Sabitlenmiş Tweet

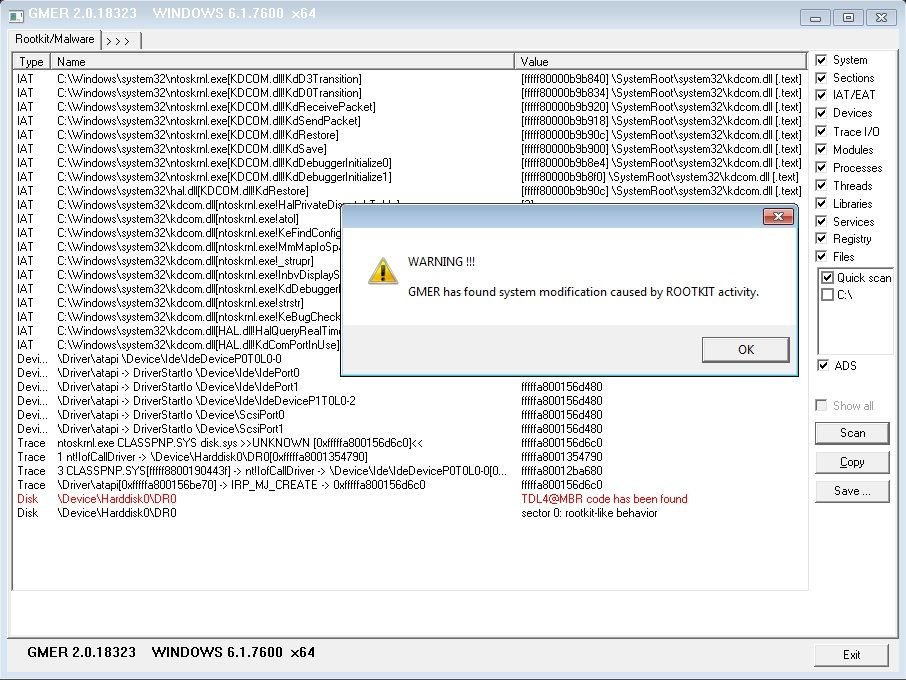
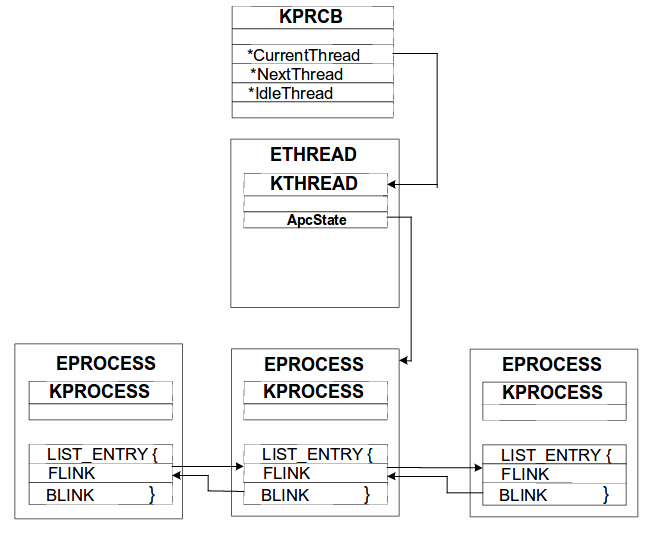
I'm proud to release my first Google Chrome RCE derived from the most fascinating and mind bending exploit I have yet analyzed: CVE-2019-13720 Wizard Opium. This is a beautiful bug which I have crafted into an exploit bypassing ASLR, CFG and CET on Win10 github.com/forrest-orr/Wi…

English