Zero fraud cases. +70% increase in onboarding conversion rates.
A leading LATAM bank was losing the battle against mule accounts.
The challenge is that the fraud is invisible at onboarding. The real person opens the account, passes every check.
By the time the fraud happens, onboarding is long over.
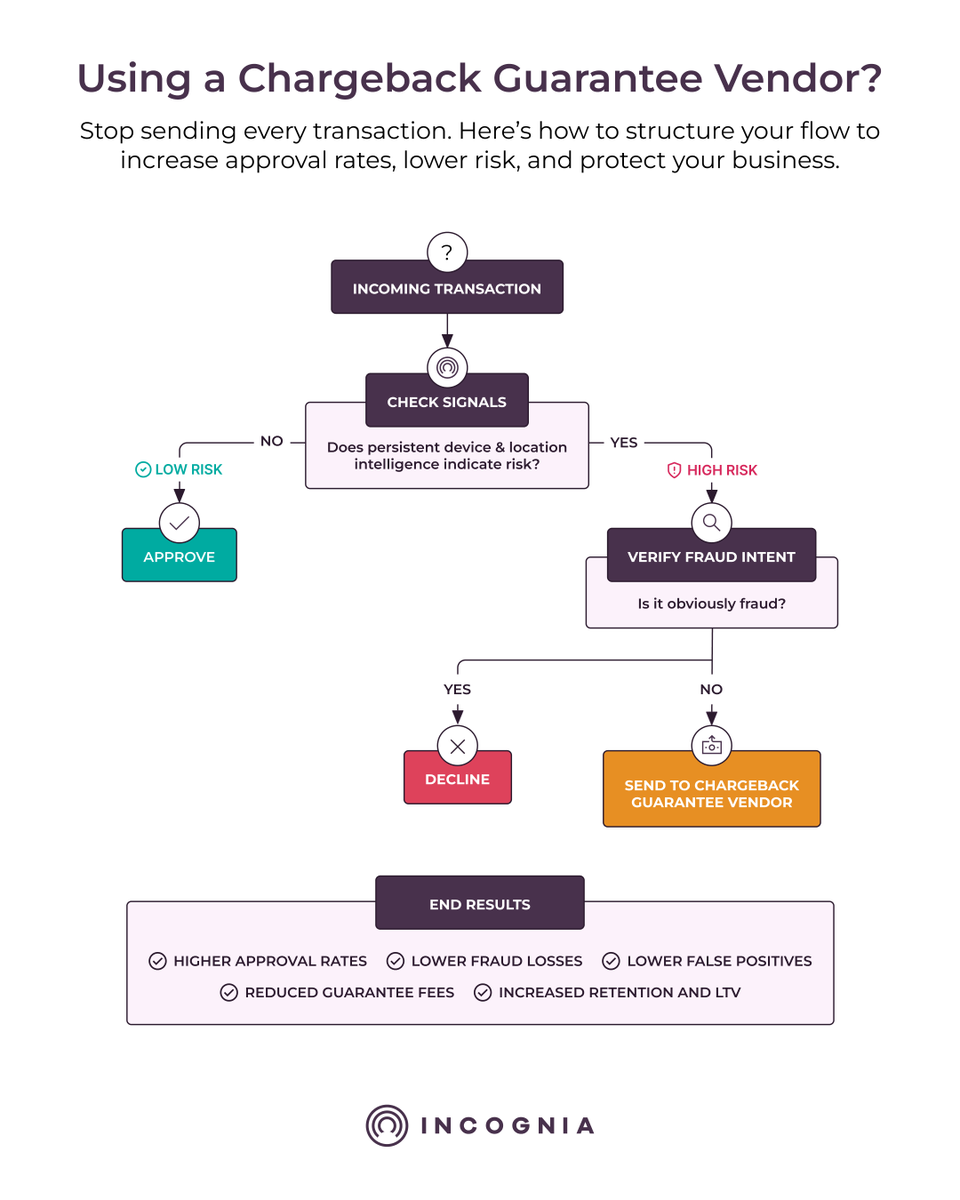
When we integrated with this bank, we started looking at where devices were actually being used—not just GPS or IP, which are too imprecise to be actionable.
Incognia's location technology locates a device within 10 feet. Enough to differentiate between floors and apartments in the same building.
That's when the pattern became obvious.
📍 One apartment. A high concentration of devices opening and accessing accounts from the exact same location. A fraud farm.
So, we blocked it.
But the same signal that caught the fraud farm also cleared the path for legitimate users.
By matching users' stated addresses to their real device location behavior, we gave the bank the confidence to approve more legitimate accounts faster.
The result after several months: every account we flagged as low risk had zero reported fraud cases.
Not a single one.
Full case study: hubs.li/Q047JRs10

English