coop
78 posts


coop
@_cooperton
i click keys on a keyboard but in a specific order @_darkmatterlabs
Los Angeles, CA Katılım Eylül 2009
439 Takip Edilen126 Takipçiler

you panic sell because you hold too many positions - how can you have conviction for 10 different positions at once?
coop@_cooperton
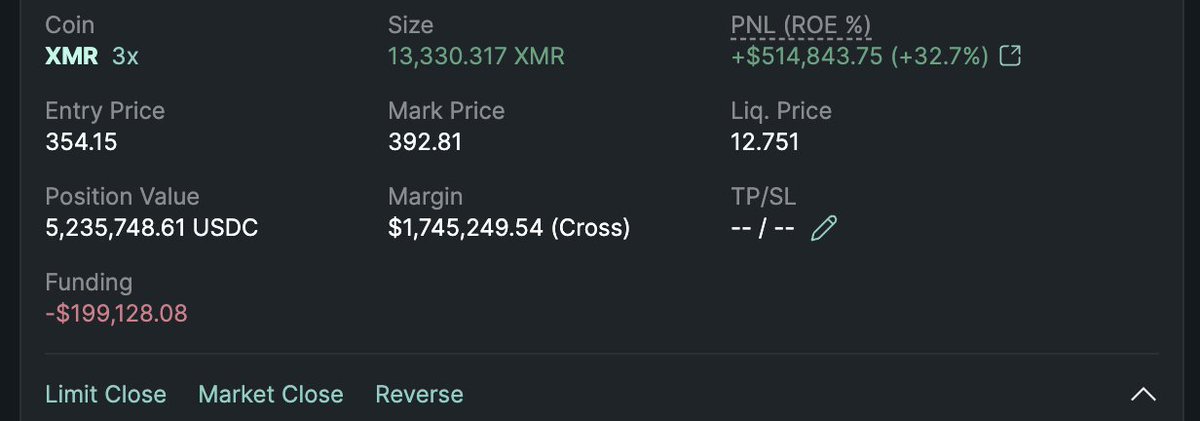
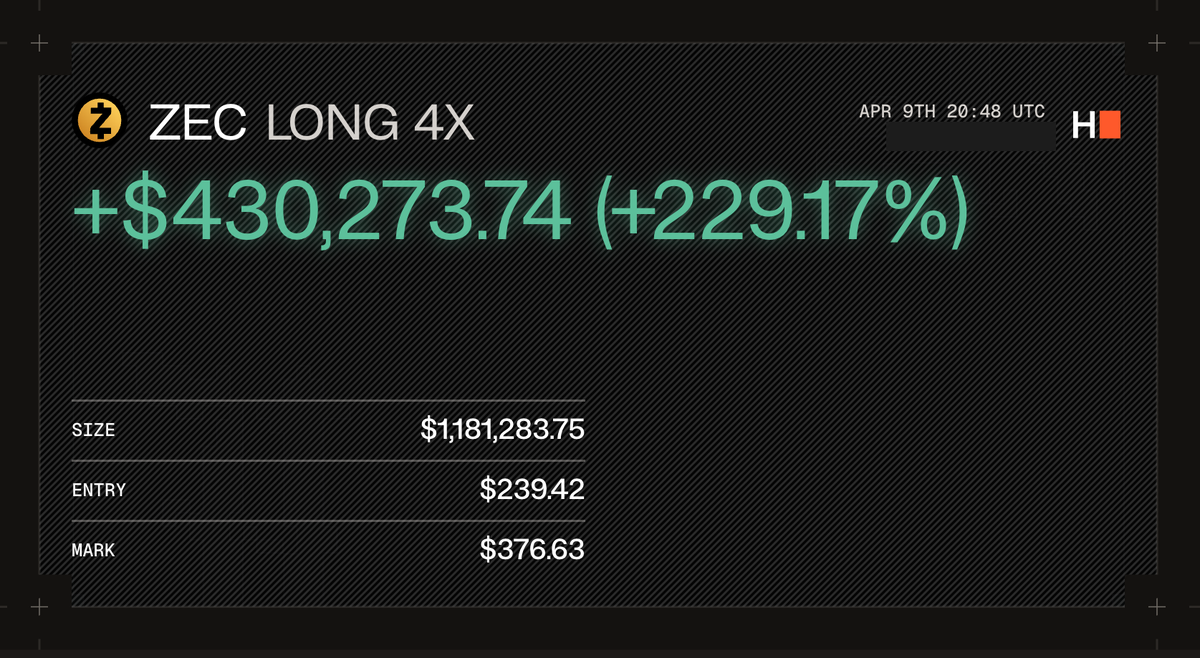
prediction: XMR/ZEC outperform BTC/ETH in 2026
English

> (notably, we hold the view that it is not appropriate to refund users who entered their wallet’s seed phrase, as this is not behavior that impersonates CoW Swap – or any DEX for that matter)
Seriously?! the interface on swap.cow.fi - at least on mobile where we were affected - stole seed phrases by posing as part of the parent web3 browser. that’s like if the connect wallet button on a browser was able to launch a native keychain prompt that prompted for a password. i would argue that is way worse as it capitalizes on that “autopilot response” that makes exploits like this so successful.
i’m very surprised by this, and am almost wondering if this is specifically trying to single us out since we were the biggest loser and accounted for half the losses. in which case couldn’t you guys at least have offered a partial refund? not to mention that we’ve probably generated more than 50% our loss in revenue for cowswap..
there’s at least 10 different ways you guys could’ve gone here that makes more sense. at least including us in the conversation being one of them
English

User protection is a core promise of CoW Swap.
We are therefore proposing a discretionary grants program so that victims of the April 14 DNS hijacking incident can be made whole as quickly as possible.
Proposal details can be found on the CoW DAO forum, here: forum.cow.fi/t/cip-draft-di…
Note that because of the high sums involved in the incident, this proposal will need to pass governance to go into effect. Please signal your support or give feedback directly in the forum.
English

this only happens with conviction
coop@_cooperton
prediction: XMR/ZEC outperform BTC/ETH in 2026
English

@_cooperton @safe it's referencing a post further up that thread about the multisig upgradeability
English

Update on Safe{Wallet} Restart
The Safe{Wallet} UI displayed the correct-appearing transaction information according to ByBit, yet a malicious transaction that had all valid signatures was executed onchain. Our investigation so far shows:
• No codebase breach found: The Safe codebase was checked thoroughly, and no evidence of a breach or modification was found.
• No malicious dependencies identified: No signs of a malicious dependency in the Safe codebase affecting the transaction flow (i.e. supply-chain attack).
• No unauthorised access to the infrastructure was detected in the logs.
• No other Safe address has been affected
As stated earlier, we have paused Safe{Wallet} functionalities temporarily to ensure absolute confidence in our platform’s security. Although our investigation shows no evidence that the Safe{Wallet} frontend itself was compromised, we’re conducting a thorough review.
Some of the actions include:
• Reviewing all of our service configurations
• Rotating all our infrastructure credentials
• Rebuilding our containers and reapply all our configurations
• Conducting a codebase audit with external security researchers
We are committed to bringing Safe{Wallet} back up as soon as possible.
English






