TeamViris retweetledi
TeamViris
121 posts

TeamViris
@TeamViris
Official Viris twitter account.
Slovenia Katılım Mart 2019
81 Takip Edilen191 Takipçiler
TeamViris retweetledi

Hacker House build by @TeamViris at @BSidesLjubljana! #BSides #BSidesLjubljana hacking in progress👨🏼💻

English
TeamViris retweetledi

HackerHouse CTF competition by @TeamViris is ramping up @BSidesZagreb #BSidesZagreb #CTF #CaptureTheFlag #VulnCasa
English
TeamViris retweetledi
Our Hacker House about.vuln.casa managed to get to cold north at @Disobey_fi !
Please visit us in CTF area and win Flipper Zero! #Disobey26
English
TeamViris retweetledi

.@TeamViris will do #CTF at #BSidesLjubljana on the 13th of March next year. Meantime - #CFP is still open cfp.bsidesljubljana.si
#39c3 #CCC #CyberSecurity #InfoSec
ʎ3ʞʍoן@lowk3y
English
TeamViris retweetledi

Hardening the Hypervisor: Practical Defenses Against Ransomware Targeting ESXi
huntress.com/blog/hyperviso…
English
TeamViris retweetledi

Hey #infosec community - #BSidesLjubljana is back on track, planning for the 13th of March 2026! Save the date, share the news, participate!
CFP is open - cfp.bsidesljubljana.si
#CallForPresentations #CFP #CyberSecurity #SecurityBSides @SecurityBSides

English
TeamViris retweetledi

🧐 How smart can a smart home really be?
🤩 Step into the Vulnerable House CTF at #DefCamp 2025, a one-of-a-kind CTF experience, by @TeamViris!
Explore. Break. Learn. Everything, in the Hacking Village, at DefCamp 2025, on Nov. 13-14. Register here 👉 def.camp/competitions/v…

English
@BalCC0n is happening!
And we are proud to host CTF again this year! With our HackerHouse and new challenges! See more here about.vuln.casa !

English
TeamViris retweetledi

The Hacker House CTF for BSidesZadar is open!
Explore a smart home full of flaws, devices, and hidden flags.
No matter your skill level -- you’re welcome.
Brought to you in collaboration with @TeamViris
🔗 zadar.vuln.casa
#CTF #BSides #infosec #cybersecurity


English
TeamViris retweetledi

🚨URSIV z današnjim dnem razglaša povečano stopnjo ogroženosti varnosti omrežij in informacijskih sistemov zavezancev iz Zakona o informacijski varnosti. ❗️🛡️
Zaznana je bila škodljiva koda na novih USB ključkih 8GB proizvajalca Extra Lux. 🔐
V primeru, da posamezni organi, zavezanci, druge entitete in posamezniki posedujejo tovrstne USB ključke, naj jih ne uporabljajo. ❌
Več informacij 👉gov.si/novice/2025-06…
#URSIV #KibernetskaVarnost #Opozorilo #USBkljucki


Slovenščina
TeamViris retweetledi

📢 Nov zakon o informacijski varnosti je objavljen v Uradnem listu RS!
V Uradnem listu RS št. 40/25 je bil danes, 4. junija 2025, objavljen Zakon o informacijski varnosti (ZInfV-1), ki bo začel veljati 19. junija 2025. 🎓
⚖️ZInfV-1 predstavlja pomemben mejnik na področju kibernetske varnosti v Sloveniji. Zakon v naš pravni red prenaša evropsko direktivo NIS 2 in vzpostavlja celovitejši, sodoben okvir za zaščito omrežij in informacijskih sistemov.
🔍 Preverite ključne novosti in odgovore na pogosta vprašanja 👉gov.si/novice/2025-06…
Zakon bo pripomogel k večji odpornosti na kibernetske grožnje in varnejši kibernetski prihodnosti vseh nas. 💻🔐
#URSIV #KibernetskaVarnost #ZInfV1 #InformacijskaVarnost #NIS2 #Zavezanci
Slovenščina
Our team is ready, thrilled, and geared up to tackle challenges, break some binaries, and push our skills to the limit. It's always an honor to be part of such an incredible event, surrounded by top-tier hackers and like-minded enthusiasts. #CTF #INSO25 /cc @1ns0mn1h4ck



