Sabitlenmiş Tweet
krp
53 posts


krp
@_kripteria
Red Team at @BlackArrowSec https://t.co/hysiudD7Wk
Katılım Ekim 2022
103 Takip Edilen66 Takipçiler
krp retweetledi
On our way to Switzerland 🇨🇭, where tomorrow @ineesdv will present our research at @1ns0mn1h4ck on abusing calendar invite processing in modern email clients.
➡️ Read more: insomnihack.ch/talks/meetings…

English
krp retweetledi

Phishing now happens in meetings as well? @ineesdv say yes! Understand how attackers exploit collaboration tools with this new #Insomnihack talk.
Buy your ticket now: ow.ly/yBis50Ya55M
#InsomniHack #Cybersecurity #INSO26

English

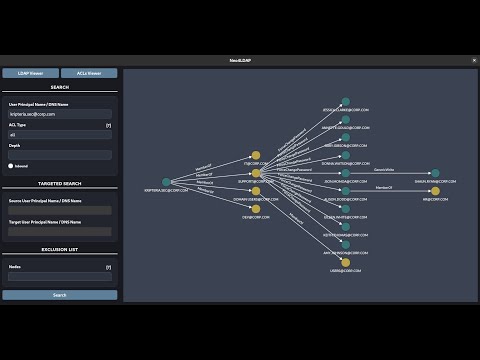
Este fin de semana estuve por @h_c0n hablando sobre la metodología y diseño de herramientas basadas en grafos de ataque sobre Directorio Activo, donde presenté Neo4LDAP y sus enfoques alternativos a Bloodhound.
Ha sido una experiencia muy gratificante que espero poder repetir🙂

Español
krp retweetledi

Charla de Alejandro Rivera aka @_kripteria sobre la transformación de nTSecurityDescriptor a grafos de ACLs, limitaciones de Bloodhound y presentación de Neo4LDAP con soluciones técnicas avanzadas.
#hc0n2026


Español
krp retweetledi
Just over 24 hours until @_kripteria takes the stage at @h_c0n to revisit the design and methodology of attack graphs in Active Directory, showcasing new approaches with Neo4LDAP.
English
krp retweetledi

🚀 Once again, the @Tarlogic team will be at @h_c0n! Next Saturday at 3:00 p.m., @_kripteria, Red Team Operator at @BlackArrowSec, will give a talk on the transformation of nTSecurityDescriptor to ACL graphs, Bloodhound limitations, and present Neo4LDAP.

English

Querying AD in BloodHound usually means learning Cypher. What if we could use a language we know, like LDAP? This post explains how this was made possible by translating LDAP queries to their Cypher equivalents while keeping BloodHound compatibility.
@kripteria.sec/goodbye-cypher-hello-ldap-querying-neo4j-with-neo4ldap-5e6466426a01" target="_blank" rel="nofollow noopener">medium.com/@kripteria.sec…
English
krp retweetledi

Hi! I just published a technical deep dive into a complex and fun N-day vulnerability that allows to get RCE in a very popular e-commerce platform.
Check it out!
hiddeninslack.github.io/posts/from-sst…
English
krp retweetledi

Tangled is a social engineering platform that weaponizes calendar event processing in Outlook and Gmail to deliver spoofed meeting invites that are automatically added to a user's calendar without interaction.
github.com/ineesdv/Tangled
Technical breakdown: tarlogic.com/blog/abusing-c…
English
krp retweetledi
Meetings You Didn’t Plan, But We Did
In this post, @ineesdv breaks down how calendar event processing in Outlook and Gmail can be abused to deliver spoofed meeting invites that are automatically added to a user's calendar without interaction
➡️Read more: tarlogic.com/blog/abusing-c…

English

El 7 de Febrero estaré por h-c0n dando una ponencia donde se examinará a bajo nivel cómo herramientas como BloodHound recolectan y procesan datos de Active Directory. También se presentará Neo4LDAP y se hablará de sus capacidad técnicas y soluciones :)
h-c0n.com/p/agenda2026.h…
Español

Overly complex ACL graphs? Neo4LDAP now helps you prioritise attack paths without losing visibility.
• Editable ACE weights
• Shadow Relationships
Details + PoC 👇
@kripteria.sec/finding-optimal-attack-paths-in-active-directory-with-neo4ldap-3d2158419f35" target="_blank" rel="nofollow noopener">medium.com/@kripteria.sec…
English
krp retweetledi
This Thursday, our colleague @_Kudaes_ will be at @NavajaNegra_AB presenting Activation Context Hijack: a new code execution technique for Windows environments.
➡️ More info: navajanegra.com/2025/speaker/k…

English
krp retweetledi

Im happy to announce Neo4LDAP — a query and visualization tool focused on Active Directory environments.
It combines LDAP syntax with graph-based data analysis in Neo4j, offering an alternative approach to tools like BloodHound.
youtube.com/watch?v=5V22K3…
🧵: 1/4
YouTube
English
krp retweetledi
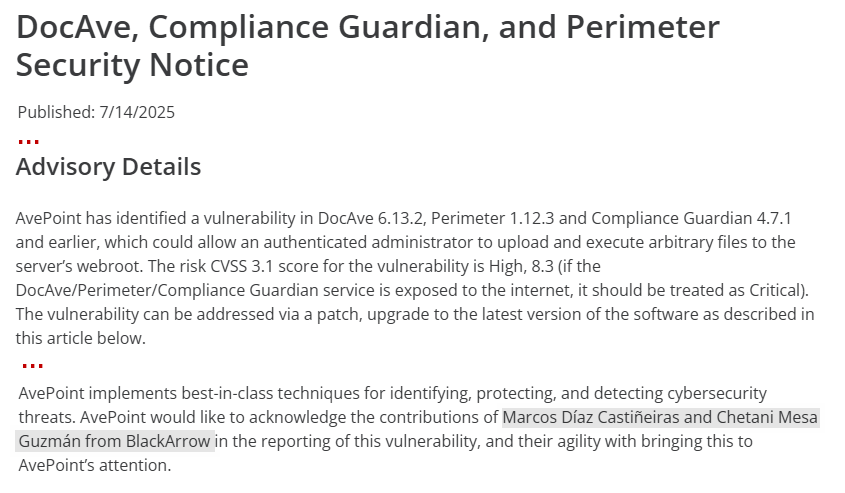
AvePoint has fixed a vulnerability in DocAve, Perimeter and Compliance Guardian discovered by our researchers @m1ntko and @Calvaruga.
This vulnerability can be used to achieve Remote Code Execution (RCE) in affected systems.
➡️ Advisory: avepoint.com/company/docave…
English

New major update!
The parsing and ingestion process now uses a concurrent method
Indexes are now used to optimize search queries.
This update reduces processing time from several hours on a db with 3 million relationships to ~40s.
github.com/Krypteria/Neo4…
English

Support for logging into different databases has been added, which is useful when using neo4j-enterprise :)
github.com/Krypteria/Neo4…
English


