Actlysis
1.7K posts

Actlysis
@actlysis
Aspiring smart contract auditor & developer | Obsessed with Linux 🐧 | 💻 https://t.co/iL9cWNI7LG | Check out https://t.co/5BQdkurOh6
404 Katılım Ağustos 2025
798 Takip Edilen289 Takipçiler

How do I make a video with this filter/color?
Ken Carson Song Of The Day@KCSOTD
Ken Carson - Diamonds (V1+ Released) [2024]
English

Let’s be honest, all of us thought HTML was a programming language🙄
#html
English

@Obrigado100 @trending_news72 Him sabi na
Na engagement him dey find
Leave am
Filipino

@trending_news72 This can't be real joor. No be like this vitiligo de do. It does not draw a straight-line though the midsection jare. Make una no whyne me
English

“My mother is Japanese, from Osaka. My father is Nigerian. Their love was judged long before I was born.
Then I came into the world, a mixed little girl who later developed a rare skin condition that changed not only my skin, but my eyes too.
I grew up under stares, whispers, and questions
My mother cried with me, protected me, and one day showed me Kintsugi — broken pottery repaired with gold. She touched the lines on my skin and said, ‘Kintsugi skin. Let this become your beauty, Eva.’
Years later, dance became the place where I stopped feeling broken. People no longer looked at me with pity, but with admiration. It taught me that my body was never something to hide from the world.
So when you look at me now, you are not just seeing a face or beautiful photos. You are seeing a little girl who survived every stare and slowly learned to love herself anyway.”
— Eva Dellone

English

🗓️ Day 86 – Solving Damn Vulnerable DeFi Challenges 🛠️
🔹 Current Challenge: Puppet v3 🕵️♂️
📚 Key Learnings:
✅ Learned how ticks simplify liquidity provision by specifying tickLower and tickUpper ranges
✅ Learned how ticks can be converted to prices and vice versa using the standard formula
✅ Learned how TWAP values are fetched using the consult function from a pool contract
✅ Learned that when creating a pool via NonfungiblePositionManager, it expects the initial price in √price × 2^96 (Q64.96 fixed-point format)
✅ Understood the developer intent behind the challenge
💡 Notes:
- Still figuring out whether TWAP can be manipulated when a protocol does not use it correctly
- Most of these concepts are still at a high level for me; I have not yet gone deep into how they work internally

English

@actlysis Actlysis spot on with Puppet v2 never trust onchain dex prices as oracles
English

🗓️ Day 85 – Solving Damn Vulnerable DeFi Challenges 🛠️
🔹 Current Challenge: Puppet v2 ☑️
📚 Key Learnings:
✅ Learned how Uniswap V2 Router simplifies swaps by routing everything through factory and pair contracts
✅ Understood that Uniswap V2 can handle any ERC20 ↔ ERC20 token swaps through liquidity pairs
✅ Understood basic router flow and how trades are executed indirectly through liquidity pools
✅ Saw that Puppet v2 uses the same pricing weakness as Puppet v1, but now through Uniswap V2 liquidity
💡 Security Mindset:
Don’t trust onchain DEX prices as a source of truth , they can be easily manipulated 🚨
💡 Reflection:
Even decentralized prices can be unreliable when liquidity is low. Protocols must not assume AMM prices are always “fair” or accurate.

English

🗓️ Day 84 – Solving Damn Vulnerable DeFi Challenges 🛠️
🔹 Current Challenge: Puppet v1 ☑️
yo i can’t even hold the urge for 3 days to grind 😭 been slacking on school work too so I’m swapping peak hours for school sessions and non-peak hours for coding
📚 Key Learnings:
✅ Understood the risk of using Uniswap v1 as a price oracle
✅ Learned how token swaps can manipulate AMM reserves and distort pricing
✅ Saw how lending logic can be broken when it depends on spot price from external liquidity pools
💡 Security Mindset:
Never trust AMM spot price as a source of truth , liquidity can be manipulated to game collateral calculations 🚨
💡 Reflection:
Small changes in liquidity can completely break financial assumptions in DeFi systems

