Ai000 Cybernetics QLab
28 posts


Ai000 Cybernetics QLab
@aioooir
Ai000 Cybernetic QLab is a little company with a focus on low-level system security, secure communication, and defend against bad minds.
Tehran Katılım Kasım 2023
182 Takip Edilen20 Takipçiler

We take a closer look at some foundational Git concepts, focusing on the processes of #initialization, #cloning, and the powerful features of #GitKraken. youtube.com/watch?v=8Amrdg…

YouTube
English

📌طراحی یک سامانه Windowing برای لینوکس از صفر. در این پست دربارع چالشهای طراحی رابطهای گرافیکی در لینوکس صحبت شده است. در تلگرام @aioooir بخوانید.
فارسی

📌لینوکس بهتر است یا ویندوز، آخر سر حق با کیست؟ مقاله را در کانال تلگرامی @aioooir بخوانید.
فارسی

📌نظارت بر روی تراکنشهای بلاکچین و شناسایی فعالیتهای مجرمانه و غیرقانونی، نگاهی فنی به داستان @nobitexmarket. مقاله را در کانال تلگرام @aioooir بخوانید.
فارسی

In this research paper, the first part of the system analysis series, our team at ACQL has embarked on an exploratory journey to thoroughly understand general systems concepts, aiming to extrapolate these concepts to broader system typologies. read here acql.ir
English

One of the most interesting challenges for me is to write an exploit for a media player which is player continues its work after the exploit embedded into the file is triggered. Do you think this can be done? #exploit #fileformat
English

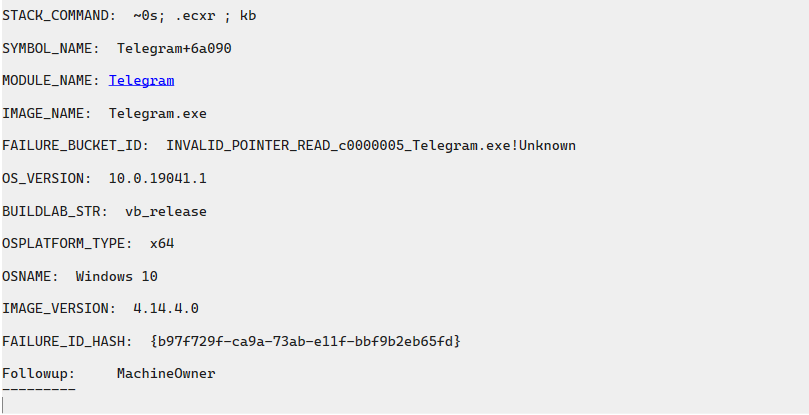
The second vulnerability in the same class (github.com/telegramdeskto…) was spotted by the Ai000 Cybernetic QLab team. However, @Telegram had some issues recently with rlottie class. However, this new vulnerability exists in v4.14.4.
English