Sabitlenmiş Tweet

Get your free copy of my CF Alive book
Read on to see how to get your free copy of my CF Alive book. But first, what is the book about?
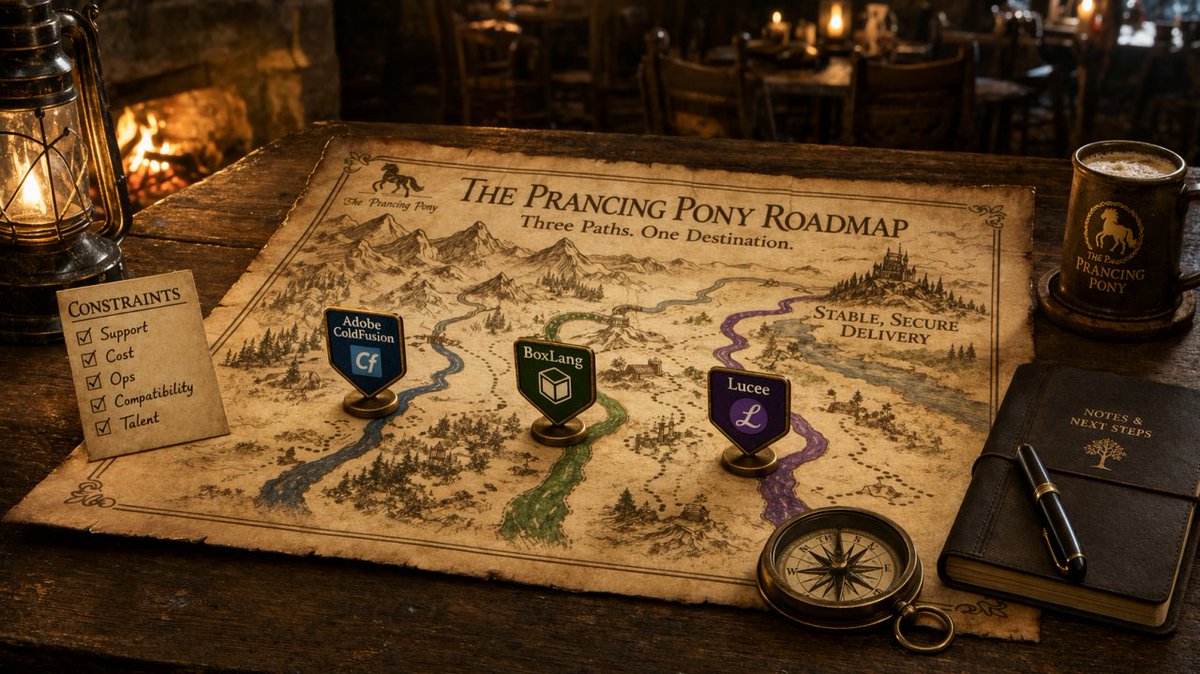
ColdFusion is a vibrant and modern language for complex, data-driven enterprise apps. While some companies have abandoned CF as dying, more farsighted dev teams have embraced CF. Learn how they are making it the most modern, secure and state-of-the-art web development ecosystem. Bar none.
The CF Alive book explains how you can:
* Modernize your legacy CF apps with 14 best practices for easy-to-maintain apps
* Discover 27 state-of-the-art tools from my hand-picked list that will make you more efficient at CF development
* Inspire others developers and young programmers with our proven 21 outreach methods
* Learn 8 keys to improve CF Marketing and be proud of using ColdFusion
* Contribute to making CF more alive this year
You can buy the book on Amazon or you can get a free copy by commenting on this post saying “I want CF Alive” and optionally saying why you want it.
