Paolo Stagno (VoidSec)
1.7K posts


Paolo Stagno (VoidSec)
@Void_Sec
Director of Research @Crowdfense. Windows Vulnerability Researcher and Exploit Developer, ex-@XI_Research


GitHub - orinimron123/CVE-2026-40369-EXPLOIT: Full exploit code for CVE-2026-40369 - A Windows kernel arbitrary write vulnerability that allows browser sandbox escape from all browsers render process sandbox · GitHub github.com/orinimron123/C…








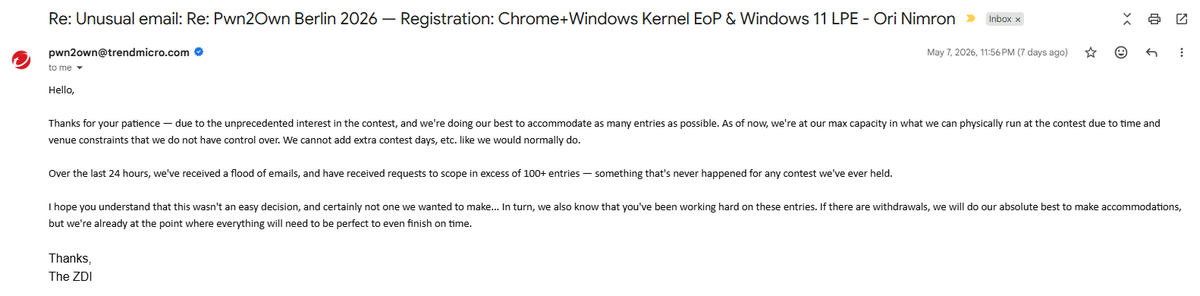




this year's pwn2own isn't just interesting because there will be lots of entries with AI+human. it is also interesting because a) anthropic burned a ton of tokens on firefox, basically running claude in a loop until it found something for a month, probably exhausting whatever claude can one shot. b) if someone submits full chain without much use of ai, it tells you one shotting plateaus and these models are bit like fuzzers than seasoned security reseachers. c) even if they used an llm to find the bug, this tells us scaffolding/harnesss design, prompting, and the operator matters a lot.





Bug count != exploitable bug. Finding != chaining. LLMs are exceptional at pattern recognition on known bug classes. They are not reasoning about novel failure modes in complex multi-component systems. The hard bugs still require humans. voidsec.com/ai-vulnerabili…





Finally back to the forge. ⚒️ I revisited an old friend, #CaddyWebServer, and forged kCaddy: a malleable Caddy redirector for #RedTeam ops. New post: proxying and obfuscating #Evilginx with M365, Google, and Okta phishlets. knifesec.com/blog/kcaddy-re…