Yeeb
568 posts


Yeeb
@Yeeb_
Penetration tester, red teamer and capture the flag player with incident response experience.


What I see in cybersecurity: AI has re-invigorated an industry that was largely stale for the past ten years. Complete new green field. Changes everything. New innovation happening everyday. Need to adapt or be left behind. This reminds me of the early 2000s, it’s exciting, addicting, and it’s going to be fun as hell.


If #RBCD has been thoroughly documented, only a few resources mention the workflow in cross-domain environment. In our new blogpost, we dive into the cross-domain and cross-forest RBCD workflows. Read it here 👇 synacktiv.com/en/publication…











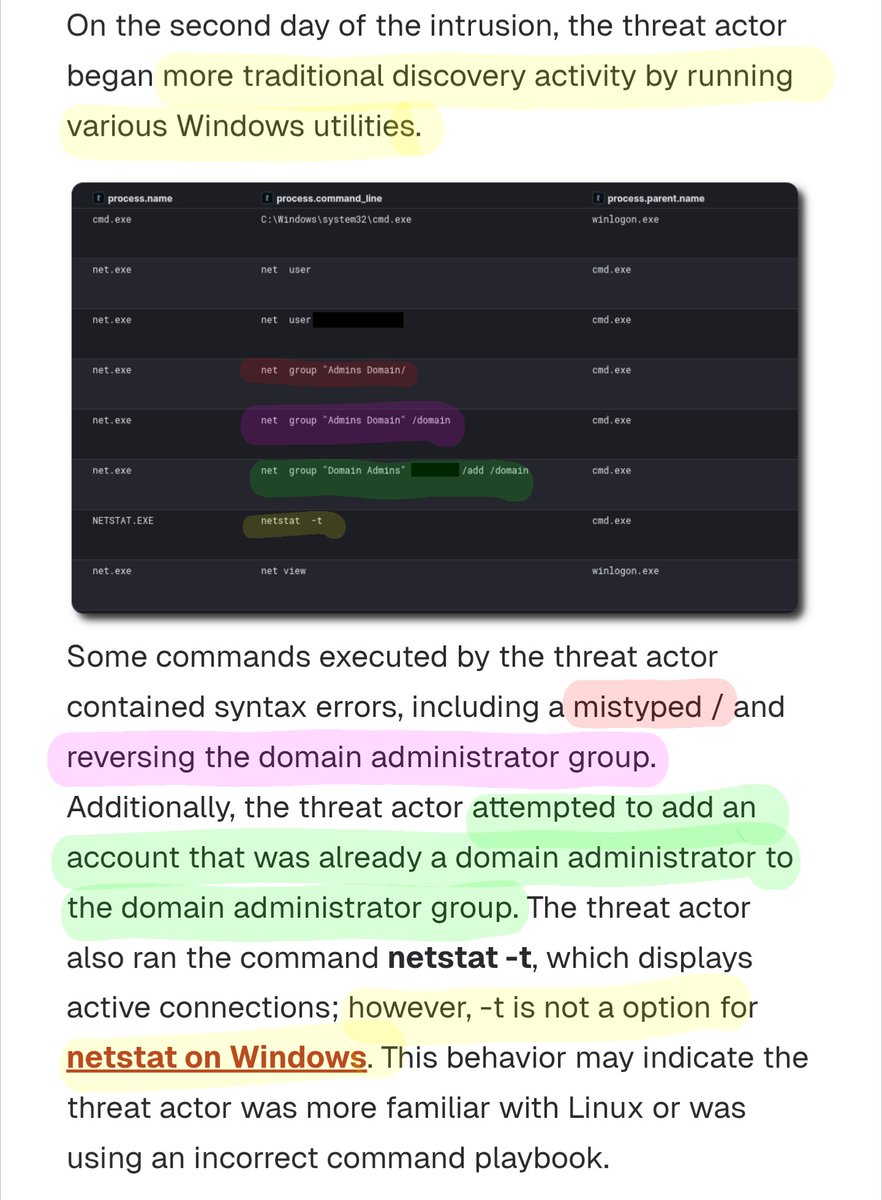
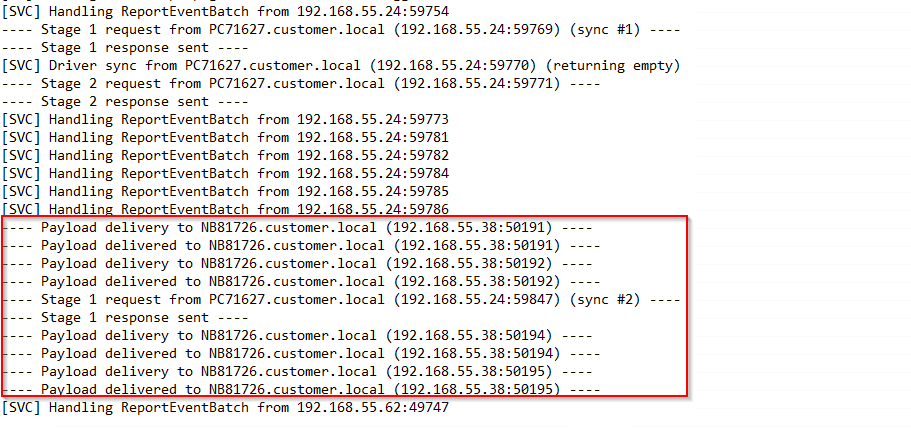
🌟New report out today!🌟 Apache ActiveMQ Exploit Leads to LockBit Ransomware Analysis and reporting completed by @malforsec, @lapadrino, and @PeteO. 🔊Audio: Available on Spotify, Apple, YouTube and more! thedfirreport.com/2026/02/23/apa… #DFIR #DigitalForensics #BlueTeam