Sabitlenmiş Tweet
Filip Skokan
477 posts


Filip Skokan
@_panva
Identity, OpenID Connect, OAuth 2.0, SSO, Authorization, Authentication, Technical Standards. Node.js core collaborator and TSC member.
Czech Republic Katılım Mart 2019
129 Takip Edilen676 Takipçiler

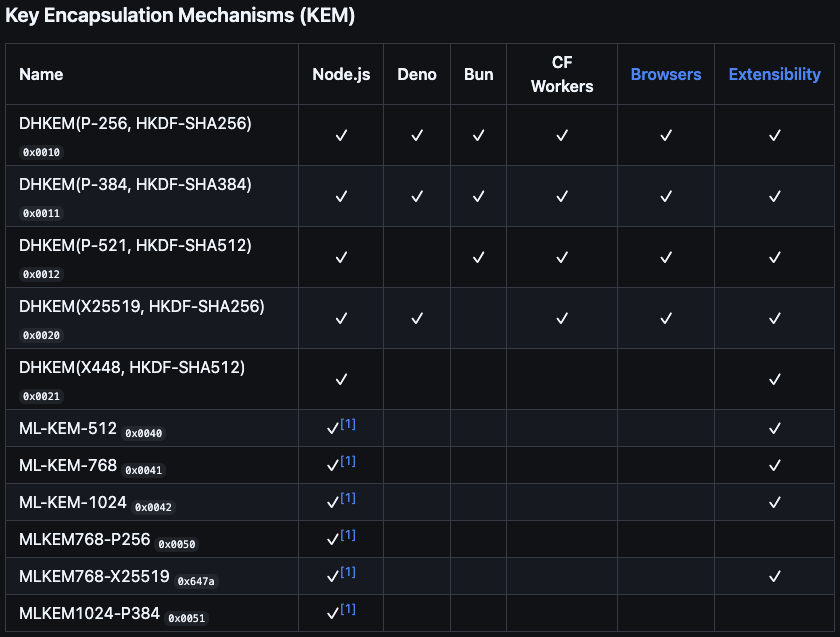
Time to catch up with wicg.github.io/webcrypto-mode… @bunjavascript @deno_land @Cloudflare
WPTs are available. Browsers started going through their implementations.
These algorithms power HPKE implementations (github.com/panva/hpke)


