adibou retweetledi
adibou
173 posts

adibou retweetledi

We've published a new blog post by RyotaK @ryotkak !
He exploited a directory deletion race condition in Google Cloud's Looker, leading to full RCE and K8s privilege escalation.
Read the technical details here:
flatt.tech/research/posts…
English
adibou retweetledi
adibou retweetledi

I finally let Claude do my pentest this week. Full 5-day engagement, zero human input. Here's what the client got: 😏
clawd.it/posts/10-repla…
#bugbounty #pentesting #AI #cybersecurity #infosec #claudeai
English
adibou retweetledi
adibou retweetledi

New research just dropped by @alien2exe on hijacking OAuth popups via predictable window. open() targets.
The chain uses iframe name collision forcing the auth flow into a controlled context, eventually linking an attacker-controlled addon to leak workspace PII and config data
lab.ctbb.show/research/can-a…
English
adibou retweetledi
adibou retweetledi

@FearsOff @Cloudflare This write‑up tells the story of how traffic aimed at that certificate path could reach origins behind Cloudflare even when the rest of the application was blocked by customer rules.
Enjoy the reading here fearsoff.org/research/cloud…
English
adibou retweetledi

We hacked the AWS JavaScript SDK, a core library powering the entire @AWScloud ecosystem - including the AWS Console itself 🤯
How did we do it? Just two missing characters was all it took.
This is the story of #CodeBreach 🧵👇

English
adibou retweetledi

I wrote an article about 8 vulnerabilities in Claude Code that allowed me to bypass the permission model and execute arbitrary commands!
GMO Flatt Security Inc.@flatt_sec_en
We've published a new blog post by RyotaK @ryotkak He discovered 8 methods to bypass safety mechanisms in Claude Code, leading to arbitrary command execution. We recommend updating to v1.0.93 or later to fix this vulnerability (CVE-2025-66032). flatt.tech/research/posts…
English
adibou retweetledi
adibou retweetledi

Quite a long work to get the exploit working and the article ready, but here it is !
Our pre-auth RCE in Livewire v3 (CVE-2025-54068) with @_remsio_ is live ! Enjoy the read :)
Synacktiv@Synacktiv
🚨 RCE in #Livewire (CVE-2025-54068)! Our specialists uncovered a critical flaw allowing remote code execution without the APP_KEY, exploiting Livewire’s hydration mechanism + PHP’s loose typing. 🔗 Patch now! (v3.6.4+) synacktiv.com/en/publication…
English
adibou retweetledi
@livewithnoregrt Achieving your dreams is a race against time. Time forces convergence, and premature convergence kills dreams.
This is hard to understand when you’re young, before you know the wrath of time or the meaning of convergence.
It's typically understood in hindsight, and with regret.
English
adibou retweetledi

Today, we’re releasing watchTowr Labs’ @chudyPB’s BlackHat .NET research, owning Barracuda, Ivanti and more solutions.
Enjoy the read as Piotr explains a new .NET Framework primitive, used to achieve pre- and post-auth RCE on numerous enterprise appliances.
labs.watchtowr.com/soapwn-pwning-…
English
adibou retweetledi

We believe this is the first documented case of a large-scale AI cyberattack executed without substantial human intervention. It has significant implications for cybersecurity in the age of AI agents.
Read more: anthropic.com/news/disruptin…
English
adibou retweetledi

Whoever that promises you their tool, their course or whatever will make you make big bucks is lying.
Learn, work hard on your skills, understand the things. There is no other magic in the field.
Don't listen those that are saying otherwise
#bugbounty
English
adibou retweetledi

I've been researching the Microsoft cloud for almost 7 years now. A few months ago that research resulted in the most impactful vulnerability I will probably ever find: a token validation flaw allowing me to get Global Admin in any Entra ID tenant. Blog: dirkjanm.io/obtaining-glob…
English
adibou retweetledi

