
mthcht
136 posts


@mthcht2
Threat Hunting - DFIR - Detection Engineering

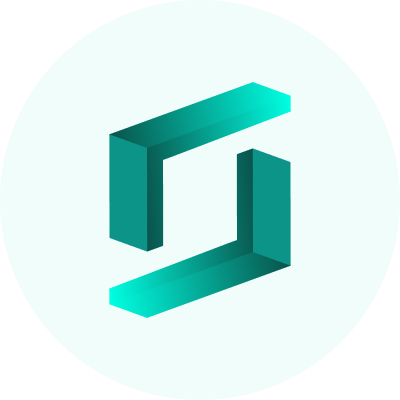




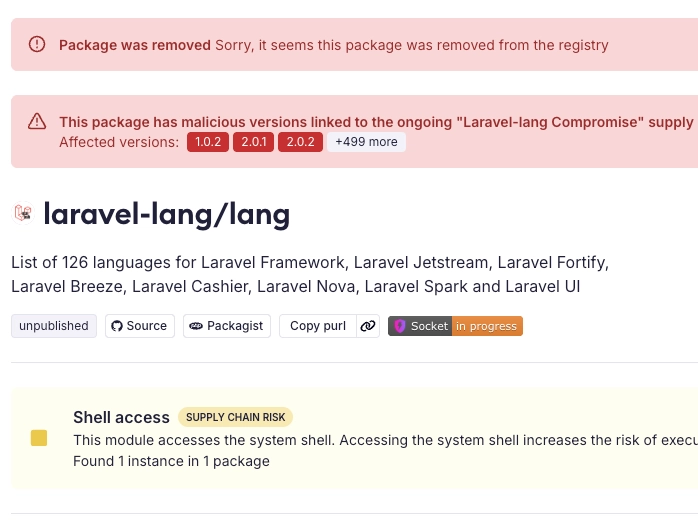
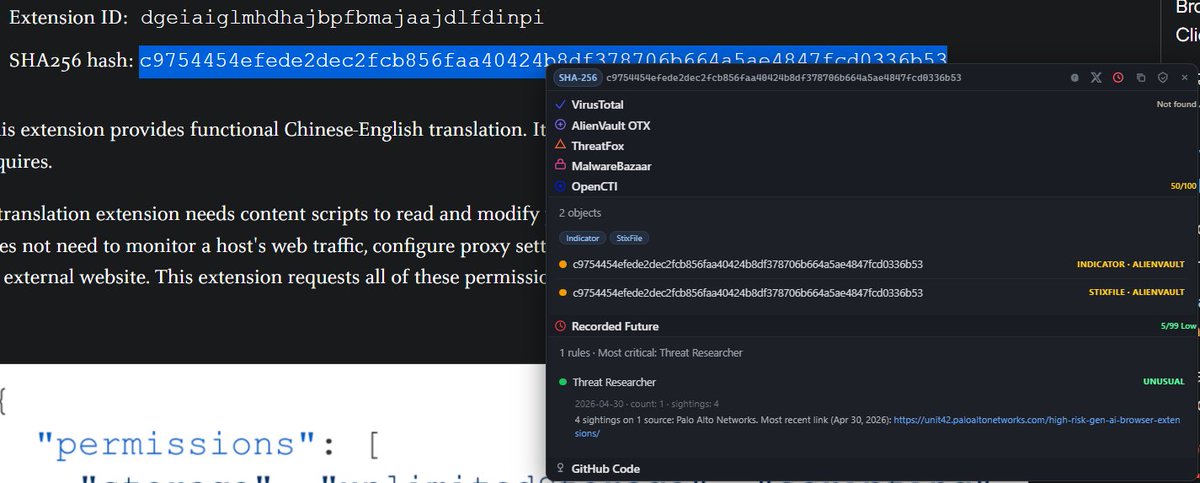
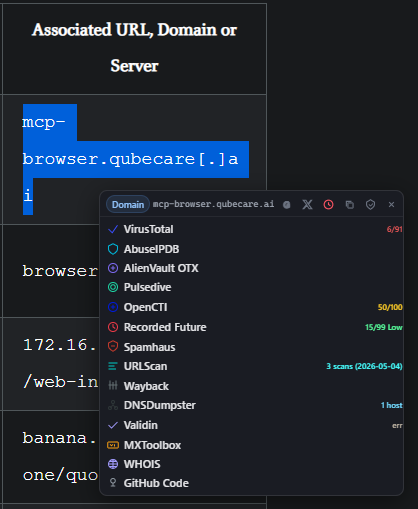
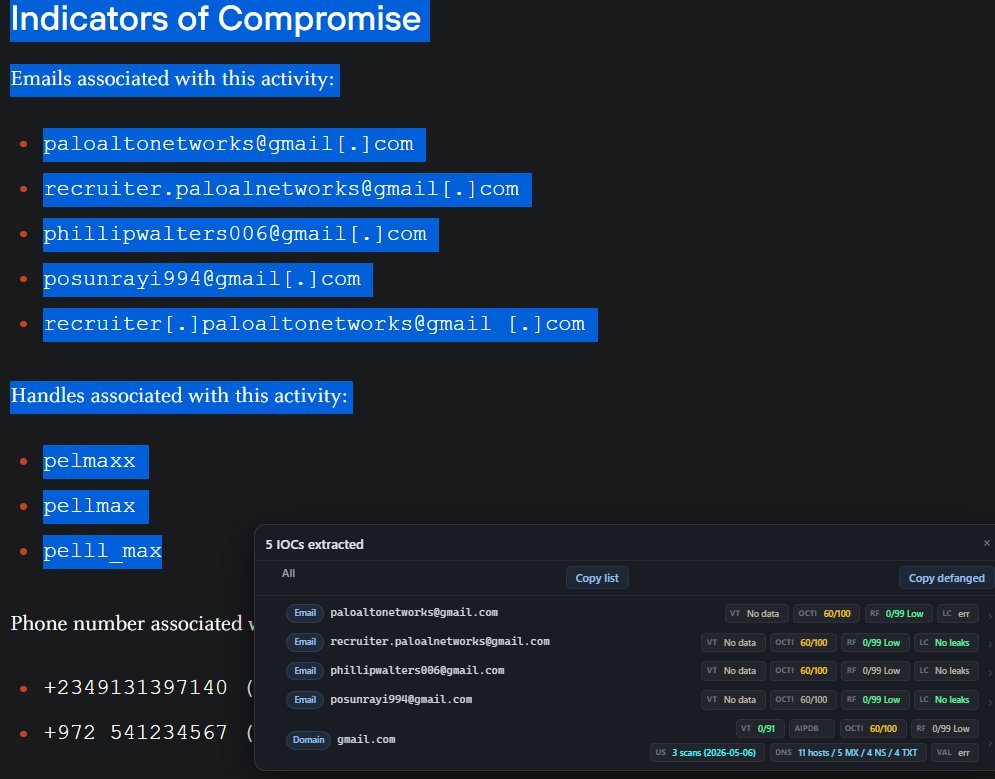
1/ We are sharing additional details regarding our investigation into unauthorized access to GitHub's internal repositories. Yesterday we detected and contained a compromise of an employee device involving a poisoned VS Code extension. We removed the malicious extension version, isolated the endpoint, and began incident response immediately.