What readers are saying about CF Alive:
"In CF Alive, the author explores best practices surrounding modern web development, recommending specific software tools and other resources for implementing these best practices for Adobe ColdFusion and other CFML application developers. What I liked best about the book (Kindle version), is that I could read about a recommended software tool, then link directly to a CF Alive Podcast between the author and a highly-experienced ColdFusion developer with expertise in using that tool." - G Cantor
"This book is taking on a tough challenge: convince the web development world that ColdFusion is worth investing in. There's a lot working against ColdFusion: its age, its decline in popularity, its perception as stagnant. What this book does, however, is line up all the many responses to those criticisms. It reaches out to new and former ColdFusion developers with the words of the very community that writes ColdFusion code today. It also speaks to existing ColdFusion developers and encourages them to embrace the latest techniques and technology that the ColdFusion community offers to help bolster and improve the name of ColdFusion in the development community.
If you are a current or former ColdFusion developer or simply curious about developing for ColdFusion, you should check this book out." - Miles Rausch
"I love the inspirational quotes throughout the book, and all the contributions from other CF community members. This reminds me of the Fusion Authority articles and the great sense of community support that they provided. The “Outreach” chapter is excellent in this regard — reading it brought back a lot of the feelings I got when I first met people in the CF community and shows how passionate the CFML community still is.
