Tikkala Security
367 posts

Tikkala Security
@TikkalaResearch
Securing Web2 & Web3, auditing and penetration testing.
Menlo Park, CA Katılım Kasım 2024
3 Takip Edilen665 Takipçiler

@taraxa_project Meanwhile, it lost 4.3 ETH and ~6,000 USDT tokens (worth ~$14,600 total). The root cause is the unprotected function 0x6cd50a67 in the contract etherscan.io/address/0x359c…, which allowed arbitrary transfers and mints.

English

It seems @taraxa_project was hacked. The attacker minted 100 * 1e30 $TARA tokens (etherscan.io/address/0x2f42…) in transaction etherscan.io/tx/0xa1301596c…. Attacker address: etherscan.io/address/0x7bd7….
English

The other contracts created by the same deployer were attacked, too. TX etherscan.io/tx/0x1b28fdbf0…
victim: etherscan.io/address/0xae4c…
English

An old contract named RIGHT (etherscan.io/address/0x0241…) was hacked and lost about 6.7 ETH (~$14K).
Tx: etherscan.io/tx/0x7b3878969…
Attacker: etherscan.io/address/0x66d3…
English

The unknown function selector 0x83c7b8e4 allows transferFrom of any user who previously approved the $ETF token (bscscan.com/address/0xec7b…) and swap with $USDT. In that transaction, 22 victims' $ETF tokens were attacked.
English

Another access control attack on the contract bscscan.com/address/0x1b69…. Address bscscan.com/address/0x56b9… gained about $75k. Attacker: bscscan.com/address/0x4bf7…. Tx: bscscan.com/tx/0x1d8ebeb5a…
English

There are two issues in the victim contract (bscscan.com/address/0x46e1…). The unknown function selector 0x6f73978a allows calling transferFrom on any account, forcing a swap of $OLY tokens (bscscan.com/address/0x5440…) and enabling the sandwich attack.
English

Attacker bscscan.com/address/0xf103… gained more than $60K in tx bscscan.com/tx/0x827e23d6d…. The victim contract bscscan.com/address/0x46e1… lacks access control and blindly trusts user input, allowing it to transfer any user's $USDT who has given allowance. Please revoke the allowance ASAP!
English

@doom_cats 2/ The attacker created 60 contracts and kept calling rescue() to force the victim contract to swap out more Heaven Gate ($HATE Token) while putting 5 WETH into the swap. This affects the K value, allowing the attacker to profit using a sandwich attack.

English

An old NFT contract, DoomCat (@doom_cats), was attacked and lost about 2 ETH (~$5k).
Attacker: etherscan.io/address/0xb84b…
Tx: etherscan.io/tx/0x58d57759c…
English

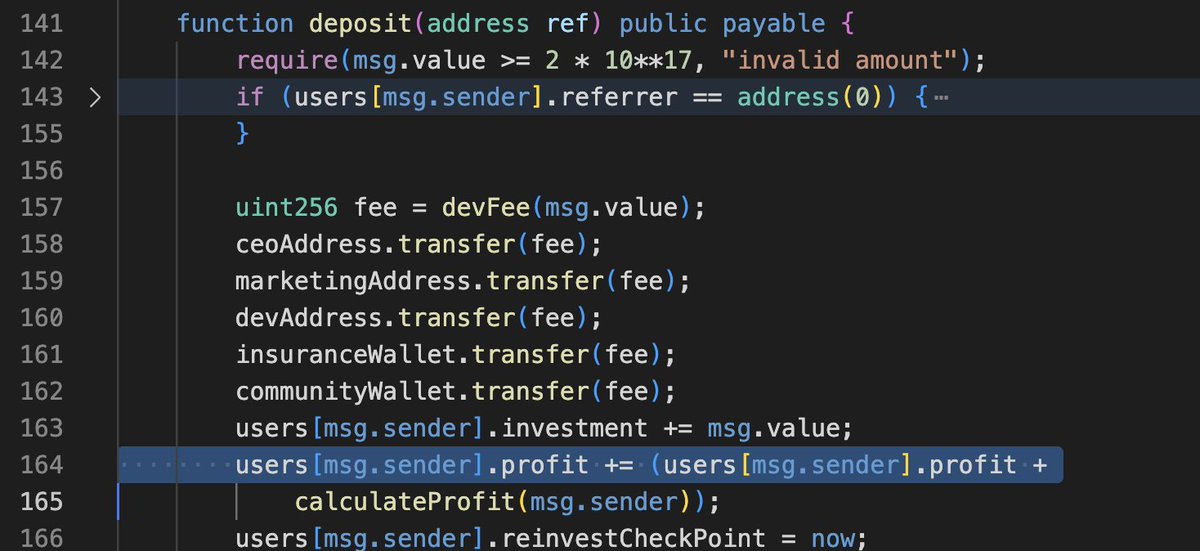
@RAILGUN_Project The double add caused the profit to increase no matter what.
English


