User7472
15 posts



@Inifintyink @HuntressLabs @polygonben I understand why companies don't pay you. No one wants to deal with a crazy mf
English

@HuntressLabs, hey guys, you know right that having @polygonben employed poses a threat to your existing employees? god can have many punishments for people who know what will happen? Or how god could punish them, I recommend terminating him before god decides to punish them=)
English

@Inifintyink This is literally terrorism in the most primitive sense of the word lol. Time to stop buddy
English

@Ransom_DB Here you are able to see that we support cancer in the fight
English

🚨 Threat actor "Devman" publishes "CANCER" - Brazil 🇧🇷
@Inifintyink dafuq r u doing?
📍 Location: Brazil
🏢 Industry: Nonprofit Healthcare
🔗 Website: cancer.org.br
Fundação do Câncer is a Brazilian nonprofit founded in 1991 focused on cancer prevention, research, and education. It collaborates with the National Cancer Institute (INCA) and partners nationwide to develop programs aimed at controlling cancer across Brazil.

English

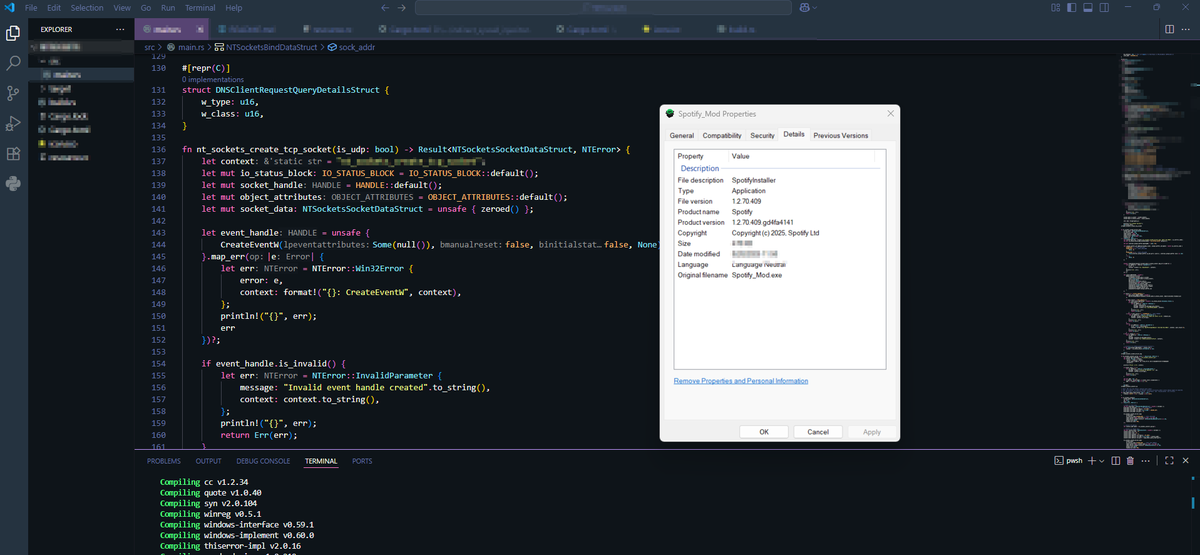
Someone found an RCE on my website yesterday.
CVE-2025-55182.
React2Shell.
I don't have a bug bounty program.
I never asked for a security assessment.
I woke up to a DM: "Hey I found a critical vulnerability in your site. I only ran the exploit to verify it worked. Here's my PayPal for the bounty."
Bounty?
I checked my logs.
Forty-seven requests to my RSC endpoint.
Something, something ... Prototype pollution payloads.
They used the GitHub script.
The one with 2,000 stars.
The one that runs id automatically "for verification purposes."
They spawned a shell on my production server.
uid=1001(nextjs) gid=65533(nogroup)
They took a screenshot.
They posted it on Twitter.
"Popped a Shell on a Live Website 🚀💀 #BugBounty #CVE-2025-55182 #YOLO"
They got 84781 likes.
My customers' data was on that server.
I asked them to delete the screenshots.
They said "I removed the domain name, you should be thanking me."
Thanking them.
For unauthorized access to my production infrastructure.
For running arbitrary commands on systems I own.
For posting proof of exploitation for clout.
They called it "responsible disclosure."
I called my lawyer.
They called me "ungrateful."
I called the FBI.
Now they're in my DMs explaining that "this is how the industry works" and I "don't understand pen testing."
A pen what?
I understand it perfectly.
I understand that running react2shell-ultimate.py against random websites isn't research.
I understand that "I removed the identifying info" doesn't undo the unauthorized access.
I understand that #BugBounty doesn't apply when there's no bounty program.
I understand that finding my site on Shodan doesn't constitute authorization.
Their followers are defending them now.
"Presumption of innocence."
"You don't know if it was authorized."
"The screenshots were redacted."
Three hundred people are calling me a bootlicker for reporting a crime.
Someone said I should be grateful they didn't deploy a cryptominer.
The bar is underground.
I just wanted to run a small Next.js app.
I didn't ask to be someone's proof-of-concept.
I didn't consent to being their "first"
I didn't sign up for an unscheduled penetration test from a stranger with a GitHub account.
There is no safe harbor for spraying public exploits at random websites.
There is no legal protection for "I was just verifying the vulnerability."
There is no ethical framework where unauthorized prototype pollution is a favor.
But sure.
Thank you for your service.
You found a CVE that was already public.
Using a tool someone else wrote.
Against a target that never authorized you.
And you posted about it on main.
For likes.
Hero.
English

@R3dVector @akaclandestine Man… Russia is a multinational country…
English

🚨Cyberattack Alert ‼️
🇮🇩Indonesia - Ransomware Group vs Ransomware Recovery Company
The newly discovered The Gentlemen ransomware group claims to have breached Recovery Ransomware Indonesia.
Place your bets.
Discover more at hackrisk.io

English