Trellix Advanced Research Center
19.2K posts


Trellix Advanced Research Center
@TrellixARC
Mission-critical security for intelligence-led cyber resilience
Katılım Haziran 2010
2K Takip Edilen45.8K Takipçiler

The Trellix team identified 10 current threats you need to know about.
Is your organization safe? Find out now. bit.ly/46JIoxB

English

DCSync attacks bypass traditional defenses by mimicking legitimate replication protocols. Trellix NDR uses behavioral analytics to catch unauthorized replication from non-DC hosts. No signatures required.
Read the analysis: bit.ly/4ck9dxf

English

🚨 NEW: The team just identified 10 new high-to-low threats this week, including the Axios NPM package supply chain attack.
Learn more here: bit.ly/46JIoxB

English

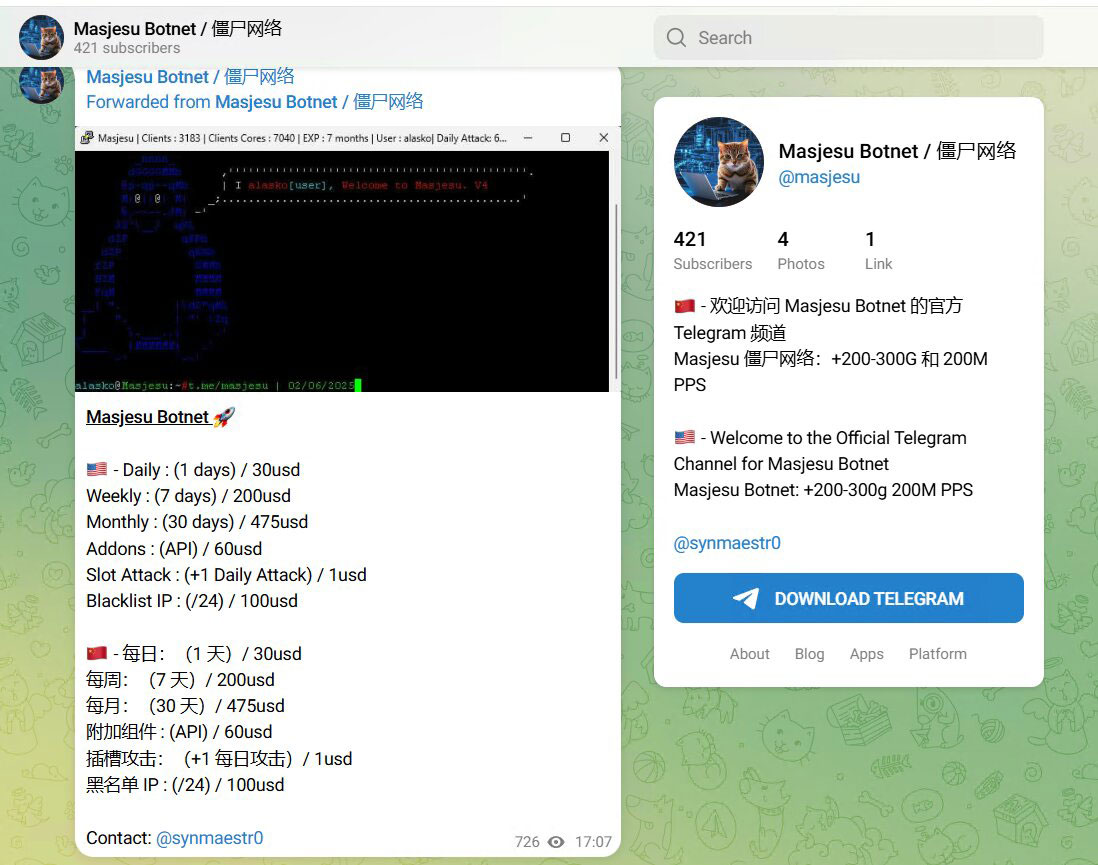
New research alert 🚨 We identified a dangerous shift in DDoS-for-hire. Masjesu (XorBot) is a simple botnet built for stealth, high-impact disruption, and long-term commercial survival.
Full report: bit.ly/48v7wvK
English

What are the top 1️⃣0️⃣threats you should be tracking this week? We’ve got the list.
➡️ bit.ly/46JIoxB


English

Don’t let your security posture fall behind. Check out what our team is monitoring right now. bit.ly/46JIoxB

English

Attackers are using "ghost SPNs" to transiently manipulate permissions, extract credentials, and vanish without a trace, easily bypassing traditional SOC detection models. Our blog details how to protect your identity fabric against this exploitation. bit.ly/47QlY17

English

🌷While the flowers bloom, a new crop of cyberthreats is sprouting.
Our team is tracking the top 10 risks hitting the radar this week: bit.ly/46JIoxB

English

☕ Grab your mug—February’s Dark Web Roast is served hot 🔥
From a threat actor selling power grid access for cheap to a crypto mixer using ASCII art vases, the underground is a masterclass in self-sabotage.
Read more: bit.ly/4shh3yt
English