Sabitlenmiş Tweet
Troy Hunt
121.2K posts


Troy Hunt
@troyhunt
Creator of @haveibeenpwned. Microsoft Regional Director. Pluralsight author. Online security, technology and “The Cloud”. Australian.
Australia Katılım Nisan 2008
1.3K Takip Edilen244.2K Takipçiler

@joostlek @haveibeenpwned Ah, I gotcha now. So the ability to query just your own email address by API? And a check every day to see if it’s been exposed? With fault tolerance, of course.
English

@troyhunt @haveibeenpwned The reason I'm not using it at the moment is that I can't really justify $4/month for something I also get an email about. And in theory I also don't need 1000 requests a month, I'd assume max 50 per email address (/24h + restarts)
English

Today, after many months of hard work, we're launching a bunch of new @haveibeenpwned features that improve privacy, usability and performance. We're a little team, but we've done a lot since this pic in November. Here are all the details: troyhunt.com/passkeys-k-ano…
English

@joostlek @haveibeenpwned I’ve used that integration myself and thought it was great! I don’t see how it could be made easier for its current purpose, unless you expand it laterally and start adding support for things like domain or k-anon searches.
English

@troyhunt @haveibeenpwned So hey Troy, as you're a Home Assistant user and as there's an Have I been pwned integration, is there something we can do to make the integration more accessible?
English

Weekly update is up! Join Me in Investigating Today’s Data Breaches With the PwnedClaw, the OpenClaw Agentic AI Bot Doing My Legwork: troyhunt.com/weekly-update-…
English

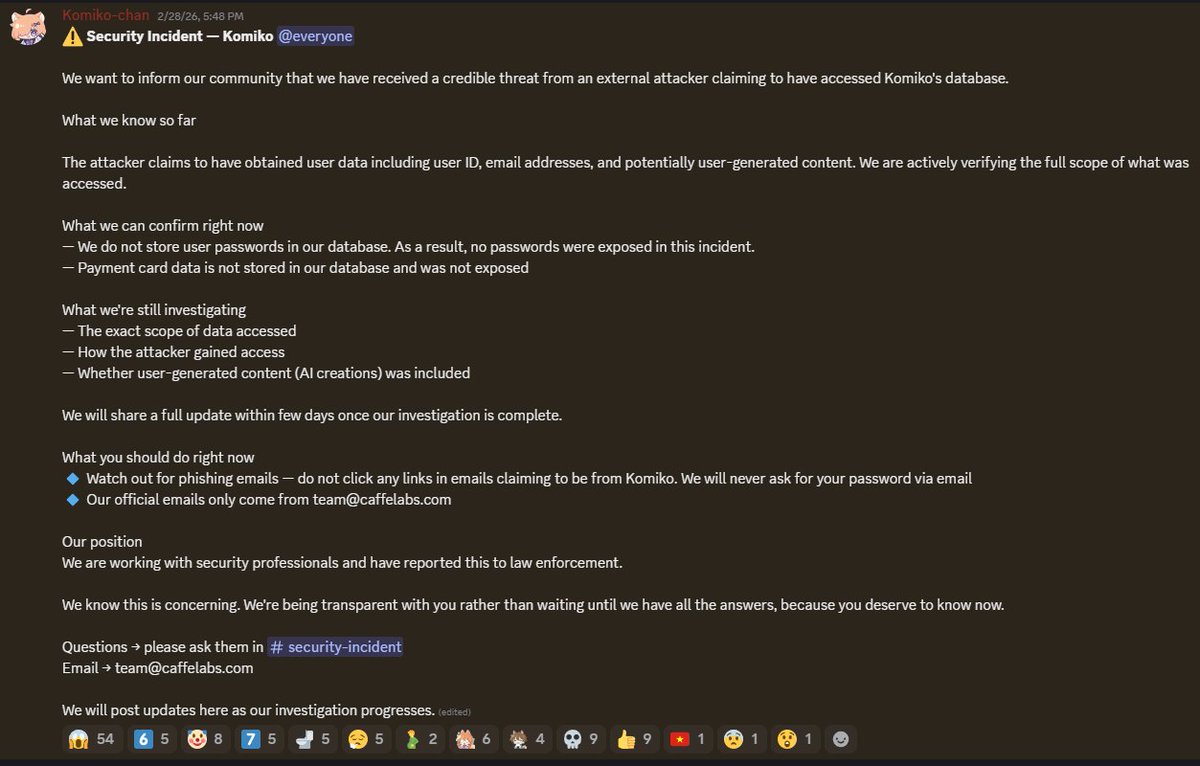
@carlodreyer @KomikoAI It’s a firm that offers AI services, but I didn’t see any evidence the security flaw was introduced by AI, classic human error AFAIK
English

