Sabitlenmiş Tweet

It’s been a busy last few weeks!
Check out our analysis on PIPEDREAM - the 7th malware family to target industrial control systems.
It was a fun (at times crazy) project to work on!
dragos.com/blog/industry-…
English
Sam Hanson
398 posts


@__samhanson__
Malware hunting/analysis and vulnerability research at Dragos.











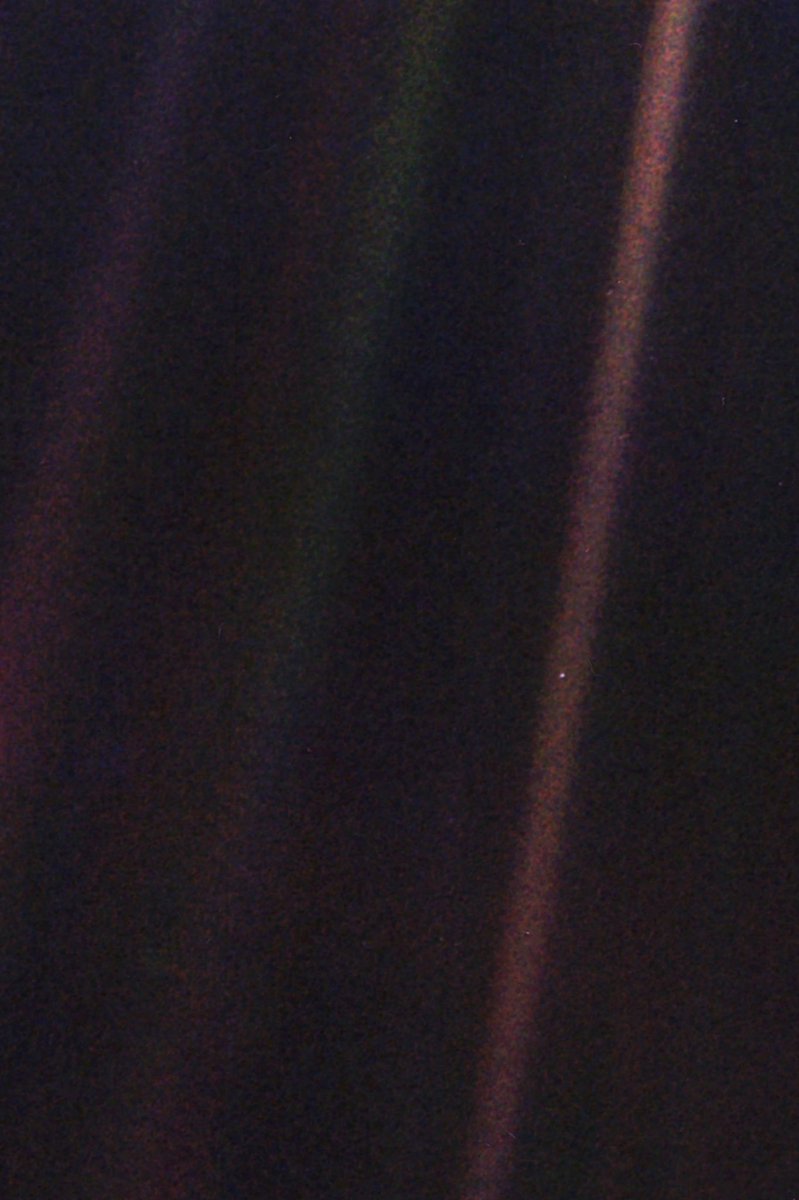
In your opinion, what is the single greatest photograph in history?