ARC
4.9K posts


ARC
@arc4g
Sundial co-founder · building @Protectmyface, a service that tells you when your face gets posted online without your knowledge.



crazy fact about discord is when you delete your account they still keep all the posts public even the photos and just switch the username to random letters. How is that legal? It's one of the only platforms that gets away with insane stuff like that

some influencer approached me & asked for my insta i said no sorry. i didnt know he was filming w meta glasses & now he has posted that reel & some weird looking creature has commented "always a 2/10 girl w attitude"😀 I texted the influencer to take it down hope he'll do it asap




Hi, some freak on Instagram stole my work, ran it through an AI, and uploaded it to their account. Disgusting. First is mine. Reports are more than appreciated.







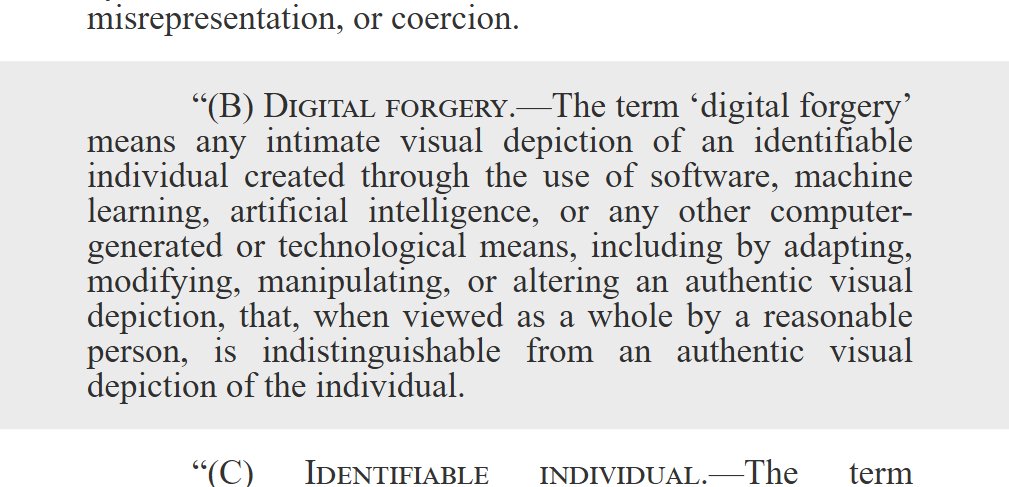
The federal notice-and-removal provisions of the Take It Down Act will go into effect in about 7 hours. Platforms used to be able to ignore removal requests for nsfw ai edits using your real photos. Starting May 19, non-compliance means FTC fines up to $53,088 per image.