An old WADJET contract on BSC was hacked, losing about 111 BNB (worth $98k) in tx bscscan.com/tx/0x6ee0086b5…. Attacker bscscan.com/address/0xdbdc… moved the assets to bscscan.com/address/0x8b6b…, which seems funded by Rail BSC: Deployer (bscscan.com/address/0x76eb…) @RAILGUN_Project.
English

An attacker (bscscan.com/address/0xa33a…) attacked the new $HTC token using nearly 500 contracts and 37M gas. TX: bscscan.com/tx/0x9e1ea64cb…. The token contract's awarding logic has an issue, leading to a $45K loss.

English

@EdenNetwork The locker account could be any one, the startTime is from user input, the lock receiver could be any one, too.

English

It seems like @EdenNetwork lost 12 ETH and 1.24M $EDEN tokens, worth about $54k in this tx: etherscan.io/tx/0xa5fde4dd2….
The attacker (etherscan.io/address/0xd5db…) called the vulnerable lockTokens() function, which allowed the contract to transferFrom any user account and assign an arbitrary startTime value.
English

Another copy attacker etherscan.io/address/0xcafe… walked away about $10k in this tx etherscan.io/tx/0xd462ce892…
English

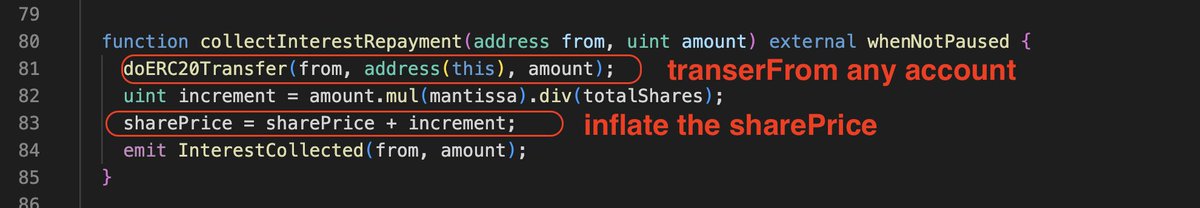
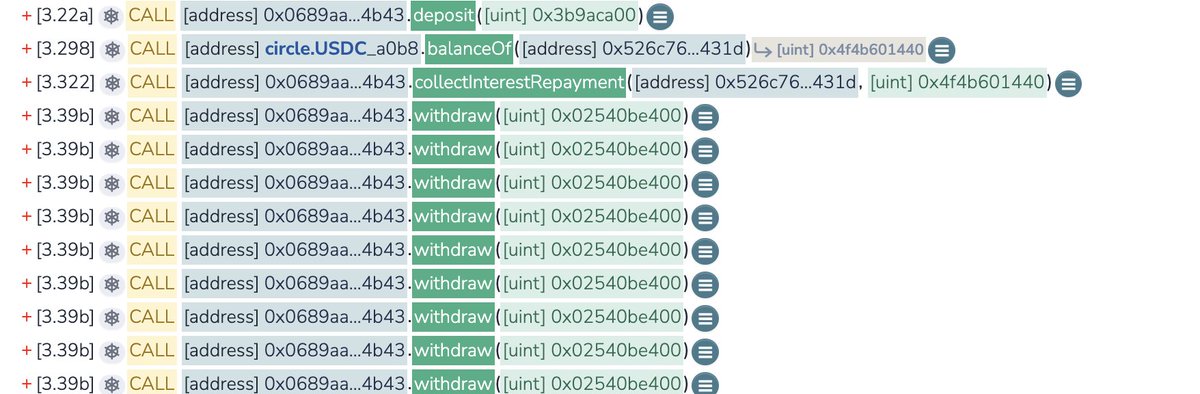
An unknown contract (etherscan.io/address/0x0689…) has an issue allowing users to pump the sharePrice and gain from its staking. It has another issue allowing transferFrom of $USDC from any account with allowance. Attacker (etherscan.io/address/0x2c2e…) gained about $330k from the victim (etherscan.io/address/0x526c…) in tx (etherscan.io/tx/0x3a8bde0a1…).
English