English

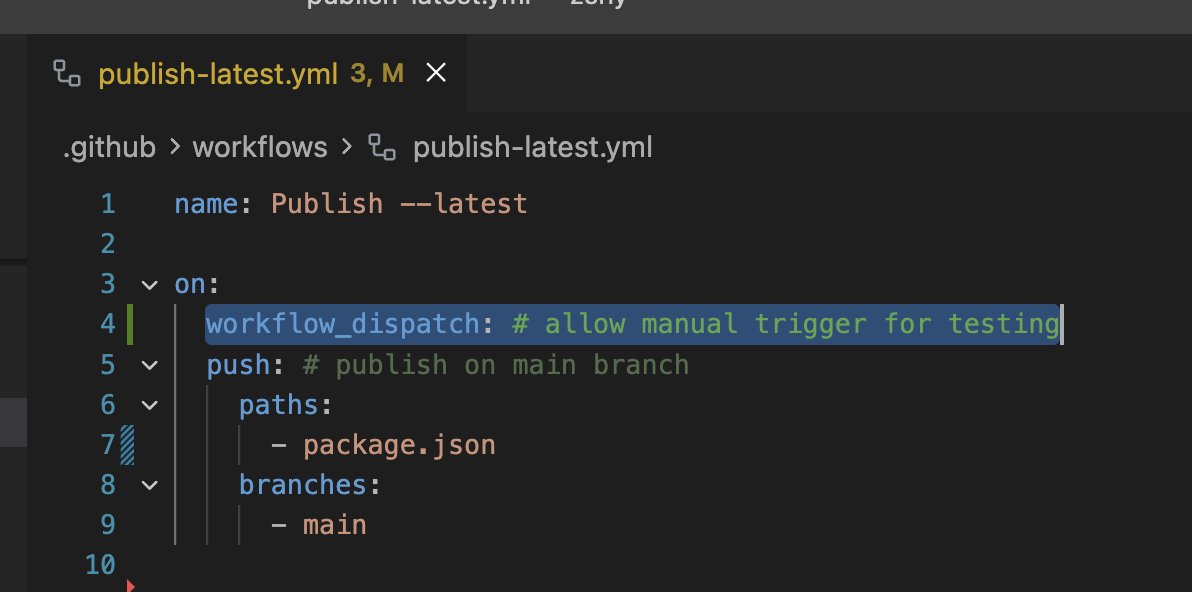
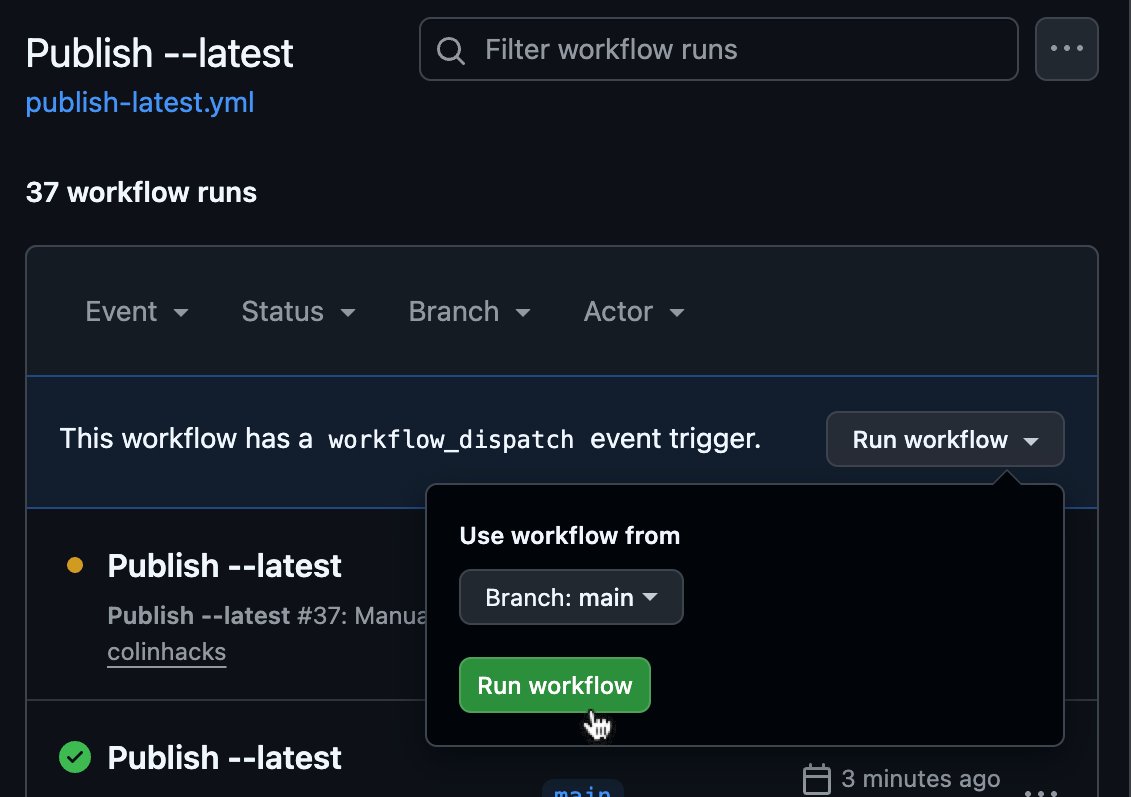
@colinhacks A _button_? It gives so much more cli.github.com/manual/gh_work…
English

HPKE vector validation in *your* browser (and the implementation project's github actions pipeline)
panva.github.io/hpke/
English