Going live with my weekly vid in 5 minutes! Join Me in Investigating Today’s Data Breaches With the PwnedClaw, the OpenClaw Agentic AI Bot Doing My Legwork youtube.com/live/HQYSfszSz…

YouTube
English

@troyhunt are you aware of the crunchy roll data breach animenewsnetwork.com/news/2026-03-2…
English
Troy Hunt retweetledi

New breach: Today, a breach of one of the iterations of the BreachForums hacking forum known as "version 5" was publicly disclosed. Data included 340k unique email addresses, usernames and argon2 password hashes. 96% were already in @haveibeenpwned. More: haveibeenpwned.com/Breach/BreachF…
English
Troy Hunt retweetledi

New breach: In 2015, custom gaming controller maker Scuf Gaming suffered a breach that exposed 129k email addresses. Data also included username, display name, IP address and password hash. 88% were already in @haveibeenpwned. Read more: haveibeenpwned.com/Breach/ScufGam…
English
Troy Hunt retweetledi

New breach: Sound Radix had 293k unique email addresses breached in an incident they disclosed this week before self-submitting it to HIBP. Data included name and potentially hashed password. 76% were already in @haveibeenpwned. Read more: haveibeenpwned.com/Breach/SoundRa…
English

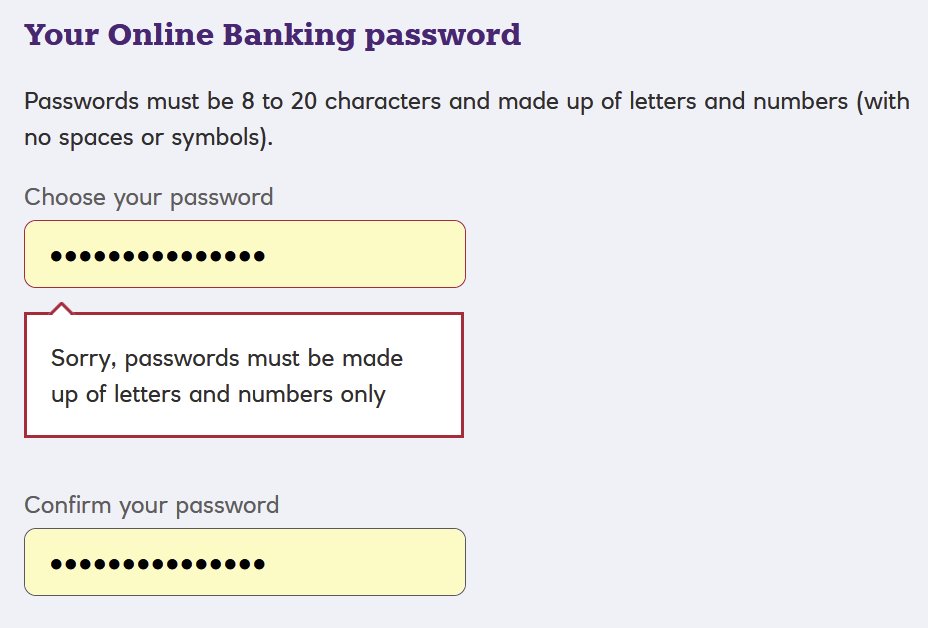
@JakubKonecki @NatWest_Help @troyhunt @ICOnews They advocate the use of special characters on their own website: natwest.com/fraud-and-secu… But then their online banking system forbids them, in 2026! It's f*ck*ng r*t*rd*d. @NatWest_Help @Grok
English

@NatWest_Help Is this a joke or a financial institution? 20 char limit and no special characters? Please tell me you are not storing the passwords in clear text!
@troyhunt @ICOnews
English

@charitablelwt Weird, first I’ve heard of it. I use it via Chrome on iOS all the time with no problem, wonder if it’s a Safari thing or a you thing?
English

@troyhunt not sure if youre aware but sometimes when i load hibp on ios safari it shows a white blank screen first and then after a refresh then loads the website im currently on ios 26.3
English

