Sabitlenmiş Tweet
Jason
7.4K posts


Jason
@Trackpads
Dr. Jason Edwards, DM, CISSP, CRISC Follow Me | Cybersecurity | Author | Professor | Veteran | Father | Cheer Dad | Husband | Dog Dad
Texas Katılım Ağustos 2009
399 Takip Edilen956 Takipçiler

On a personal note, beagles have a special place in my heart.
I wrote a children’s book about a beagle because these dogs deserve to be seen the way they really are: loyal, funny, gentle, curious, stubborn, loving, and full of life.
That is why stories like this hit so hard. Every beagle deserves a home, a family, and a chance to be loved — not a life behind facility walls.
Find Darwins Stories here: amzn.to/4ukY2M7
English

Based on the reporting, roughly 1,500 of Ridglan Farms’ approximately 2,000 beagles are being moved to rescue groups, with the first 300 leaving Friday.
This is a victory worth celebrating, but it should never have taken this long.
Beagles — or any dogs — should not be treated as disposable research inventory. They are living, feeling animals that deserve sunlight, grass, safety, affection, and a real home.
The fact that hundreds are now leaving Ridglan Farms and heading toward rescue, medical care, and eventual adoption is a meaningful win. But it is also a reminder of how much cruelty can hide behind sterile language like “research,” “testing,” and “facility.”
Anyone who participates in breeding, supplying, or using dogs for painful experimentation should be publicly condemned and held accountable. Scientific progress should not depend on turning loyal animals into instruments of suffering.
I’m glad to see these beagles getting a chance at life. Now let’s make sure this is not treated as an exception, but as a turning point.
English

Read the article here: linkedin.com/newsletters/ba…
If you’re exploring the Systems Security Certified Practitioner (SSCP), you can find the free audio course developed by Bare Metal Cyber, the Study Guide book, and the Flash Cards ebook together on the Bare Metal Cyber Academy page: baremetalcyber.com/cybersecurity-…
English

The Systems Security Certified Practitioner (SSCP) helps early-career cybersecurity professionals move from basic awareness into the real work of securing systems, managing access, and supporting day-to-day defense operations. It is a practical certification for people who want to show they can handle security responsibilities inside live IT environments instead of only talking about theory.
🔐 SSCP is built for real-world security operations, not just abstract concepts
🖥️ It fits especially well for admins, analysts, and support pros stepping into security work
📡 The exam rewards applied judgment across access control, network security, monitoring, and incident response
🧠 It is a strong bridge between foundational certs and bigger operational security responsibilities
🎧 Busy professionals can prep in a more flexible way with audio, structured reading, and flash-card review
#Certified #SSCP #ISC2 #Cybersecurity #SecurityOperations #SecurityAnalyst #SystemsAdministrator #NetworkSecurity #CyberCareer #CareerChange #ITCareers #CyberEducation #BareMetalCyber

English

A company cook turns front-line assault leader along a muddy Italian ditch under fire. Today’s Beyond the Call revisits Technician Fifth Grade Eric Gunnar Gibson at Isola Bella in 1944. Link in the first comment!
🪖 A shallow drainage ditch becomes the only cover as German machine guns and artillery lock onto the advance.
⚔️ A Swedish-born company cook steps out front to lead green replacements through their first minutes under fire.
🎖️ Four enemy positions destroyed, five dead, and prisoners taken as one man claws forward through mud and explosions.
📜 Quiet courage, immigrant grit, and a final solo rush that secures the flank but costs Gibson his life.
#BeyondTheCall #DispatchMagazine #Trackpads #MedalOfHonor #WorldWarII #Anzio #USArmy #MilitaryHistory #Leadership #Veterans

English

Read Today’s Edition! linkedin.com/newsletters/da…
More links:
📰 DailyCyber.News: dailycyber.news
⚔️ Amazon Author Page: amazon.com/author/jasonce…
🔗 LinkedIn: jason-edwards.me
🛡️ Bare Metal Cyber: baremetalcyber.com
English

