The Phenom
897 posts

The Phenom
@TheMidasMethod
Business scaler. X saviour. Duppy maker.




Come on bro @BrendanSchaub












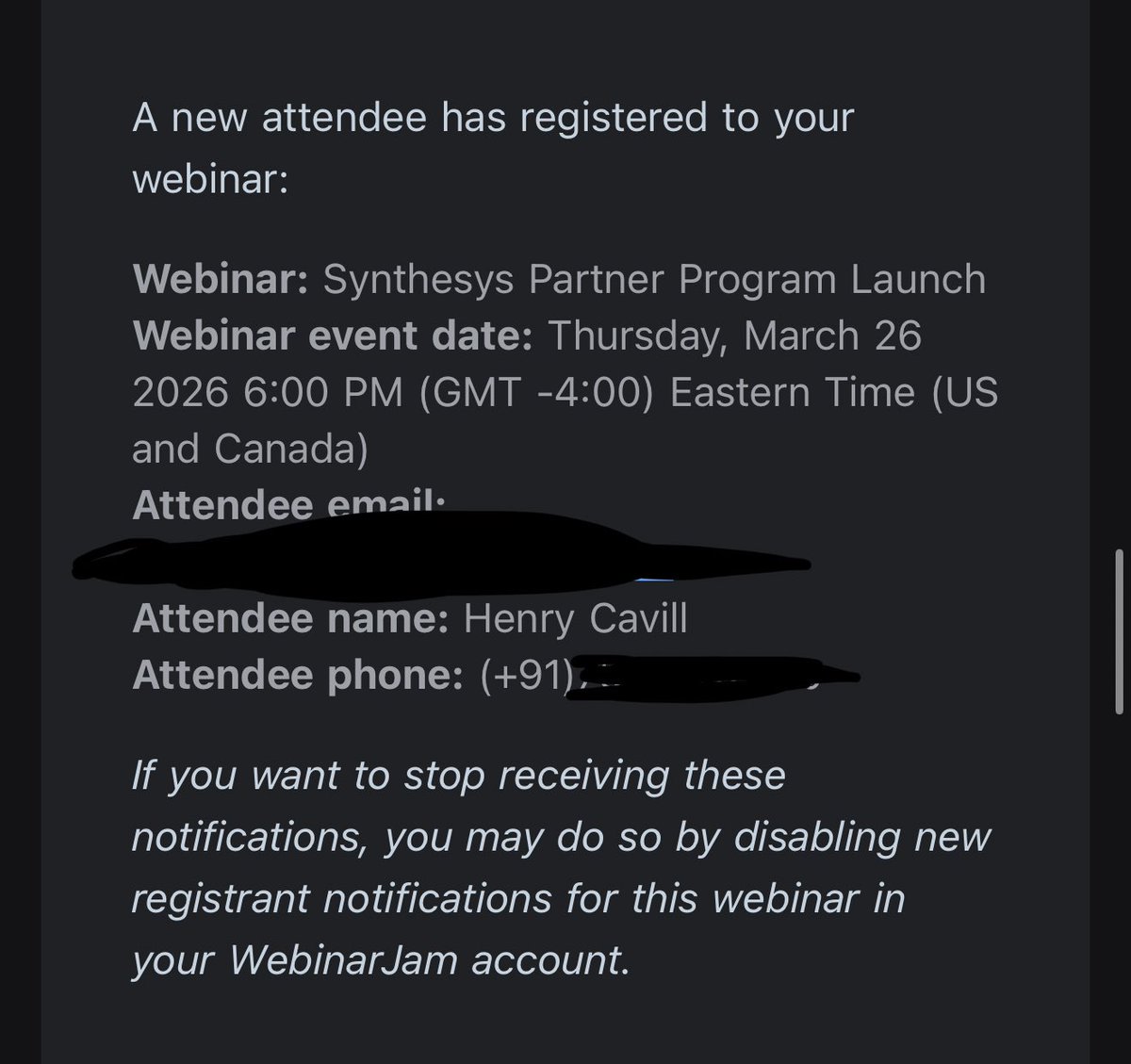
If you have a camera in your home or outside, in your office or shop, any connected electronic device, a car, or even a camera with Bluetooth, it can potentially be accessed or activated remotely, particularly if there is cooperation from a manufacturer or service provider, a software vulnerability, or interception through the network infrastructure. Modern devices are designed to communicate constantly with networks and other devices. Intelligence services or sophisticated attackers with sufficient technical capabilities can exploit these connections to conduct surveillance. In a world saturated with networked electronics, the line between personal equipment and potential monitoring tools has become increasingly thin.






For a cheap preworkout this one is pretty hard to beat. Nutricost getting a lot of my money these days.