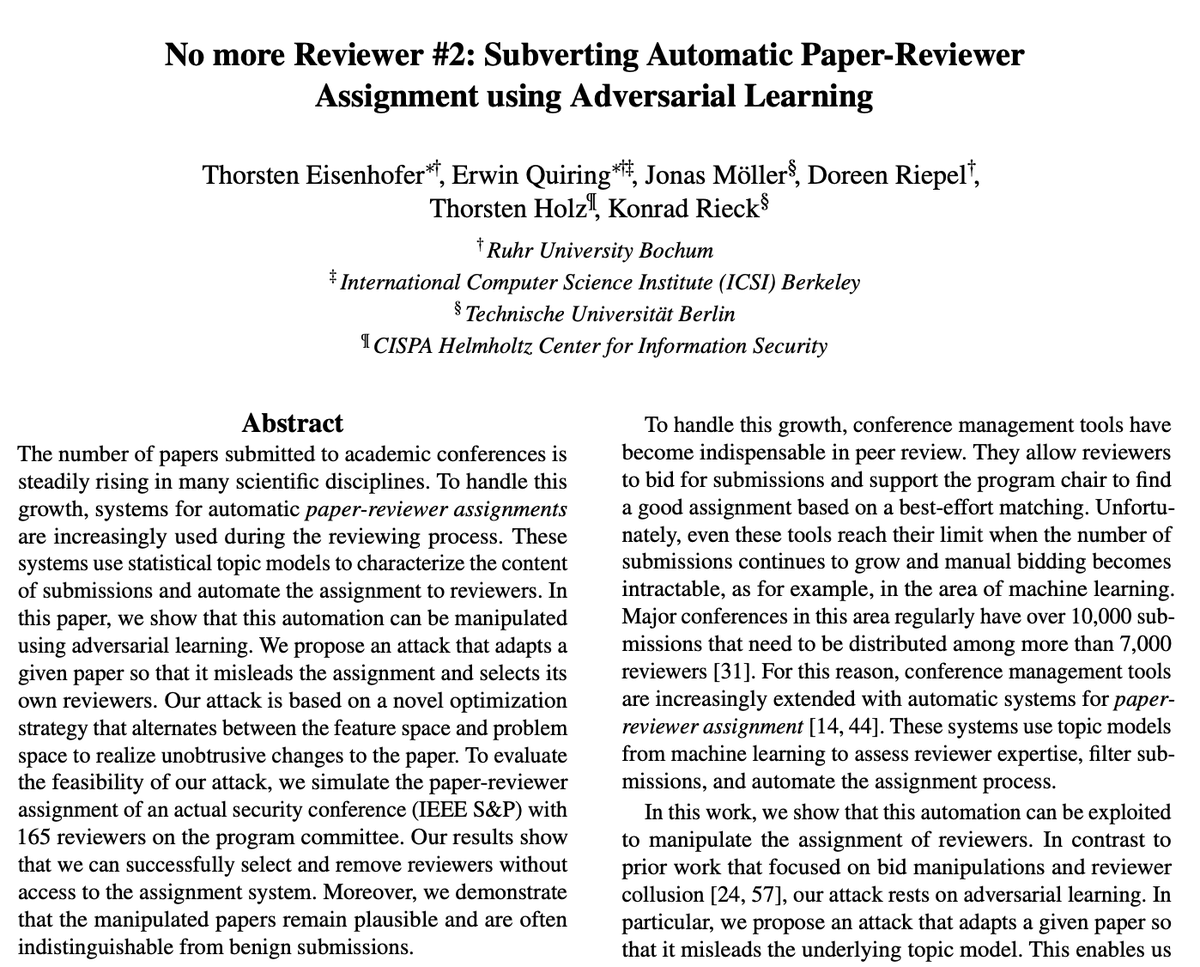
Thorsten Eisenhofer retweetledi

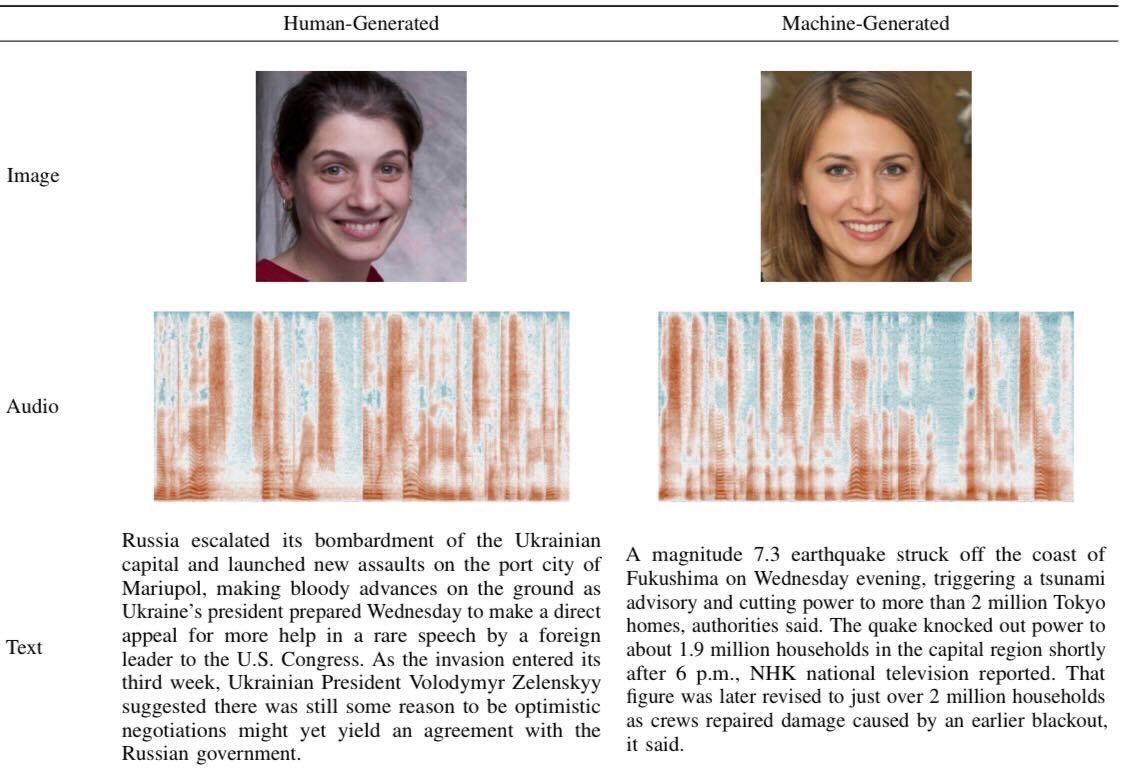
A Representative Study on Human Detection of Artificially Generated Media Across Countries (n=3,002) covering audio, image, and text 🥳
Our #SP24 @IEEESSP paper is now available arxiv.org/pdf/2312.05976…
Together with @joool_f @FranziskaPiaH @thorstenholz @jonasricker @_thrsten
English