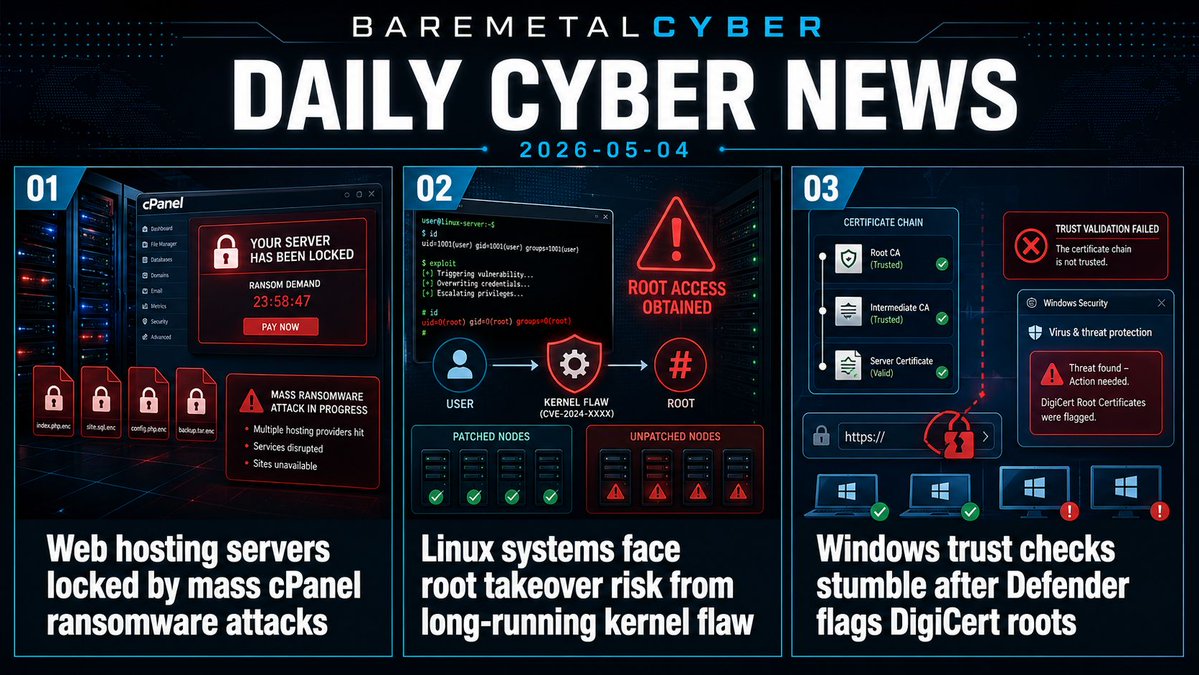
Today’s biggest risk is operational disruption across the systems companies rely on to host websites, run Linux workloads, and validate digital trust. The brief also looks at vendor code exposure, AI automation failures, cloud account abuse, and scams that turn familiar platforms into attack paths.
• 🚨 Web hosting servers locked by mass cPanel ransomware attacks
• 🐧 Linux systems face root takeover risk from long-running kernel flaw
• 🪪 Windows trust checks stumble after Defender flags DigiCert roots
• 🧬 Security vendor source code exposure raises supplier confidence questions
• 🤖 AI agents need hard limits before they can touch production data
• ☁️ SaaS attackers are finding faster paths through trusted login flows
• 📦 Cybercrime is increasingly spilling into logistics, cargo theft, and real-world losses
#Cybersecurity #CyberRisk #InfoSec #CloudSecurity #Ransomware #LinuxSecurity #MicrosoftSecurity #SaaSSecurity #SupplyChainSecurity #BareMetalCyber
English

Stay connected for more cybersecurity writing, analysis, and daily reporting:
⚔️ Amazon Author Page: amazon.com/author/jasonce…
🔗 LinkedIn: jason-edwards.me
🛡️ Trackpads: trackpads.com
📰 Dispatch Magazine: dailycyber.news
🎙️ Beyond the Call Podcast: beyond.trackpads.com
🎧 Dispatch Magazine Podcast: dispatch.trackpads.com
English

Stay connected for more cybersecurity writing, analysis, and daily reporting:
⚔️ Amazon Author Page: amazon.com/author/jasonce…
🔗 LinkedIn: jason-edwards.me
🛡️ Trackpads: trackpads.com
📰 Dispatch Magazine: dailycyber.news
🎙️ Beyond the Call Podcast: beyond.trackpads.com
🎧 Dispatch Magazine Podcast: dispatch.trackpads.com
English

