Sabitlenmiş Tweet
KAMI
9.8K posts

KAMI
@ade_kami
MERN Stack developer || SAIL Alumni
React Katılım Mart 2017
2.6K Takip Edilen321 Takipçiler
KAMI retweetledi
KAMI retweetledi
KAMI retweetledi

LetsDefend contributed to the success of CyBlack SOC Academy. Once again, thank you and happy birthday @LetsDefendIO 🥂
LetsDefend@LetsDefendIO
No meme today, it's my birthday! 🎂 We started 5 years ago. 5, FIVE. Your support has been our motivation, thank you all! 💙 🦔
English
KAMI retweetledi
KAMI retweetledi

In tech, the most underrated skill isn’t coding faster or knowing every tool……it’s being able to explain complex topics simply.
You can be brilliant with tools and tech stacks, but if you can’t communicate your ideas clearly to teammates, managers, or even in interviews, you’ll struggle to stand out.
At the end of the day, tech is about solving problems and making sure others understand the solution.
🛸@mvcciido_szn
unpopular opinion?
English

Day 5/31 When Access becomes a Weapon (Tesla, 2018)
In mid-2018, Tesla uncovered an alarming internal breach. Sensitive manufacturing data had been leaked, and unauthorized changes were found in the company’s Manufacturing Operating System.
At first, investigators suspected an external attack. But the culprit turned out to be one of their own, a production technician.
Using legitimate access, he allegedly exported gigabytes of confidential data to unknown third parties and made code changes that could have disrupted operations.
Tesla claimed he acted out of frustration over workplace issues, while he insisted he was a whistleblower exposing safety and quality problems.
This was not a phishing or malware attack. It is an example of how a trusted insider, with the right credentials and motivation, can become a company’s most dangerous vulnerability.
Community Challenge
What measures can an organization put in place to prevent insider threat without creating a culture of fear?
English
KAMI retweetledi

YOU MAY STILL BE YOUR PARENT'S CHILD
Dear Eric,
PHENOTYPE or GENOTYPE
Your "genotype" test might be lying to you!
READ ME!!!!
Many labs in Nigeria aren’t actually giving you your genotype...they’re giving you your phenotype. And yes, there’s a difference!
1) Phenotype is like vibes, genotype is the DNA behind it.
Labs report HbAA, AS, SS, etc., based on what your blood is showing, not the exact genes you inherited. It’s like saying someone is rich because they drive a Benz...without checking their bank account.
● Phenotype: The observable expression of the hemoglobin types present in the blood, typically reported as AA, AS, SS, AC, SC, etc.
● Genotype: The actual genetic makeup of the individual, which requires DNA-based testing to determine specific alleles at the HBB gene locus.
2) Your "AA" might not be so innocent.
Some rare hemoglobin variants (HbD, HbE, HbO, thalassemias) can masquerade as AA or AS. Imagine thinking you married an AA, only to find out 9 months later you were lied to. SURPRISE! 🎁
3) Why does this matter?
You could accidentally have a child with sickle cell disease because the lab "forgot" to check for rare variants. A ₦5k test today could cost you millions in medical bills later. 😬
4) How do you avoid this mess?
● Get HPLC (High-Performance Liquid Chromatography) instead of basic electrophoresis.
● If your result is confusing, get DNA testing...because genes don’t lie, but lab results sometimes do.
Moral of the story: If you're testing for genotype, ask “Is this phenotype or genotype?” before life humbles you!... and when you have done the right test and it's still confusing you need to ask the source deeper questions.
ERIC 💜🦅@LagosPresidentt
My Dad is AA and my Mum is also AA but I’m AS. Can someone make this make sense to me, please.
English
KAMI retweetledi

