Gabriel Prostitis
20 posts

Gabriel Prostitis
@___prosti
CTF player for @TheRomanXpl0it and @towerofhanoi student at @polimi



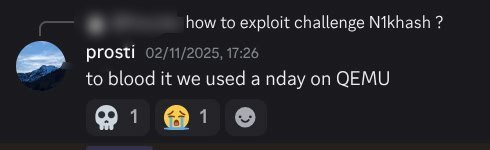
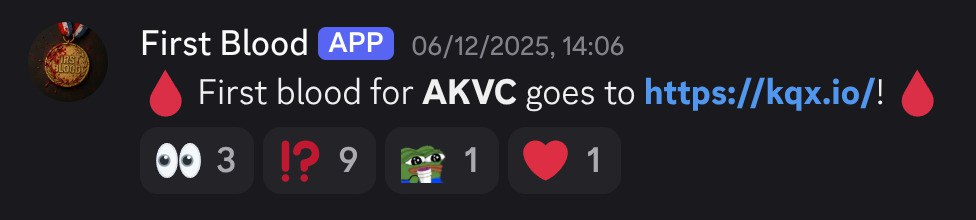
played DiceCTF quals and managed to blood the kernel pwn challenge and won the $150 bounty! check out the writeup: kqx.io/writeups/corne…




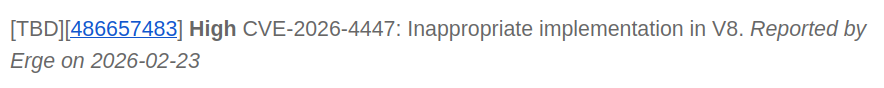
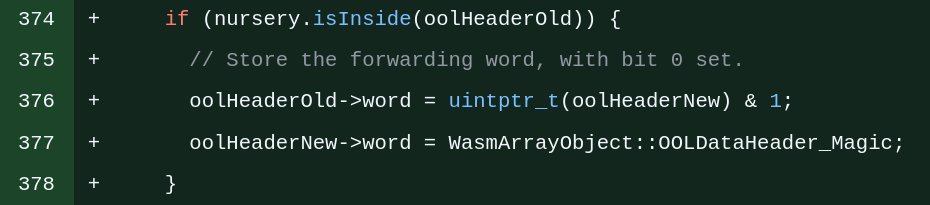
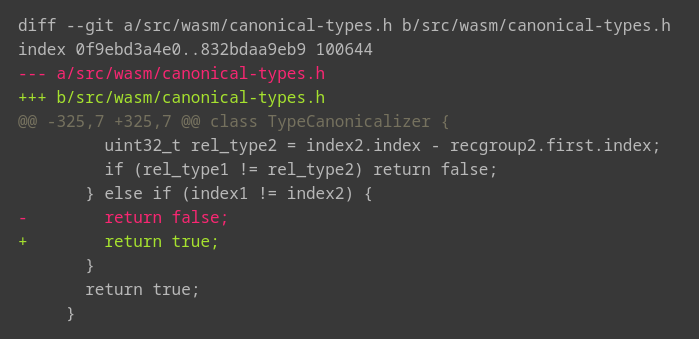
How a single typo led to RCE in Firefox Can you spot the bug? Read now at: kqx.io/post/firefox0d…





The fox caught fire??? New blog post very soon at kqx.io 6b2f0f9f754952d956cab1a6922c920664d2636c192db4db614866345369a888





It wouldn‘t really be #DefCamp without the #HackingVillage. A huge round of applause for everyone who joined our competitions! Whether you took home a prize or new insights, we hope you had an amazing time!


corCTF 2025 has ended! Congrats to the top 5: 1. @FlatNetworkOrg 2. @r3kapig @ProjectSEKAIctf 3. The Amazing Digital Orange 4. @TheRomanXpl0it 5. STM Thank you to all of our players and sponsors! @osec_io, Research Innovations, @ret2systems, @trailofbits, @vector35, @googlecloud