Ashish Kar
303 posts


Ashish Kar
@ashishkar
Explorer, who is awed by nature and its inner working. Still unpacking how it all fits together so beautifully.
Sunnyvale, CA Katılım Mart 2010
388 Takip Edilen57 Takipçiler

Check out my latest article: Sacred Systems: Governing Agentic AI with Timeless Principles linkedin.com/pulse/sacred-s… via @LinkedIn
English

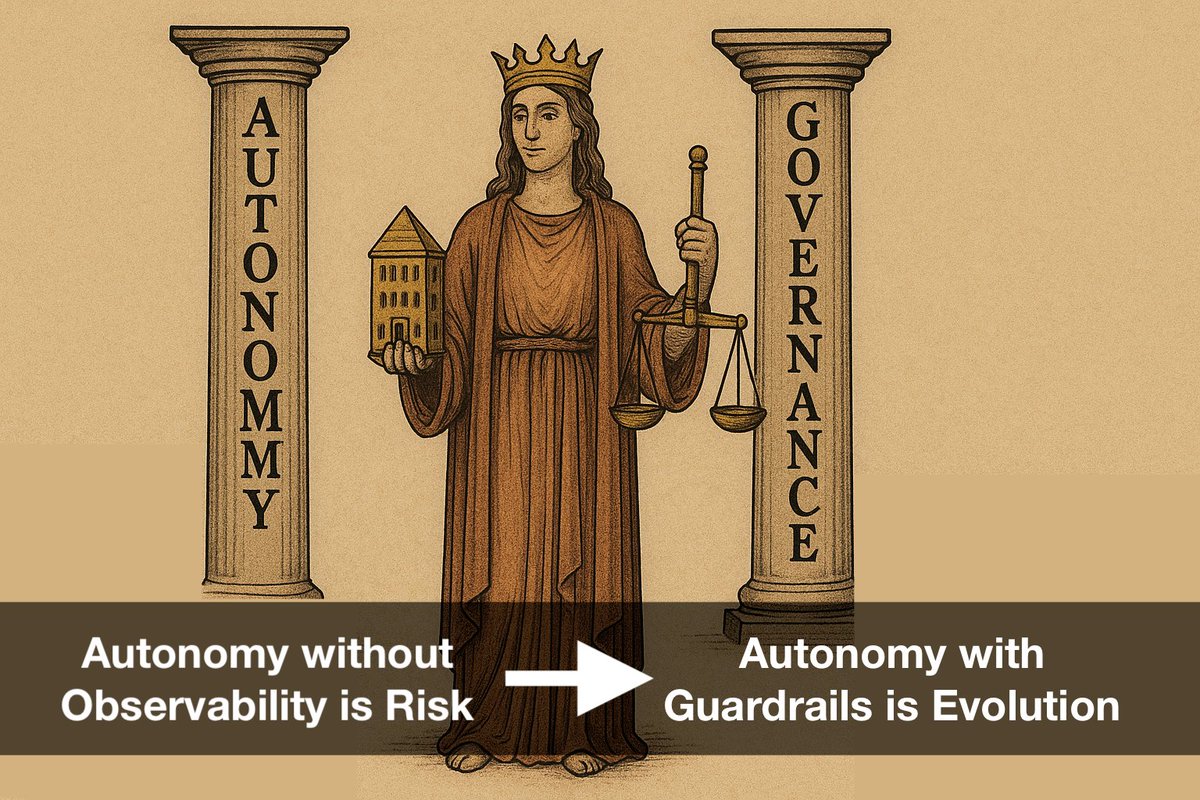
🚀 Agentic AI is here. Agents that plan, act & adapt.
Remember: Autonomy without observability = risk.
With it = evolution.
#AgenticAI #AIEngineering #AIGovernance #LLMs
linkedin.com/pulse/agentic-…
English

How a friend described how he felt after eating pepper X 🤣
Toaster X
youtu.be/xpyMi6zQRE0?si… via @YouTube

YouTube
English


Funny and probably is one of the correct depiction of how breach happens. When soc teams have no context. lnkd.in/ge4z5RuC
English

System Intrusions are complex attacks that leverage malware and/or hacking to achieve their objectives, including deploying Ransomware and Backdoors.
Araali Networks allows your team to detect and prevent intrusions in your complex cloud-native environme…lnkd.in/gc55f6Cw
English

Are you looking for SOC2 compliance for your cloud-native environment?
Having gone through SOC2 Type II twice, we understand the pain and have added features to Araali Networks to make your journey smoother.
#soc2 #vulnerability…lnkd.in/gMuSZBMX lnkd.in/gbCANhfM
English

SOC2 Type II is not trivial. Leading the effort is challenging, and it takes a village to make it happen. Thanks to our team and Abhishek Singh for supporting me in this journey.
Also, please let me know if you need any help with SOC2.
Going through the…lnkd.in/gB6_3HH6
English

Tang Hall's 50th anniversary
Unbelievable how time flies!
550 Memorial Drive, Cambridge
Srikanth Patala, Srujan Linga, Deep Ghosh, Sukant Mittal, Vikrant Vaze, Chetan Shinde, Ram Bala Chandran lnkd.in/gU8bzyNJ
English

Automate security outcomes for SOC2 with Araali Networks
Vulnerability management, auto-patching vulnerability, compensating controls for unpatchable vuln, cloud detection - IDS, Access Control for Apps, Network Security, and Asse…lnkd.in/gjbUEmCq lnkd.in/gRzdr7Bd
English

Automate security outcomes for SOC2 with Araali Networks
Vulnerability management, auto-patching vulnerability, compensating controls for unpatchable vuln, cloud detection - IDS, Access Control for Apps, Network Security, and Asset Inventory.
Deploys an…lnkd.in/gMMQxrBX
English

Is Your Vulnerability Management Effective?
Software is vulnerable, and this fact is routinely abused by attackers to pull off a data breach (the grand prize). Recently there has been a huge emphasis on vulnerability management, shift left, and continuou…lnkd.in/gHuYkXhT
English

We often forget this nuance - in cloud ingress is closed by default - we have to allow list what can come in.
But egress is all open by default - no checks and balances in place - making backdoor creation trivial.
Reminds me of airport, where the TSA s…lnkd.in/gPEEXJG5
English

Security success is ruining the attacker's ROI -
Security teams can’t achieve an absolute secure state, so deter attackers by disrupting and degrading their Return on Investment (ROI).
Increase the attacker’s cost and decrease the attacker’s return for…lnkd.in/gAFk6FmK
English

A very powerful image from the PANW research team. The top three exploited vulnerabilities - RCE, Traversal, and Info Disclosure represent 65.4% of all attacks in 2021. In the microservice world, all three require network access and open egress - which is…lnkd.in/gCcF55Rt
English

People often confuse mTLS with Zero Trust.
mTLS is a security protocol that authenticates both client and server during digital communication. It enhances security, especially in B2B communications, but should not be mistaken for…lnkd.in/gGi5CnwY lnkd.in/gwPhJBAz
English