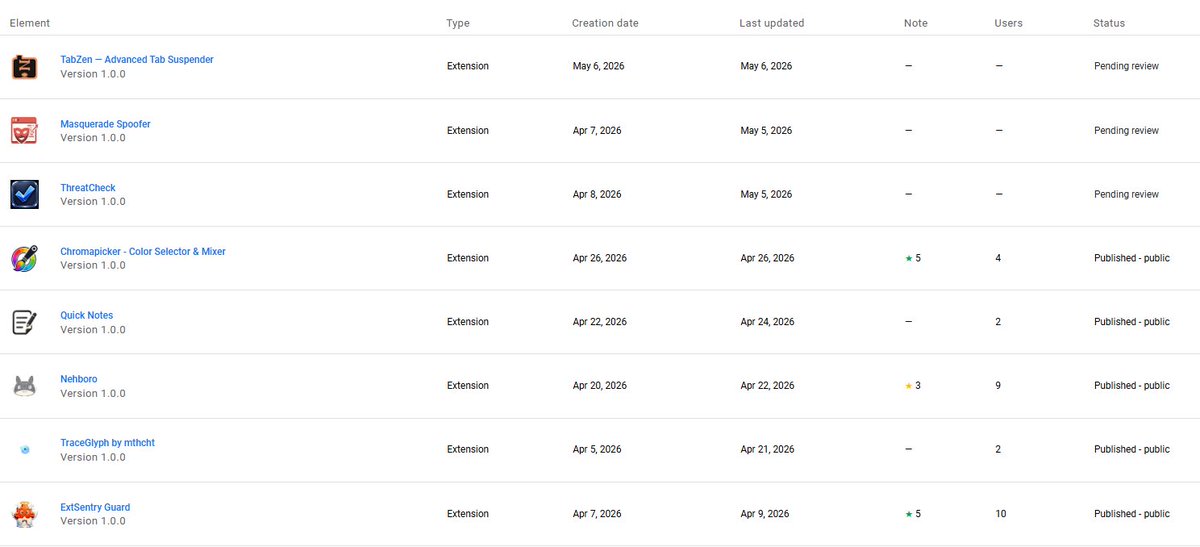

💠VSXSentry💠 vsxsentry.github.io VS Code Extensions threat intel feeds for multiple platforms, VSIX analyzer, scripts & policy generator, remediation and forensic traces guide

Just open-sourced CodeNeedle: a stealthy VS Code plugin that spins up a hidden endpoint for arbitrary JS evaluation with full Node privileges. VS Code is trusted everywhere, and runs everywhere. A needle straight to the heart of trusted environments💉 github.com/chvancooten/co…