This is an excellent reference for people new to CMFL looking to get a jump start on recommended practices, and a great resource for anyone doing web development that just needs to be inspired again. (Full disclosure: I was interviewed for this book and also helped with the technical editing." - Nolan Erck
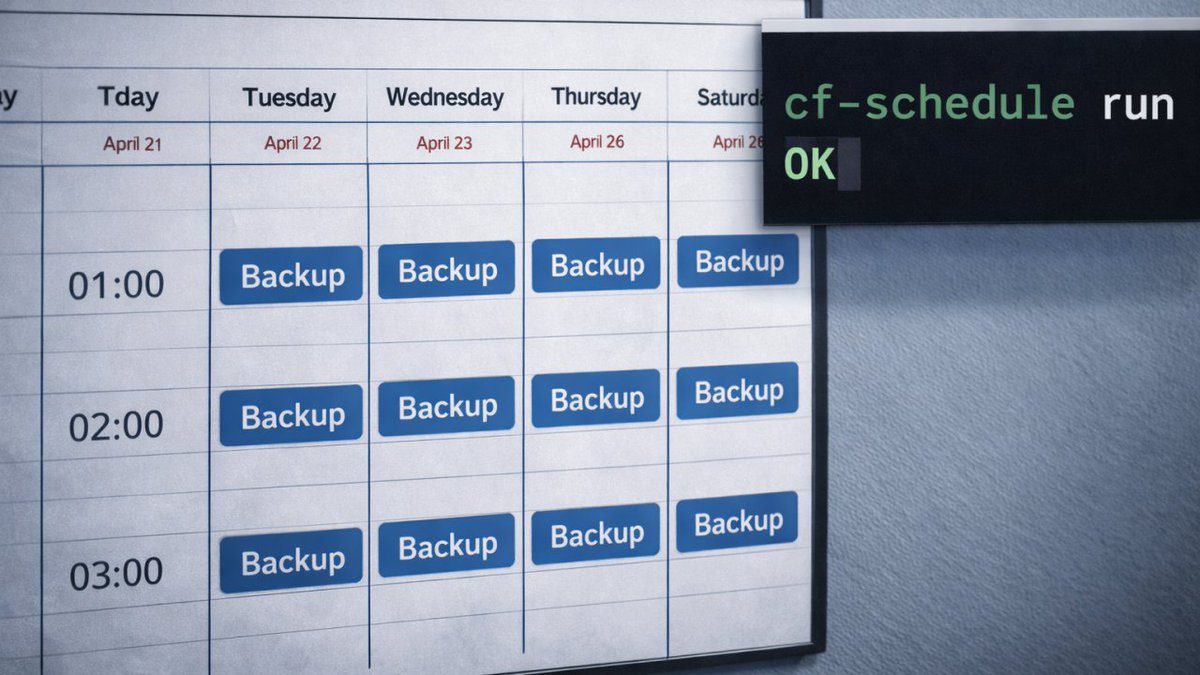
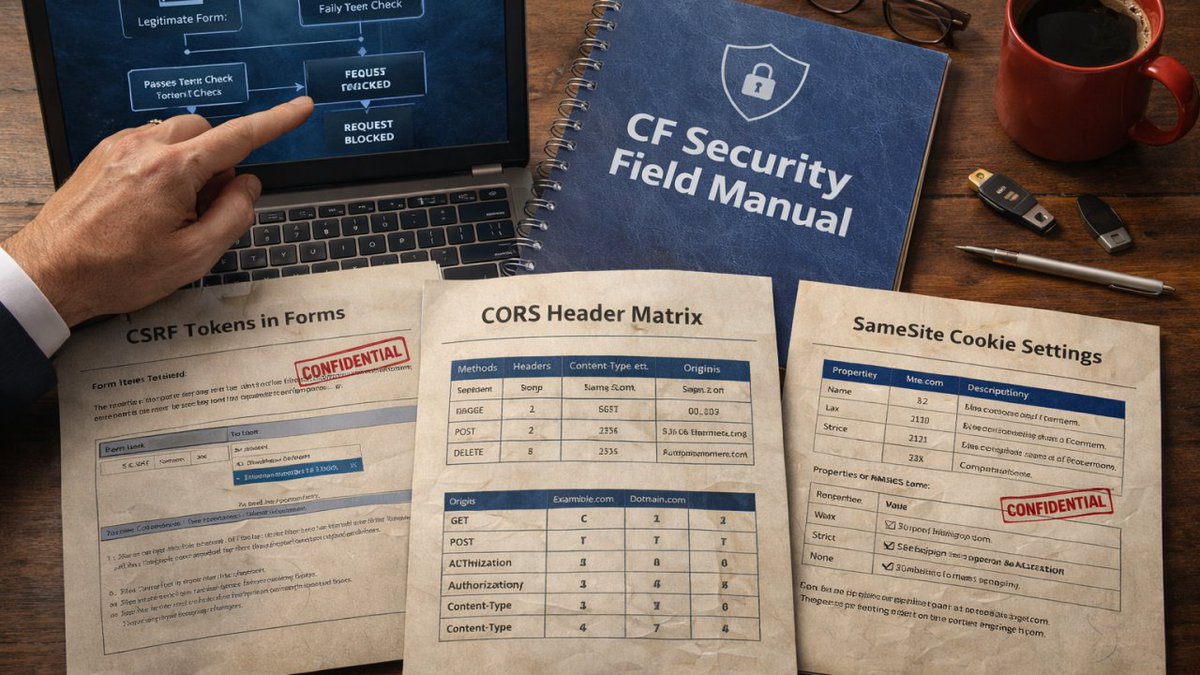
"We have all seen legacy developers stuck in their ways. It is time for ColdFusion developers to step up and modernize! CF Alive is a great resource written to provide the necessary tools and resources to update, secure, scale and deploy new and better applications with ColdFusion. This book helps from the newbie CF developer to the larger team of developers looking at ways to support and move forward with ColdFusion. Additional topics include containers, ways to bring more applications to the cloud, better security of our application source, testing environments, opportunities to use the open source Lucee engine and more.
It is time to bring more educational opportunities to developers with the rapid application development of ColdFusion. This book hits it straight on. CF is Alive!" - William Frankhouser
About the author
Michaela Light is the host of the CF Alive Podcast and has interviewed more than 60 ColdFusion experts. In each interview, she asks “What Would It Take to make CF more alive this year?” The answers inspired this book.
Michaela has been programming in ColdFusion for more than 25 years. She founded TeraTech in 1989. The company specializes in ColdFusion application development, security and optimization. She founded the CFUnited Conference and runs the annual State of the CF Union survey.
Get your copy of CF Alive now
You can buy the book on Amazon at
amazon.com/CF-Alive-Makin…
Or you can get a free copy by commenting below. Just say “I want CF Alive” and optionally why you want it. And I will PM you back with the book PDF and Mobi file. Easy!

English