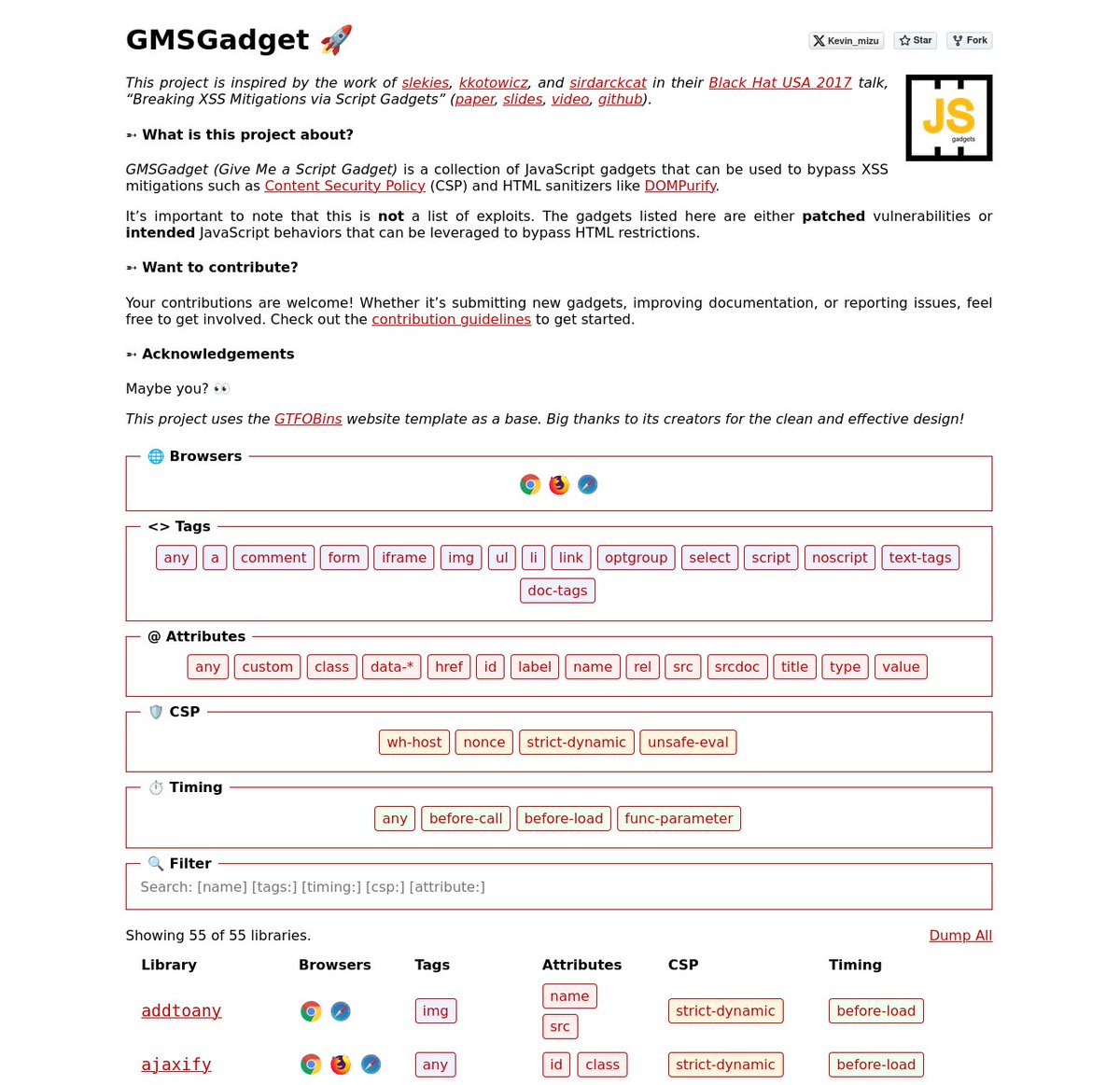
I'm happy to release a script gadgets wiki inspired by the work of @slekies, @kkotowicz, and @sirdarckcat in their Black Hat USA 2017 talk! 🔥
The goal is to provide quick access to gadgets that help bypass HTML sanitizers and CSPs 👇
gmsgadget.com
1/4
English
adibou retweetledi

New blog post is up: How I leaked the IP addresses of Brave's Tor window and Chrome VPN extension users--plus, a new Popunder technique and connect-src CSP directive bypass. Read more @ 0x999.net/blog/leaking-i…
English

Today was my last day as a pentester at Bsecure, and it feels a bit surreal. After a three-year journey of hunting on the side, I’m finally ready to go all-in as a full-time bug bounty hunter.
To celebrate this milestone, I've written an article sharing the full story. It’s a transparent look at the path that got me here: the wins, the lessons, the real financial numbers, and my honest advice for anyone considering this adventure.
You can read all about my journey from pentester to full-time hunter here: gelu.chat/posts/from-pen…

English