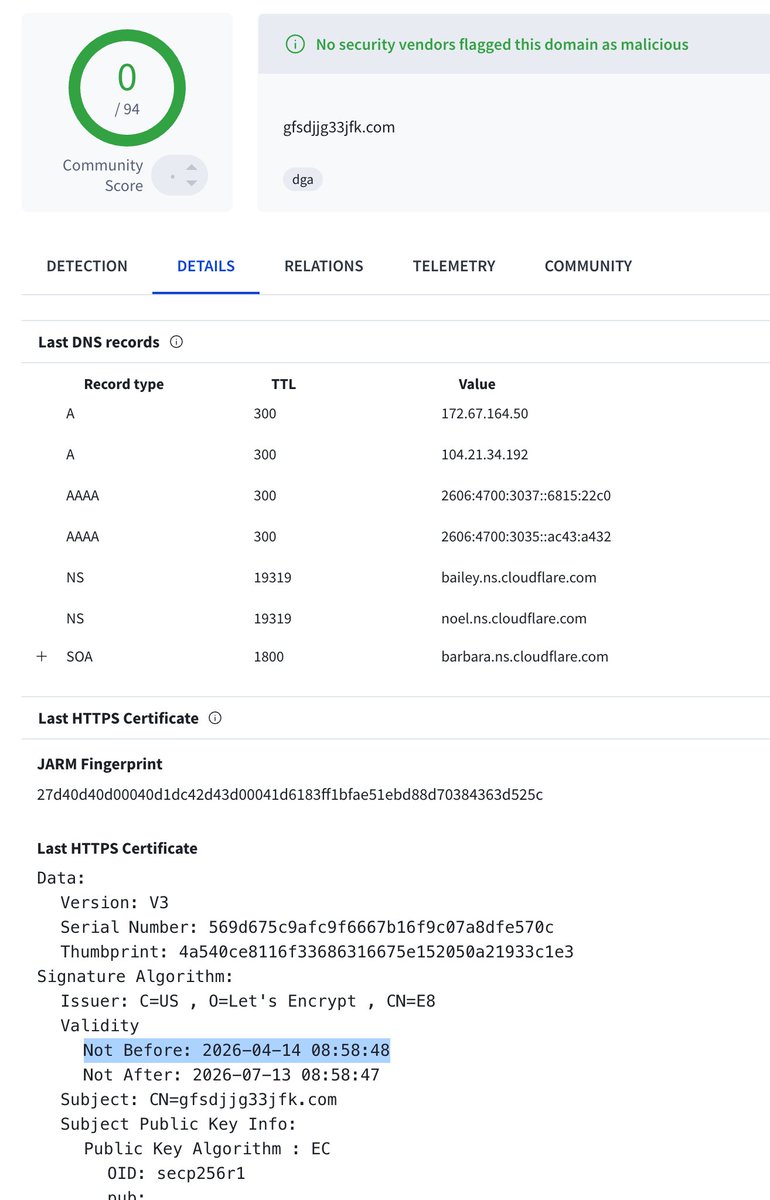
We have identified a novel social engineering campaign abusing Obsidian, the popular note taking app, to deliver a previously undocumented RAT #PHANTOMPULSE and it’s loader #PHANTOMPULL targeting individuals in finance and crypto. The attack never exploits a vulnerability. It abuses Obsidian's own plugin ecosystem to execute code the moment a victim opens a shared vault. Full analysis: go.es.io/4cld0dB