📲 SMS Trap: How One Message Can Steal Your Crypto on P2P Platforms
When selling cryptocurrency for fiat on P2P platforms, scammers often use a scheme involving fake SMS or email payment notifications.
Here’s how it works — so you know what to watch out for.
🎬 How the scheme works
You decide to exchange your cryptocurrency for fiat (USD, EUR, GBP, etc.).
You have, for example, USDT on a popular exchange (Binance, Bybit, MEXC, Gate.io, Kraken, etc.).
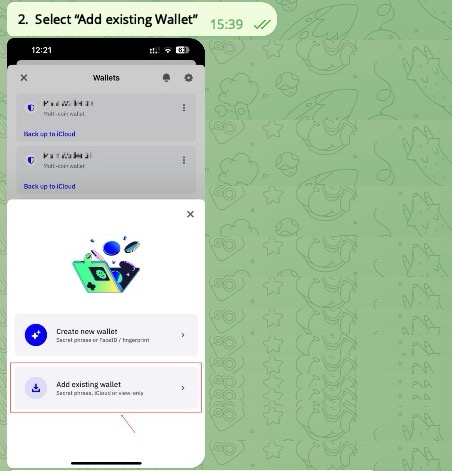
1️⃣ You go to the P2P section of the exchange.
2️⃣ You post an ad or select an existing offer.
3️⃣ As the payment method, you choose phone number transfer or instant payment app (🇺🇸 Zelle, Cash App, Venmo — USA; 🇪🇺 SEPA Instant, Revolut, bank-linked phone number — Europe).
👉 At this point, the counterparty receives your phone number or linked account details.
🎭 How the scammer operates
• They use an exchange account registered under a fake or stolen identity (such accounts are sold on darknet marketplaces 🥷 for $20 to $300).
• Instead of sending a real payment, they send you a fake SMS or email, pretending to be a notification from your bank or payment app.
They typically don’t spoof the official sender name — the message comes from a random number or email (spoofing sender names has become more difficult).
📩 Example of such text:
“Payment received: $1,200.00 USD via Zelle. Available balance: $4,350.00 USD.”
• After sending the message, the scammer starts pushing in chat:
“Payment sent, please confirm the transaction.”
• The victim, seeing the familiar template, rushes to complete the deal and confirms the transaction on the exchange — without checking the actual bank account or app.
🚨 What happens next
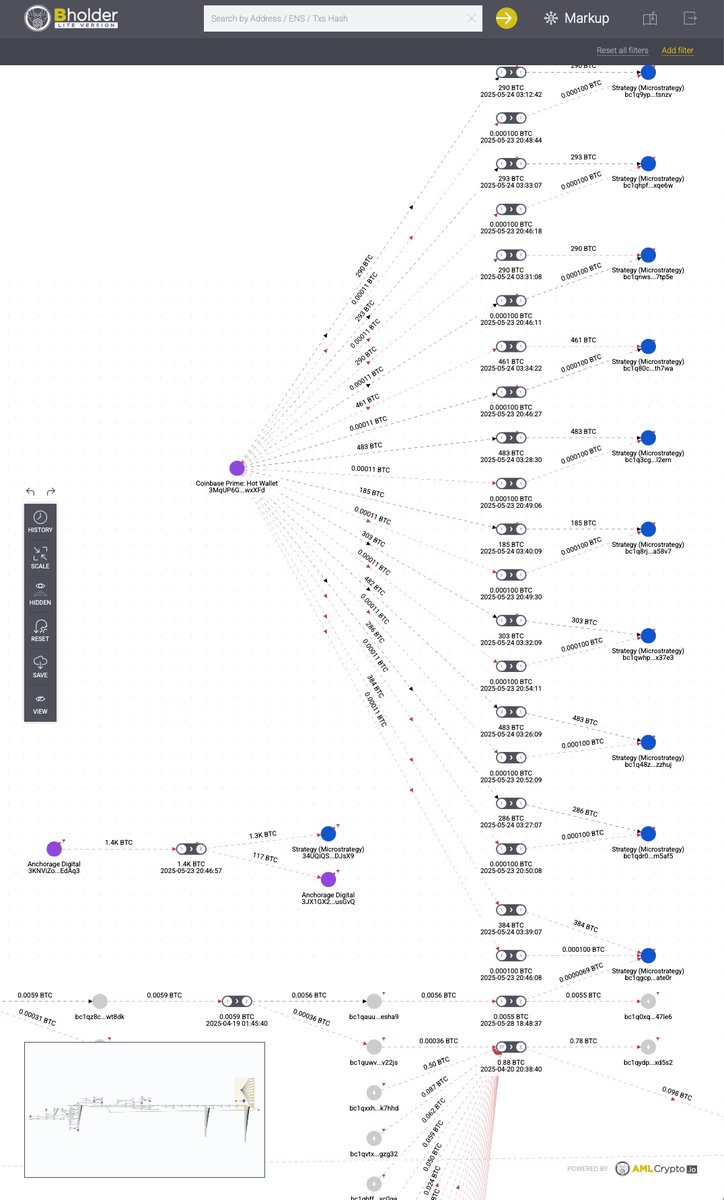
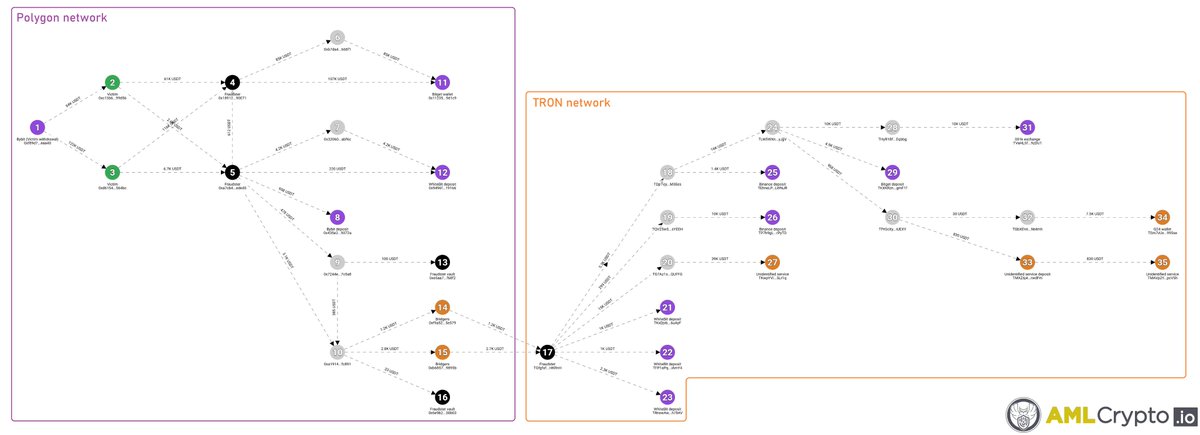
• The cryptocurrency is immediately transferred to the scammer’s wallet.
• Even if you quickly realize the scam and contact exchange support:
• You confirmed the transaction yourself — from the exchange’s point of view, everything was executed correctly.
• The scammer usually withdraws the funds instantly — making it nearly impossible to recover them.
🛡 How to protect yourself
✅ SMS or email ≠ payment confirmation. Always verify the actual receipt of funds in your banking app or online banking.
✅ Any pressure to “confirm quickly” is a clear red flag.
✅ Remember: if you confirm the transaction, the exchange is unlikely to refund your crypto — even if fraud is proven.
🛡 AMLcrypto.io | ✔ TG - Bot (t.me/AMLCryptobot | 💬 Contact us (t.me/AMLCrypto)

English