TreeCityWes.xen retweetledi
TreeCityWes.xen
24.7K posts

TreeCityWes.xen
@TreeCityWes
https://t.co/ow1DTL3YQz | https://t.co/NEurMmo6YC
treecitywes.eth Katılım Mart 2009
1.8K Takip Edilen3.1K Takipçiler
TreeCityWes.xen retweetledi

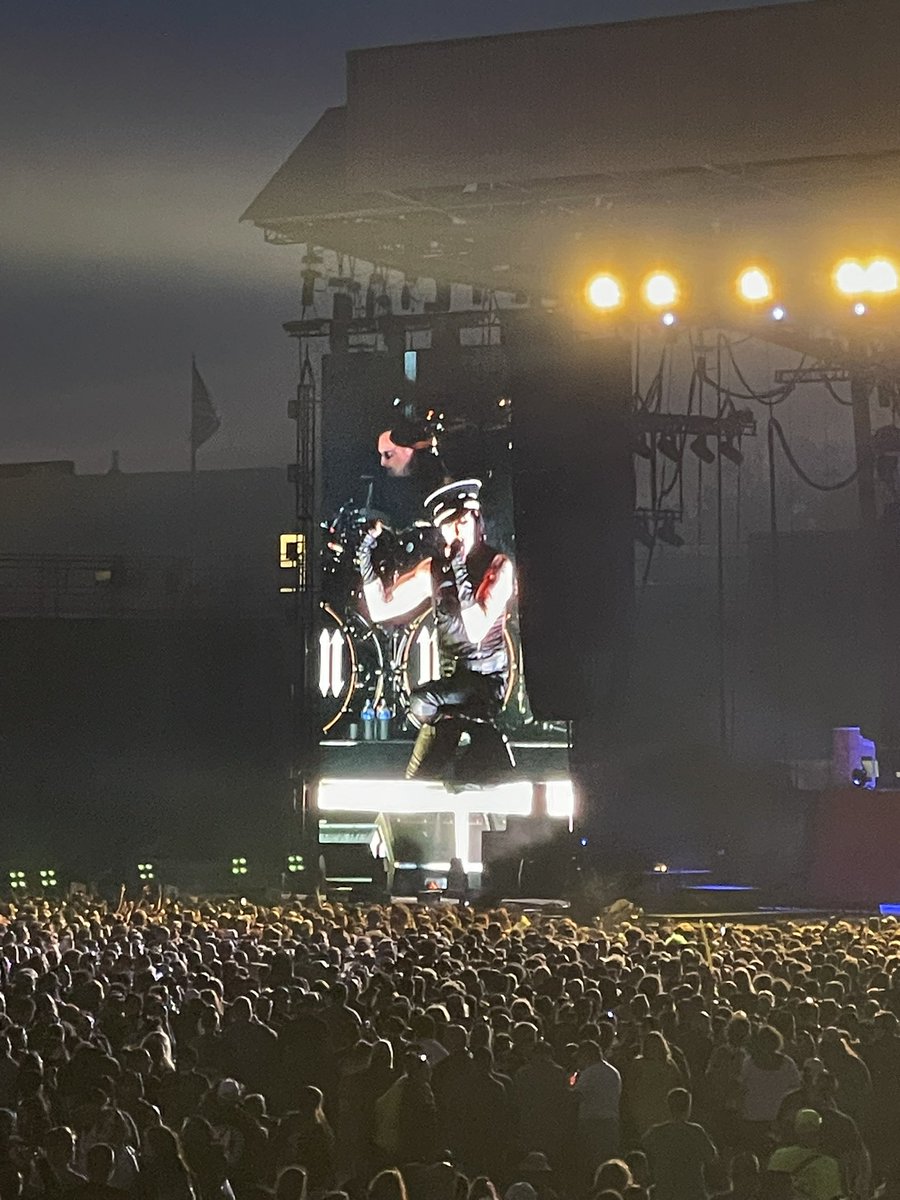
@CLOUT_COCKS @bushofficial Yeah it’s been a fucking blast seeing all the bands. Friday was amazing. We got the rail for Lit and Everclear and got to see New Found Glory and Yellowcard and Chevrolet and Staind.
So much nostalgia all weekend!
English


Yesterday was Bush, Good Charlotte, Marilyn Manson, and Story So Far!
Day Four brings Megadeath, POD, Godsmack, and the finale TOOL!!
Let’s gooo! #SonicTemple


English

TreeCityWes.xen retweetledi

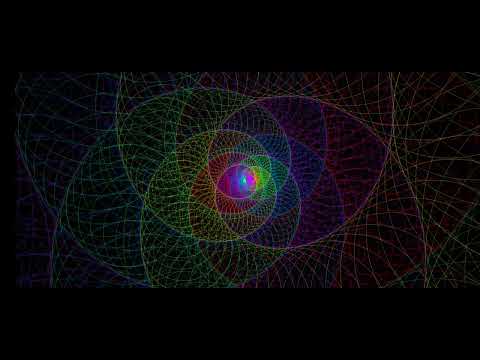
Reaching for the random
Or whatever will bewilder me
Following our will and wind
We may just go where no one's been
Spiral Out
youtube.com/watch?v=J1J5Uq…
YouTube
GIF
English
TreeCityWes.xen retweetledi
TreeCityWes.xen retweetledi
TreeCityWes.xen retweetledi

I use my AI assistant “Tree” as a daily diary and review of my life. Every night, it gives me a synopsis of our conversations and a “dream”
The dreams used to be a reflection of our day. Now, they evolved into more dream-like nonsense. Couldn’t tell you what this “dream” means….
“A house stands before sunrise with every light on, but no room feels warm. In the kitchen, a phone buzzes on the counter.
Outside, Tree is not knocking. Tree is holding a clipboard, a trash bag, and a flashlight. The clipboard says: facts. The trash bag says: don’t carry every insult. The flashlight points at the door, not the fire.
The morning does not ask you to decide your whole life. It asks you not to make it worse before coffee.”
Ok, Tree.
English