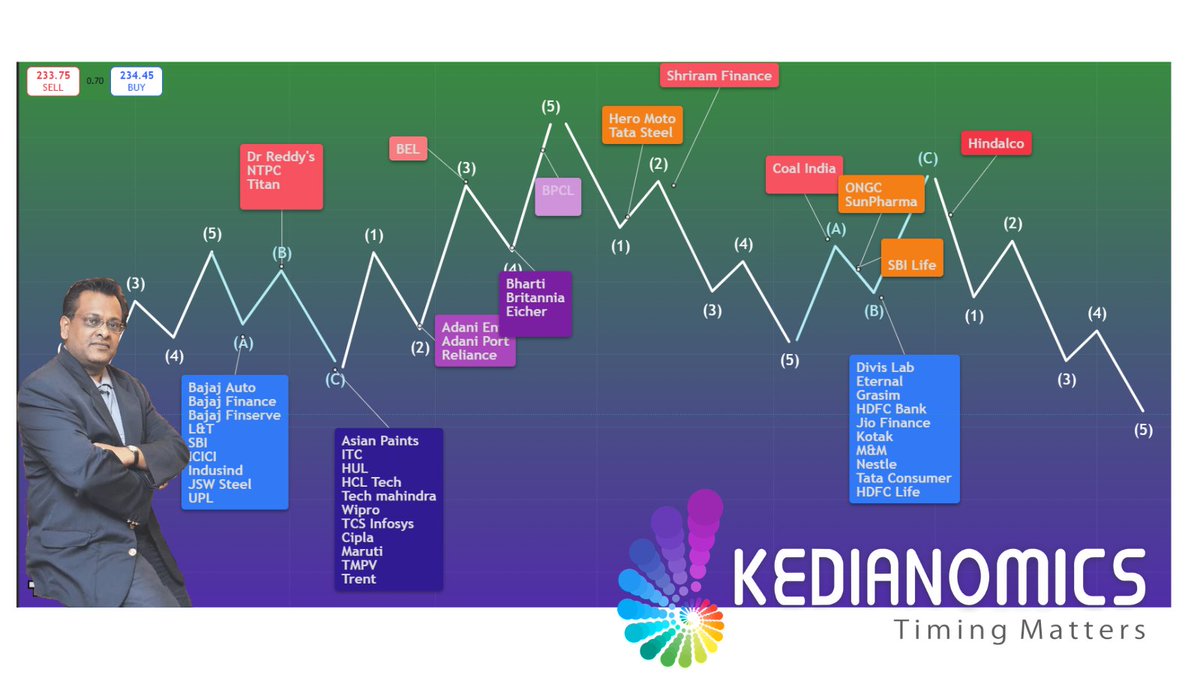
2.30 hr webinar costing 2500 with @sushilkedia where is explains every of 50 stocks of #Nifty going to 27000, where each stock is on the cycle. To get this:
-Follow us [So we can DM regn link]
-Retweet
-Nice Replies help
English
Subash S retweetledi
Introducing Nuxt Skill Hub 🧪
A Nuxt module that generates one project-aware skill entry point from your actual Nuxt stack, instead of me hand-maintaining a pile of separate skills
nuxt-skill.onmax.me 👇

English