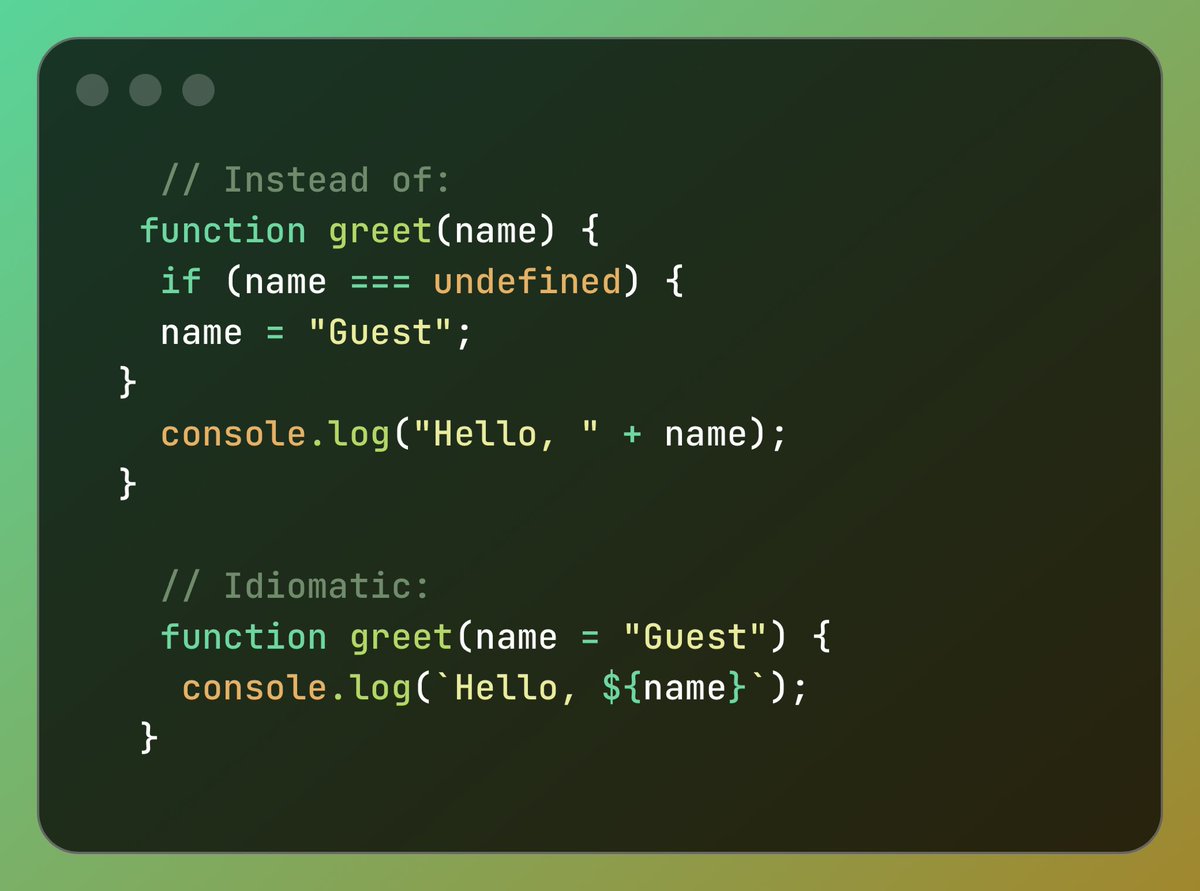
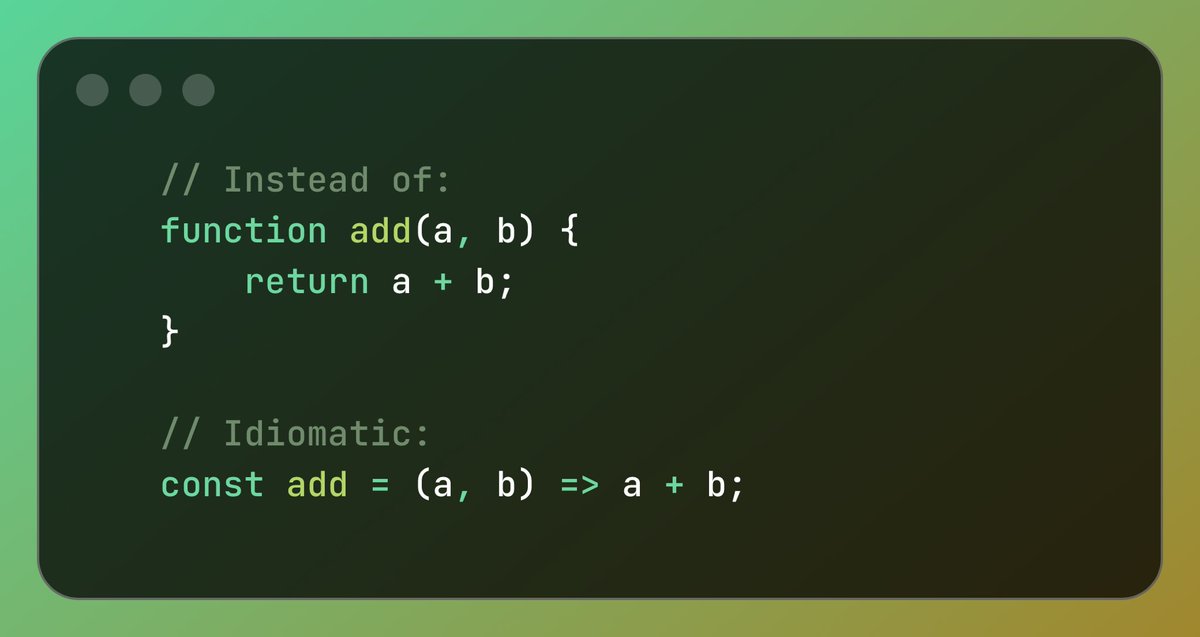
Honestly, since @Dominus_Kelvin mentioned about idiomatic JavaScript, I couldn’t stop thinking about it.
English