Let's get some ⭐⭐⭐ going 🙏
github.com/panva/hpke
Hybrid Public Key Encryption (HPKE) for Node.js, Browser, Cloudflare Workers, Deno, Bun, and other Web-interoperable runtimes.
Fully tree-shakeable. Fully typed. Extensible.
Filip Skokan@_panva
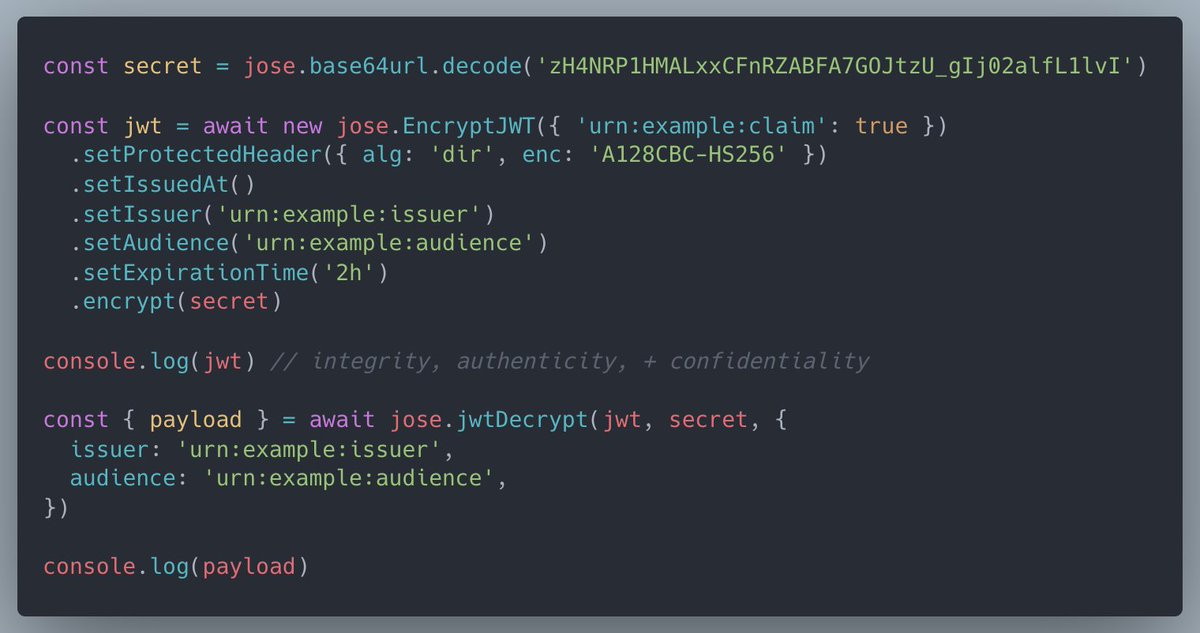
I've been hammering on a new, 0 dependency, runtime-native-only crypto, module that runs everywhere*. Hard to Predict, Keeps everything Encrypted.
English

@feross is there a list of detected typosquatted malicious packages?
English

@matteocollina @CVEnew Had GitHub staff from the Secure Open Source Fund who are on the CVE board look into it weeks ago. The resolution as disputed is final as per the "process" and cannot change to rejected. Despite it being factually incorrect. No appeal.
English

💬 It's partly because of @balazsorban44's projects' needs and the poor state of Vercel Edge Runtime Node compat at the time that we now have jose, openid-client, and oauth4webapi with no dependencies entirely built on top of Web Platform APIs such as Fetch and Web Cryptography.
Balázs Orbán@balazsorban44
This is a bittersweet moment, but given the time and energy I've been able to dedicate to the project lately, it feels like the right decision I followed @bekacru from the start and I think he is the right person to trust with Auth.js I am officially no longer the maintainer
English

The @npmjs name dispute process does not work anymore. It used to but no longer does. I have 3 npm pkg name claim disputes open for package names that see no downloads or activity since more than a decade ago. Tickets open for over a year with no response.
English