Q5Ca
244 posts


Q5Ca
@_q5ca
Chief Remote Work Officer at @u0Kplusplus
Vietnam Katılım Kasım 2017
395 Takip Edilen957 Takipçiler
Sabitlenmiş Tweet

Happy to share that my colleague @vudq16 and I will be speaking at PHDays in Moscow 🇷🇺 next week, May 24th. I’ll share a story from one of our red team projects, with techniques to maximize stealth during the operation.
Hope to make new connections there:D
phdays.com/en/forum/progr…
English
Q5Ca retweetledi

Locked in! Le Duc Anh Vu (@vulda17) of Viettel Cyber Security (@vcslab) exploited Cursor, earning $30,000 and 3 Master of Pwn points. Full win! #Pwn2Own #P2OBerlin

English
Q5Ca retweetledi

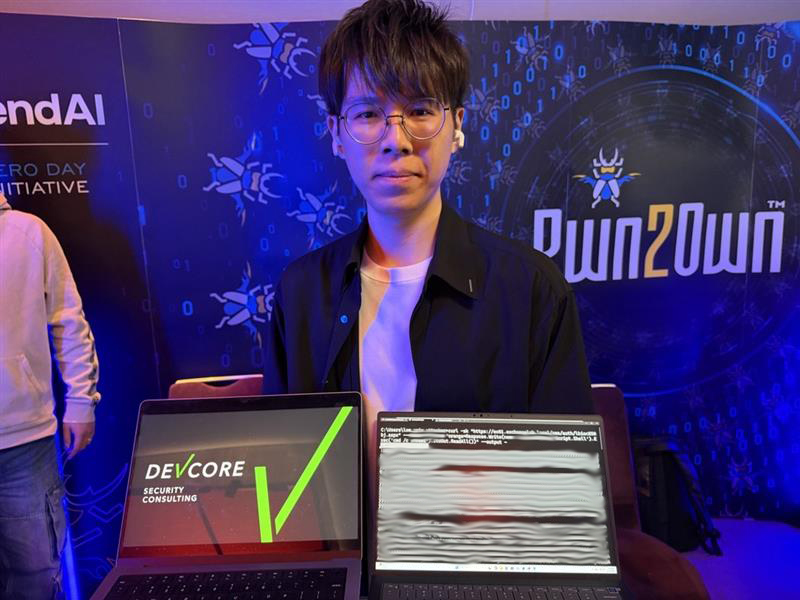
Aaaand it's official! Orange Tsai (@orange_8361) of DEVCORE Research Team chained 3 bugs to achieve Remote Code Execution as SYSTEM on Microsoft Exchange, earning a whooping $200,000 and 20 Master of Pwn points. Full win! #Pwn2Own #P2OBerlin
English
Q5Ca retweetledi

There it is! Orange Tsai (@orange_8361) of DEVCORE Research Team was able to exploit Microsoft Exchange! If confirmed, they win a whooping $200,000 and 20 Master of Pwn points. Off to the disclosure room to explain how they did it and seal the deal. #Pwn2Own #P2OBerlin
English
Q5Ca retweetledi

Boom! @rewhiles of Viettel Cyber Security was able to exploit Anthropic Claude Code! If confirmed, they win $40,000 and 4 Master of Pwn points. They're off to the disclosure room to explain how they did it. #Pwn2Own #P2OBerlin
English
Q5Ca retweetledi

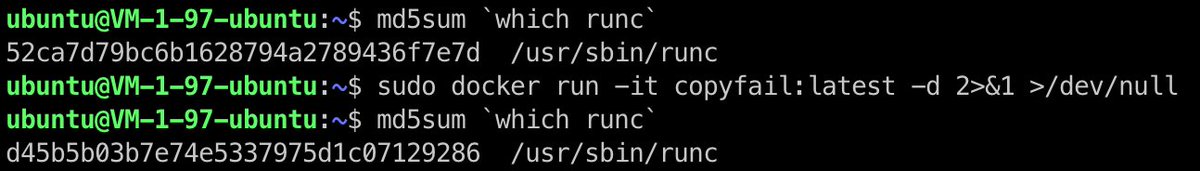
That's my chain — a full chain w/ logic bugs only! No memory corruption, no AI, and of course no collisions at all 😉
TrendAI Zero Day Initiative@thezdi
Confirmed! Orange Tsai (@orange_8361) of DEVCORE Research Team (@d3vc0r3) chained 4 logic bugs to achieve a sandbox escape on Microsoft Edge, earning $175,000 and 17.5 Master of Pwn points. Full win! #Pwn2Own #P2OBerlin
English

@D1iv3 Thanks for the hint. Allow me to farm some aura 😉 gist.github.com/Q5Ca/586fa0a18…
JFYI, codex 5.4 xhigh implemented most of it.
English

Microsoft isn’t paying a bounty because this related to “enterprise copilot” which apparently isn’t covered? I don’t even know what that means… I have an M365 copilot license and a P1 license lol. What are they talking about.

Zack Korman@ZackKorman
Microsoft isn’t disclosing this so: M365 Copilot allowed users to access files without producing an audit log. All you had to do was ask Copilot to not link to the file. You don’t even have to ask; it sometimes just happens. If your org uses Copilot your audit log is likely wrong
English

@haxor31337 @_q5ca Hi @haxor31337 it was a great talk loved it totally 🙌 also I have a question when you used ActivitySurrogateSelector gadget it prompted almost 16k+ characters payload and you mentioned that the querystring supports 2048 characters did you tried to use -minify option in ysoserial
English

From SSRF to RCE and transfer money in core banking.
It is really cool red team case. A perfect combination of external and internal vulnerabilities for each other to bypass the monitoring and detection of the blue team.
Present by my colleague @_q5ca
youtu.be/xBnMrNCuO_w?si…

YouTube
English

Happy to share that my colleague @vudq16 and I will be speaking at PHDays in Moscow 🇷🇺 next week, May 24th. I’ll share a story from one of our red team projects, with techniques to maximize stealth during the operation.
Hope to make new connections there:D
phdays.com/en/forum/progr…
English

Just a quick reminder: Copilot on microsoft365.com (m365.cloud.microsoft/chat) is not on scope for bounty 🥲
duongq5ca.substack.com/p/another-micr…

English