English

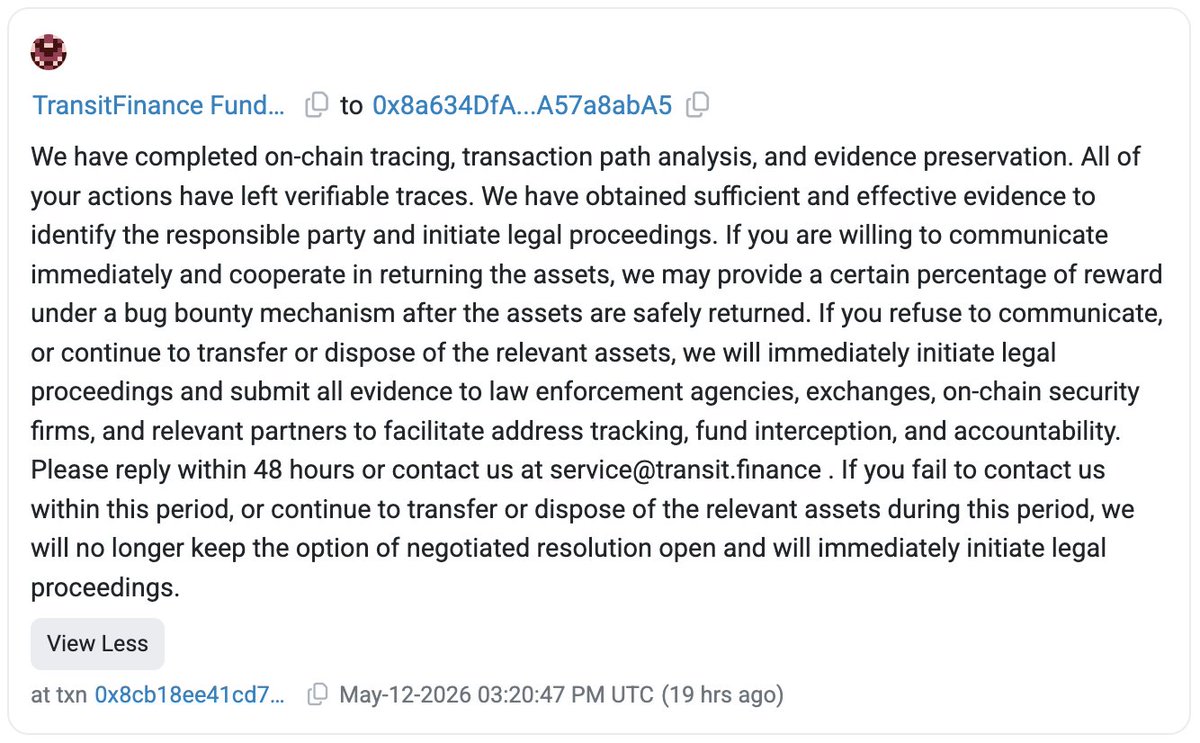
They send a 0 ETH transaction *to* the attacker's EOA, putting the full message text directly in the transaction's calldata (data field).
Since the recipient is an EOA (no contract code), nothing executes—no function is called. The message is simply recorded on-chain and visible to anyone viewing the tx on Etherscan.
That's how "onchain messages" to EOAs work.
English

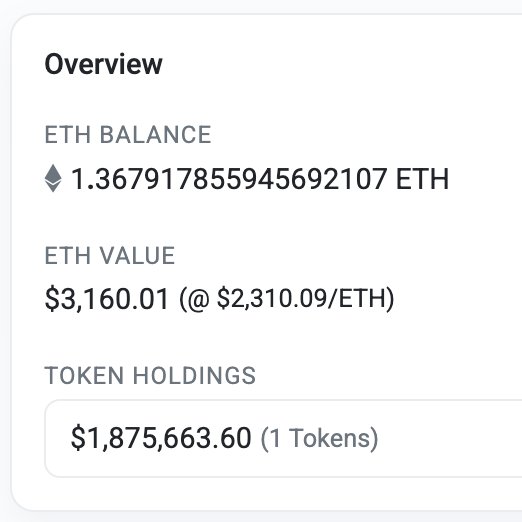
🚨 @TransitFinance appears to be hacked for $1.8M
Transit team has sent an onchain message to the attacker address who currently holds 1.875 million DAI on Ethereum: etherscan.io/address/0x8a63…
The funds are originated from Tron network: tronscan.org/#/address/TF9x…
English

