Sabitlenmiş Tweet

الحمدلله
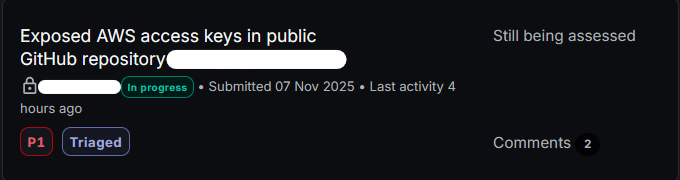
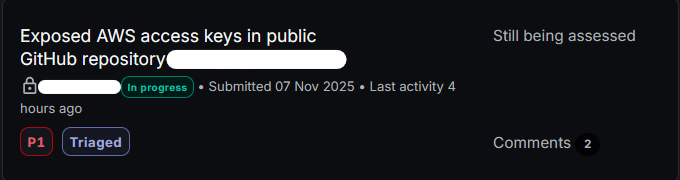
Found exposed AWS keys in a public repo
report triaged on @Bugcrowd .
Using Github Dork:
org:Target aws_access_key_id
Mahmuud Ayman
378 posts


@_0xhero1
Penetration tester || Bug hunter @bugcrowd







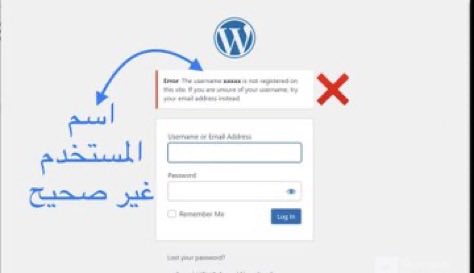

سلسلة كل يوم شرح ثغرة بسيطة : Day2 Session Fixation ثغرة: اختبارها: ١- سجل دخول لحسابك بالموقع نفذ اي اجراء على حسابك كتعديل بريد ..الخ ٢- اعترض الطلب او راقب الرابط من المتصفح تاكد من وجود رمز الجلسة بالURL ٣- افتح الرابط مع رمز الجلسة بمتصفح مخفي اذا تم دخولك لحسابك تقدر تبلغ المكافاة من ٤٠٠ الى ٢٥٠٠$ او على حسب البرنام