Stay connected for more cybersecurity writing, analysis, and daily reporting:
⚔️ Amazon Author Page: amazon.com/author/jasonce…
🔗 LinkedIn: jason-edwards.me
🛡️ Trackpads: trackpads.com
📰 Dispatch Magazine: dailycyber.news
🎙️ Beyond the Call Podcast: beyond.trackpads.com
🎧 Dispatch Magazine Podcast: dispatch.trackpads.com
English

Find the full certification page, study resources, and helpful links below:
🎓 Bare Metal Cyber Academy: baremetalcyber.com/cybersecurity-…
📚 Amazon Study Guides & Flash Cards: amzn.to/3O0VO5l
🔗 LinkedIn: jason-edwards.me
🛡️ Bare Metal Cyber: baremetalcyber.com
📰 DailyCyber.News: dailycyber.news
English

CSSLP is for people who need to build, review, and manage software with security in mind from the beginning, not as a cleanup step at the end. It matters because secure software is not just about finding bugs in code. It is about requirements, design, architecture, testing, deployment, and the discipline to reduce risk across the full development lifecycle. For developers, AppSec practitioners, architects, engineers, and security-minded technical leaders, CSSLP speaks to work that is increasingly central to how modern systems get built.
Find more information and links in the first comment below!
The free audio course podcast is built for busy people who want to learn this material in a format that fits real life. It helps break down secure software concepts into clear, practical lessons on topics like secure design, threat thinking, code quality, testing, lifecycle security, and the kind of decisions that shape software long before release day. It is available wherever podcasts are found, so it works well during commutes, walks, and the spaces between everything else.
The study guide, available in paper and ebook on Amazon, is the structured companion for going deeper. It is there for readers who want stronger explanations, better organization, and a clearer path through the material. The flash cards ebook on Amazon adds 1,000 cards for review, repetition, and exam prep, making the full stack feel like one connected learning path from first exposure, to deeper understanding, to reinforcement.
Taken together, the audio course, study guide, and flash cards give busy learners a practical way to strengthen both their exam prep and their understanding of how secure software should actually be built. Take a look and keep building skills that matter across the full lifecycle.
#CSSLP #SecureSoftware #AppSec #SoftwareSecurity #SecureDevelopment #Cybersecurity #DevSecOps #SecureSDLC #CertificationPrep #SoftwareEngineering

English

Stay connected for more cybersecurity writing, analysis, and daily reporting:
⚔️ Amazon Author Page: amazon.com/author/jasonce…
🔗 LinkedIn: jason-edwards.me
🛡️ Bare Metal Cyber: baremetalcyber.com
📰 DailyCyber.News: dailycyber.news
English

Phone phreaking is often remembered as a clever scam, a weird prehistory of hacking built on toy whistles and long-distance calls. What it really exposed was a design flaw in one of the most trusted systems of the twentieth century. For years, parts of the telephone network carried control signals in band, meaning the tones that told the system how to route a call traveled over the same path as the human voice. The network treated the right sound as authority.
For more information, see the first comment below!
That mattered because a user who could reproduce those tones could sometimes talk to the network in its own language. On long-distance trunks in the Bell System, a 2600 Hz tone could help signal that a line was idle, and multi-frequency signaling tones were used to direct switching farther down the route. Phone phreaks learned that if they could seize a trunk and then inject the proper sequence, often with a blue box, they could influence routing without being the phone company. The exploit was elegant in one sense and damning in another: the system had weak ideas about who was allowed to send control instructions.
That is why this story still matters. The real lesson was not free calls. It was trust without strong separation. Control traffic and user traffic shared the same channel, and the network assumed that anything speaking in the proper machine language must be part of the system itself. John Draper became one of the famous names from that world, but the bigger story was institutional: an enormous, sophisticated network had confused valid signals with valid sources.
Modern security keeps rediscovering the same mistake in new forms, whether it is overly trusted admin tools, flat internal networks, or software that accepts commands from the wrong place because they look structurally correct. Phone phreaking belongs to telecom history, but its warning is current: when a system cannot reliably distinguish a customer from its own control plane, how long is it really secure?
#Cybersecurity #PhonePhreaking #Telecommunications #BlueBox #CyberHistory #NetworkSecurity #TrustAndSecurity #HackingHistory #SecurityArchitecture #TechnologyHistory

English