@hackSultan @ayobaapp @AltSchoolAfrica From me, a year 2 months from the future. You're now studying Cybersecurity @AltSchoolAfrica, can't wait to see how everything works out for you. Stay jiggy 👍
English
If you want a global Diploma in software engineering @ayobaapp has partnered with @AltSchoolAfrica to give a 100% scholarship to tons of student who pass the entrance exams.
You can learn:
Cyber Security
Frontend eng.
Backend eng.
Cloud end.
RT this + reply and I’ll DM you.
Ccc@91882i7
@hackSultan You be mumu. No be everything you go dey chook mouth. When the other side throws their own bants, I hope you are bold enough to also caution them. No go hustle students for your tech school, dey mumu yoitself 🤡
English

Day 4/31 Every Breach is a Lesson (Co-op, 2025)
In April 2025, one of Britain’s oldest and most trusted retail cooperatives, the Co-op, found itself in the crosshairs of a cyberattack that shook its foundations.
Investigations suggest the attackers may have used social engineering to trick Co-op IT/helpdesk staff into resetting passwords or granting access.
Store shelves were unstocked, deliveries were delayed/ cancelled, and staff were left unable to perform basic operational tasks.
To contain the threat, Co-op deliberately powered down parts of its IT systems, effectively choosing disruption over deeper compromise.
Then came the news no member wanted to hear: the personal details of 6.5 million Co-op members, including names and contact information, had been stolen.
Community Challenge
The attackers used social engineering to gain access. What’s the most effective control an organization can implement to reduce this type of risk?
English
KAMI retweetledi

Day 3/31 — When a City Went Dark (St. Paul (Minnesota, 2025)
It started like a whisper on the network, a flicker in logs that became a blackout. In late July 2025, St. Paul’s digital heartbeat stuttered.
The city systems went offline, public Wi-Fi and library services failed, bill-pay portals stopped working, and employees found themselves locked out of the tools they use every day.
The city shut down chunks of its IT estate to contain the threat.
The ransomware group “Interlock” claimed credit for the attack. The attackers were described as a “sophisticated external actor.”
The attackers published 43GB of data online after the city refused to pay ransom. This intensified the pressure on recovery teams scrambling to rebuild.
St. Paul chose to contain, rebuild and restore rather than reward the attackers.
Community Challenge
St. Paul chose not to pay the ransom. Was this the right call? Why or why not?
English
KAMI retweetledi

Day 2/31 When Airports Stood Still: A Cyber Wake-Up Call. (London Heathrow, Brussels, Berlin, Dublin 2025)
Last month, passengers at four European airports were stranded in long queues. Flights were delayed/cancelled and bags were unclaimed.
At first, it was dismissed as “technical issues.” In reality, it was a ransomware attack on Collins Aerospace’s MUSE system, the software that powers check-in, boarding, and baggage handling.
With systems down, the airports were forced to use manual approach. The incident exposed a hard truth, aviation doesn’t just run on engines and runways. It relies on secure systems; and when the system is vulnerable, the industry stalls.
The planes are flying again. But the warning is clear.
Community Challenge
Which element of the CIA triad was hit the hardest? Give reasons
English
KAMI retweetledi

Day 1/31 “When Innocence Was Exploited”
Kido International - 2025
A cyber-attack hit an institution built on care, where trust is everything.
Few days ago, a criminal group calling itself Radiant claimed to have breached Kido International (A nursery chain with 18 UK sites and additional sites overseas). The group reportedly stole personal information of about 8000 children.
The attackers published profiles of 20 children on a darknet leak site, and private data of employees. They contacted some parents and carers, threatening to post more information, unless Kido pays a ransom.
The stolen data includes children’s names, photographs, DOBs, home addresses etc. Multiple reports indicate the breach involved third-party systems.
Community Challenge
The attackers claimed they "deserve to be compensated for their pentest”
Was this truly a penetration test? Explain why or why not.
English
KAMI retweetledi

In Mariah Carey’s voice, “Its timeeeeeeeeeeeeee!”💃🏻
To read more and apply for this @cybersafehq training, visit cybersafefoundation.org/our-programs/a…
Please note that this is a high accountability hands-on training that requires a minimum of 83% attendance and consistent task completion throughout the program.
I’m looking forward to welcoming cohort 2.0!

English

@ireteeh The organization should employ IAM and access controls, as this ensures only authorized people/systems can access resources. The org should also gamify user awareness to make it easier to teach employees about the different types of attack, how they work, and how to prevent it.
English