English
TeamViris retweetledi

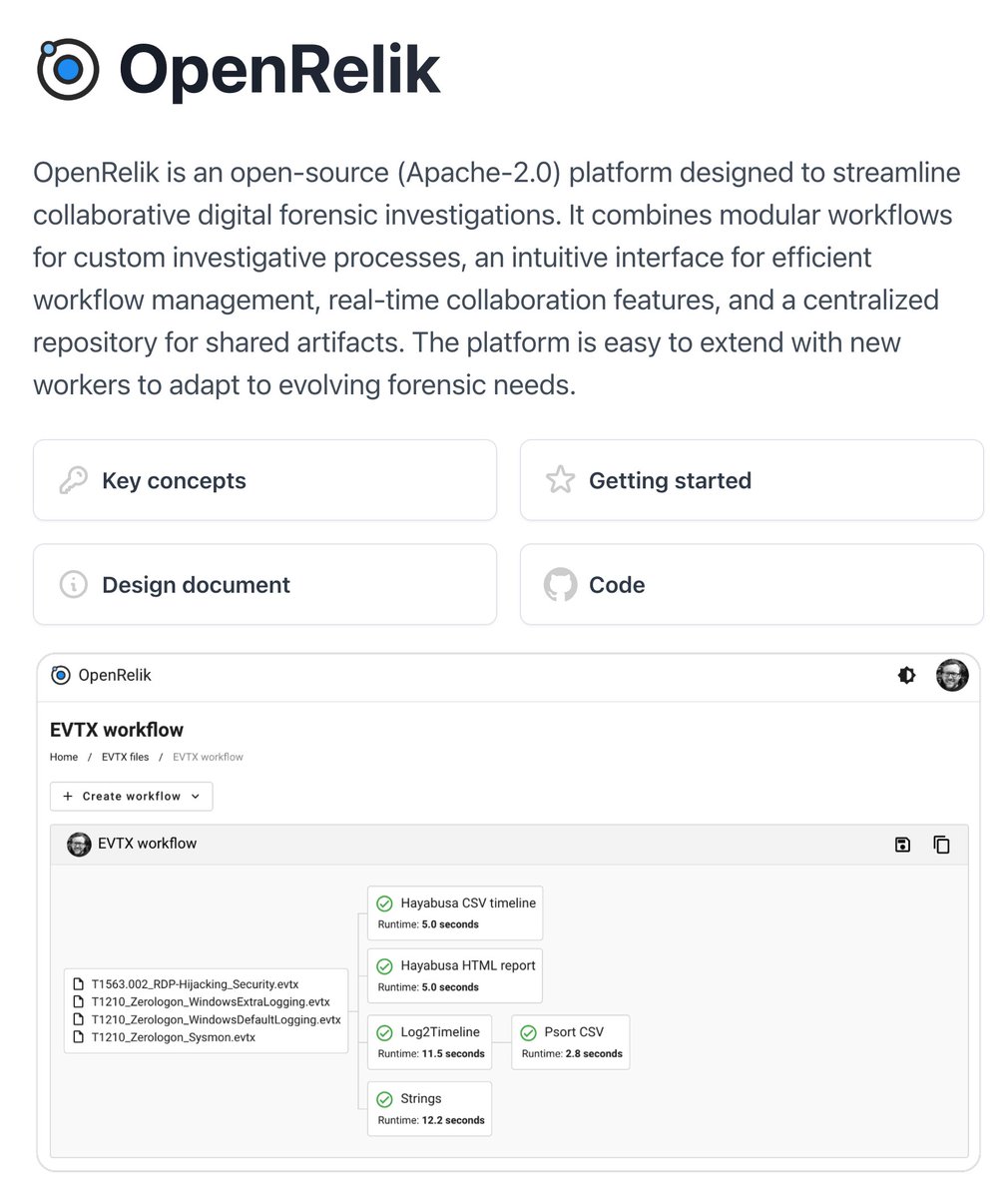
We published a worker to use our free scanner THOR Lite in OpenRelik
OpenRelik is an open-source platform designed to streamline collaborative digital forensic investigations | by @jberggren
Project page
openrelik.org
THOR Lite
nextron-systems.com/thor-lite/
THOR Lite worker
github.com/NextronSystems…
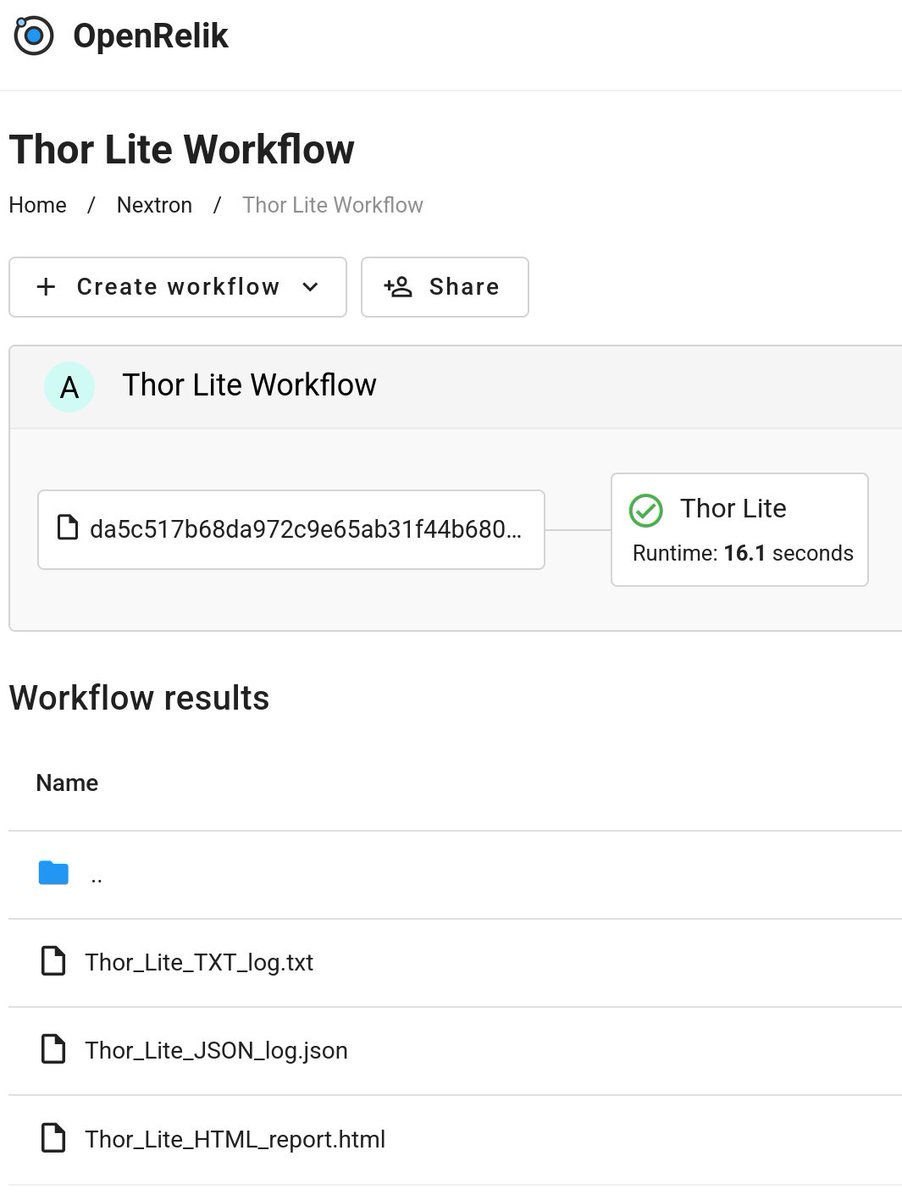
English
TeamViris retweetledi

CyberSec Trends Q1/25🔮
⬆️Lumma Stealer
↗️EDR killers (vulnerable drivers)
↗️Abuse of legit remote access tools
↗️0days in Fortinet & Ivanti
↗️Token persistence/cloud API abuse
⬆️Sliver implants
⬆️Fake CAPTCHA pages
⬆️Malvertising
Florian Roth ⚡️@cyb3rops
CyberSec Trends Q4/24🔮 ⬆️EDR killers (vulnerable drivers) ⬆️Auxiliary execution files .lnk .msc .rdp ⬆️Abuse of legit remote access tools ⬆️Token/cloud API abuse ⬆️ADCS exploitation ⬆️Fake CAPTCHAs: copy&paste PowerShell ⬆️TA using systems out of EDR scope for persistence
English
TeamViris retweetledi

CrowdStrike part 2 crashes Microsoft Office on Windows 11 24H2 | TechSpot techspot.com/news/105447-cr…
English
TeamViris retweetledi

Adversary in the Middle (AitM): Post-Exploitation w/ Michael Allen youtube.com/live/WY4mH-8Tb… via @YouTube by @Wh1t3Rh1n0
YouTube
English