Weekly update is up! Baydöner Breach; Aura Breach; Building PwnedClaw Agentic AI on a Mac Mini to do Data Breach Stuff troyhunt.com/weekly-update-…
English

Massive headline number, let’s see what the reality actually is
Dark Web Informer@DarkWebInformer
‼️ The actor is claiming 590TB of data from OVHcloud in a shared file tree.
English

@Maetis @elormkdaniel @haveibeenpwned @Proton_Pass No idea! We’ve literally designed it so that we don’t know 🙂
English

Apple’s servers hold a database of hundreds of millions of hashed passwords from known data breaches around the world sourced from breach databases like Have I Been Pwned, which aggregates leaked credentials from thousands of incidents. When your hash prefix arrives, the server returns every hashed password in its database that starts with those same few characters. That could be hundreds of entries. Apple sends all of them back to your device.
Your device then does the final comparison locally. It checks whether your full hash matches any entry in that returned list entirely on your phone, without Apple ever seeing the complete hash or the original password (allegedly). If there’s a match, the alert fires. If there isn’t, nothing happens and nothing was exposed.
This means Apple’s server never received enough information to identify your password. It received a fragment; a prefix shared by hundreds of different hashes and returned a broad set of possible matches. The actual check happened on your device where only you have the complete picture (allegedly).
The breach database itself is maintained using data from security researchers, breach notification services, and publicly documented leaks. When a company gets breached and millions of credentials are dumped online, those passwords get hashed and added to the database. Your password is never compared against plaintext. It’s always hash against hash, prefix against prefix, with the final answer computed privately on your own device (allegedly).
Apple knowing your password was leaked is not the same as Apple knowing your password (allegedly). The entire system was designed so that those two things never have to be the same.
LORD DEBRAH@LordDebrah
WTF is this 🥺🥺.
English

It broke containment as soon as there were public references to it. Accounts like @IntCyberDigest then report on discussions that are already in the public domain. Here's a whole list of accounts that follow the same pattern: x.com/i/lists/796512…
IMHO, the biggest issue this highlights is that when there is a vacuum of information about a breach, the public will quickly fill it. I've always strongly advocated for breached companies to own the narrative by leading with their voice: CR would have known about this incident well in advance of any public discussion (Shiny Hunter's MO is to demand a ransom, let many days pass, then go public). They could have controlled the discussion from the outset.
That's not to throw CR under the bus - they're the first victims of this crime - but news spreads fast, and it will be the hackers' claims that make the headlines if you don't get on the front foot.
English

@troyhunt @LoremIpsumVerb @IntCyberDigest I also find it bizarre that CyberDigest would erroneously claim that Crunchyroll acknowledged the breach when they had merely responded that they had people looking into it.
English
Troy Hunt retweetledi

New breach: In around 2011, the now defunct RuneScape Boards exposed 223k unique email addresses. Data also included username, IP address and salted MD5 password hash. 96% were already in @haveibeenpwned. Read more: haveibeenpwned.com/Breach/RSBoards
English

I disagree with this take for many reasons: the threat actors involved here have a long track record of delivering on their claims. Accounts like @IntCyberDigest are always the first to pick it up, the more formal media outlets follow. CR may have already disclosed to a regulator, or may not yet have sufficient reason to do so. And “alleged” is clearly evident without the need to explicitly state it.
I trust this account to get early news on incidents like this, search for my background on why that’s probably significant.
English

@LoremIpsumVerb I appreciate you sharing the one caveat made, that's fair enough. But to my point again, there's only one source here -- someone with a clear financial gain from their narrative -- and there's not third-party validation for the evidence. You and I have very different standards
English

@TsengSR @Erlarnd @elormkdaniel @haveibeenpwned They don’t have to pay a cent, Pwned Passwords is free and open source. There’ll also be data sets we have that aren’t in other places (I.e. law enforcement feeds), wonder if those passwords are in there?
English

@Erlarnd @troyhunt @elormkdaniel @haveibeenpwned Knowing Apple, and big tech in general, you can bet your ass on it, that they just scraped hibp w/o paying a cent. Same as Facebook did download a whole shadow library (pirated books) to train their AI instead of paying licences.
English

@TsengSR @HAMZisworking @elormkdaniel @haveibeenpwned They wouldn’t have to, Pwned Passwords is all free and open source, including all the data
English

@HAMZisworking @troyhunt @elormkdaniel @haveibeenpwned If he has to ask, the answer is most likely a "no" ;)
English