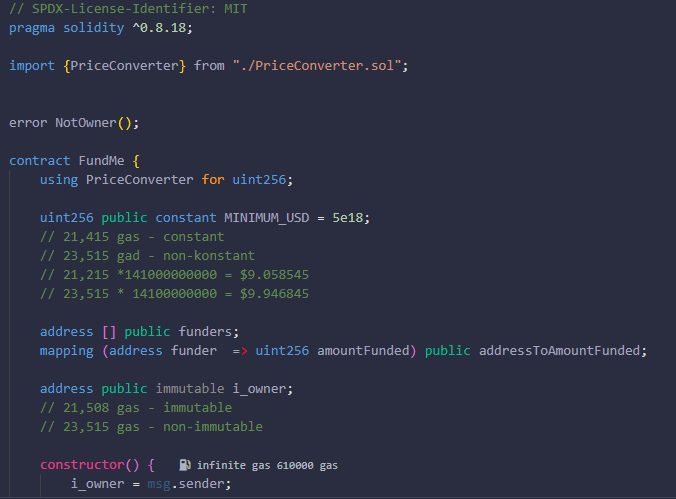
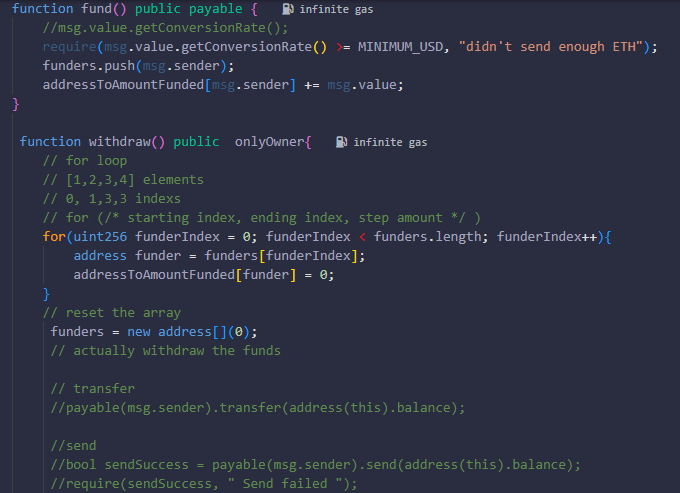
Finished the Smart Contract Development with Solidity course on Cyfrin Updraft!Built the full FundMe contract from scratch with Chainlink, onlyOwner and secure withdrawals.Solidity beginner level complete! Who else finished it? #Solidity #SmartContracts #cyfrin #updraft
English

⚡ Day 38 of Ethernaut with @OpenZeppelin
Completed all the challenges up to n.39 “Forger”.
Skipped the last one, “Not Optimistic Portal”, because it was too complex for me right now.
Github 👇
github.com/rosarioborgesi…
English

🗓️ Day 83 – Solving Damn Vulnerable DeFi Challenges 🛠️
🔹 Current Challenge: Puppet v1 🕵️♂️
I'm going to pause my grinding for a while since exams are approaching. Maybe after I round everything up, I’ll continue the grind again.
Today was all about AMMs and DeFi.
📚 Key Learnings:
✅ Learnt about liquidity and how liquidity providers earn their share for contributing funds
✅ Understood the math behind x * y = k, why both sides must maintain equal value, and the problems AMMs solve
✅ Found out that Vyper is quite similar to Solidity, just more minimalistic
✅ Understood how TWAP is used in Uniswap V2 to reduce price manipulation risks
💡 Security Mindset:
Price is not truth in DeFi, liquidity depth and oracle design determine how reliable that truth really is 🚨
💡 Reflection:
Math quietly controls almost everything in DeFi, from pricing to incentives to security itself. The deeper I learn, the more it feels like the future will belong to people who truly understand systems and numbers
English

@actlysis @CyfrinUpdraft @OpenZeppelin Spider256 its me buddy am not reading am the one who is writing those level solutions. But thank you for the best wishes buddy
Appreciated it 😁
English

Grinding through Ethernaut levels while learning fuzz testing and smart contract security.
Every challenge makes the roadmap clearer.
@CyfrinUpdraft @OpenZeppelin
English


